By Andrew Jeong
SEOUL--North Korean hackers have targeted at least six
pharmaceutical companies in the U.S., the U.K. and South Korea
working on Covid-19 treatments, according to people familiar with
the matter, as the regime seeks sensitive information it could sell
or weaponize.
The firms include previously unreported targets in the U.S.:
Johnson & Johnson and Maryland-based Novavax Inc., which are
both working on experimental vaccines, the people said. The list
also includes three South Korean companies with Covid-19 drugs in
earlier clinical trials, Genexine Inc., Shin Poong Pharmaceutical
Co. and Celltrion Inc., they added.
North Korea had also tried infiltrating U.K.-based AstraZeneca
PLC, whose vaccine co-developed with the University of Oxford, has
been shown to be as much as 90% effective and is seeking emergency
approval, the people said. On Friday, Reuters reported that
suspected North Korean hackers had tried to break into the systems
of AstraZeneca, citing unnamed sources.
It wasn't known whether the hackers succeeded in swiping useful
information. But North Korea has coordinated attacks on the six
companies since August, the people said.
The attacks contained digital fingerprints used in other North
Korean campaigns against the State Department and South Korea's
unification ministry, such as the use of the same IP addresses, the
people said.
Shin Poong and Celltrion said they had received hacking attacks
but hadn't detected any damage, according to spokesmen from both
companies. The Shin Poong spokesman said the attacks were carried
out over email. The Celltrion spokesman said the hacking attacks
had accelerated sometime in the second half of 2020.
Johnson & Johnson remains vigilant against threats to its
data, a spokesman said. A Novavax spokeswoman said the company is
aware of the foreign threats and is working with "appropriate
government agencies and commercial cybersecurity experts." Genexine
is looking into the matter but hasn't found evidence of any hacking
attempt, a spokesman said.
AstraZeneca declined to comment.
North Korea, Russia, China and Iran have backed hackers seeking
to infiltrate drug companies working on Covid-19 treatments,
according to a U.K. assessment earlier this year. Without naming
any individual companies, Microsoft Corp. said Russia and North
Korea had targeted online accounts of at least seven firms
researching Covid-19 drugs and vaccines in the U.S., Canada,
France, India and South Korea, according to a report published last
month.
North Korea, despite a sanctions-strapped economy and limited
internet access, has become one of the world's most elite global
hacking outfits. The U.S. Justice Department has brought criminal
charges against a North Korean operative believed to be linked with
the 2014 Sony Pictures hack, 2016's cyber theft of $81 million from
Bangladesh's central bank and 2017's ransomware attack called
WannaCry.
Pyongyang, through its state media, has called the Justice
Department charges "preposterous falsehoods and highhandedness."
North Korea hasn't commented on any hacks involving Covid-19
vaccine developers.
Even if North Korea succeeded in pilfering Covid-19 treatment
details, the Kim Jong Un regime would have limited direct use for
it, Pyongyang watchers say. With rudimentary manufacturing
facilities and modest health-care infrastructure, it is doubtful
the country could produce any treatment from blueprints obtained
through cyber espionage, they say.
North Korea has made repeated claims that it has zero
coronavirus cases, having sealed off its borders and championed its
"anti-epidemic" work for months. On its state-run Korean Central
News Agency, Pyongyang in May mentioned a Covid-19 vaccine under
development by its public health ministry. But no further updates
have been provided.
A more likely North Korean use for stolen intelligence on
Covid-19 vaccines would be to sell it to a third-party drugmaker,
likely in China, said Robert Potter, head of Internet 2.0, a
cybersecurity company based in Canberra, Australia, who monitors
Pyongyang's hacking behavior.
Another option, Mr. Potter added, would be to leverage knowledge
of the targeted companies' networks from the attacks to demand
payouts in return for restoring access to encrypted files--a
ransomware attack--or crash a company's website.
North Korea remains a significant threat to Covid-19 drugmakers,
the State Department said on Tuesday in response to an inquiry
about Pyongyang's recent suspected attacks against drugmakers
developing Covid-19 treatments.
"It is vital for governments, network defenders, and the public
to stay vigilant and to work together to mitigate the cyber threat
posed by North Korea," the State Department said.
The group suspected of being behind the North Korean effort
targeting coronavirus vaccine developers is a unit well-known in
global cybersecurity circles, according to people familiar with the
matter. The U.S. government has previously referred to the group as
"Kimsuky."
Since at least 2012, Kimsuky has largely focused on stealing
national security intelligence from U.S., Japanese, and South
Korean entities, according to the U.S. government. But the group
appears to have begun operations aimed at global pharmaceutical
companies this summer, as the rush for vaccines and drugs for the
coronavirus accelerated, according to the people familiar with the
matter.
For the Covid-19-related attacks, Kimsuky operatives attempted
to lure in victims with phishing tactics, those people said. The
hackers would pose as colleagues or trustworthy acquaintances by
creating fake email accounts, then send out messages with
benign-looking attachments or links. If the recipients clicked on
them, the hackers could gain access to their computers, and, thus,
user IDs or passwords, the people said.
The hackers had six companies listed either by name or with
abbreviations such as "jnj" for Johnson & Johnson, according to
one of the people and materials reviewed by The Wall Street
Journal. .
Seoul's spy agency said last week in a closed-door meeting with
South Korean lawmakers that it had foiled at least one attempted
attack on at least one local pharmaceutical company but didn't
elaborate, according to two legislators who attended the briefing.
No corporation was named, they said.
Write to Andrew Jeong at andrew.jeong@wsj.com
(END) Dow Jones Newswires
December 02, 2020 04:32 ET (09:32 GMT)
Copyright (c) 2020 Dow Jones & Company, Inc.
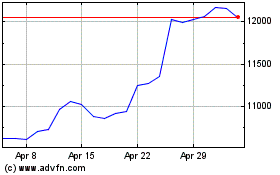
Astrazeneca (LSE:AZN)
Historical Stock Chart
From May 2024 to Jun 2024
Astrazeneca (LSE:AZN)
Historical Stock Chart
From Jun 2023 to Jun 2024
