By Jenny Strasburg in London and Dustin Volz in Washington
U.S. and U.K. government officials said a prominent state-backed
Russian hacking group is responsible for ongoing cyber espionage
against organizations involved in the development of coronavirus
vaccines and other healthcare-related work, showing escalating
security risks at a crucial time in the global response to the
pandemic.
The National Cyber Security Centre, part of the U.K.'s GCHQ
electronic-intelligence agency, and backed by U.S. and Canadian
security officials, said Thursday they jointly assessed the source
of the persistent hacking activity in several countries. The
targets, officials said, include governments, think tanks,
universities, private companies and other organizations working on
vaccine research and testing globally.
The attacks are designed to steal intellectual property related
to the response to Covid-19, the officials said. Efforts to develop
a vaccine have become an international arms race, with winners seen
as benefiting from access to treatments that would help improve
national health and economic stability. Those factors make the
scientific secrets behind vaccine development valuable.
They identified the hacking group as Russia-supported APT29,
which is also known as Cozy Bear. APT29 is widely viewed by
cybersecurity experts to be a sophisticated and prolific cyber unit
associated with Russian intelligence and has previously been linked
to attacks on the White House, the U.S. State Department, the
Democratic National Committee, and European governments.
"Throughout 2020, APT 29 has targeted various organizations
involved in Covid-19 vaccine development in Canada, the United
States and the United Kingdom, highly likely with the intention of
stealing information and intellectual property relating to the
development and testing of Covid-19 vaccines," British, American
and Canadian security agencies said jointly in a technical report
released Thursday.
The warning -- designed to help current and potential targets
boost defenses -- follows already stepped-up protection of
institutions involved in virus research, including vaccine
development. The Western allies' report said the Russian group has
shown some success gaining footholds in targeted computer networks
by exploiting software vulnerabilities and using spearphishing
attacks to compromise login credentials. But U.K. officials said
the attacks haven't thwarted vaccine-related work that they know
of.
The U.K. this year stepped up efforts to protect from
cyberattacks the University of Oxford and about a dozen
Universities battling the virus. Oxford is working with U.K.
drugmaker AstraZeneca PLC on a leading vaccine candidate that they
say could be ready by this autumn. An Oxford spokesman said the
university was working closely with Britain's National Cyber
Security Centre to ensure its research had the best cyber
protection. An AstraZeneca spokesman had no immediate comment about
the hacking warnings.
Anne Neuberger, director of cybersecurity at the National
Security Agency, said foreign actors were trying to take advantage
of the pandemic. "We encourage everyone to take this threat
seriously and apply the mitigations issued in the advisory," she
said.
The Kremlin refuted the allegations. Presidential spokesman,
Dmitry Peskov, told the official state news agency RIA Novosti that
Russia "will not accept such allegations, as well as regular
allegations of interference with the 2019 election."
There was no response from Russia's Federal Security Service,
nor from the Ministry of Digital Development, Communications and
Mass Media, which deals with cybersecurity.
Russia has mobilized its armed forces and top scientists to
develop its own coronavirus vaccine after President Vladimir Putin
demanded the country have one by this fall. The rush comes after
Russia initially waved over whether to impose lockdowns to curb the
spread of the virus.
The U.K. cyber center said it relied on multiple sources to
arrive at its conclusion that Russia was behind the activity. It
said the attackers used custom-built malware dubbed "WellMess" or
"WellMail" to target organizations across the globe working on
vaccine research. The NSA supported the attribution of the hacking
activity to Russia.
Canada's Communications Security Establishment, which is in
charge of cybercrime, said the attacks hindered the efforts of
health-care experts and researchers trying to fight the pandemic.
It urged Canadian hospitals and clinics to bolster protections
against possible attacks.
The U.S.-based cyber firm CrowdStrike accused the same Russian
group of hacking into the Democratic National Committee in the
lead-up to the 2016 election, saying the Russian group quietly
monitored email and chat conversations for months without
detection.
A separate hacking group linked to Russian military intelligence
was also accused of breaking into the DNC and implicated in
stealing and leaking emails as part of a broader cyber effort that
U.S. intelligence agencies later concluded was intended to harm
Democratic candidate Hillary Clinton's campaign. Russia has denied
the attacks.
Russia isn't the only country seeking to steal intellectual
property from foreign computer networks, say government and
private-security experts involved in responses. In the U.K.,
authorities noticed a significant uptick in malicious activity in
June, much of it they believed to be Russian, according to people
briefed on the activity.
In one case, attackers repeatedly tried to hack an entity
containing "Oxford" in its name but not part of the university,
according to the people. The entity was instead part of the U.K.'s
state-run health service. A spokeswoman for the National Health
Service declined to comment.
In May, U.S. officials issued a public alert accusing Chinese
hackers of targeting American universities and health-care
companies in a bid to steal intellectual property, saying that
intrusions could jeopardize medical research.
Trump administration officials have also said privately that
Iran or its proxies have been targeting similar types of facilities
using a relatively crude technique known as password spraying,
which attempts to compromise an organization by rapidly guessing
common account-login passwords.
Among Iran's recent targets, people familiar with the matter
have said, was the pharmaceutical company Gilead Sciences Inc.,
which has produced the antiviral drug remdesivir that was given
emergency-use authorization by the Food and Drug Administration as
a potential Covid-19 treatment.
Security experts also say they have seen several adversaries
seek to steal research related to the coronavirus and that such
attempts weren't surprising given the severity of the pandemic.
"Covid-19 is an existential threat to every government in the
world right now, so it's no surprise to see them leveraging their
cyber espionage capabilities to gather information on a cure," said
John Hultquist, director of intelligence analysis at U.S.-based
cyber firm FireEye and a longtime watcher of APT 29. "We have seen
the Russians as well as Chinese and Iranian actors target the
pharmaceutical and research space in an effort to gather
information on developing vaccines."
--Paul Vieira in Ottawa, Stu Woo in London and Ann Simmons in
Moscow contributed to this article.
Write to Jenny Strasburg at jenny.strasburg@wsj.com and Dustin
Volz at dustin.volz@wsj.com
(END) Dow Jones Newswires
July 16, 2020 13:03 ET (17:03 GMT)
Copyright (c) 2020 Dow Jones & Company, Inc.
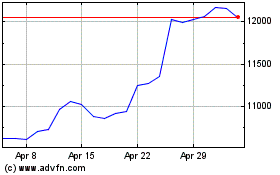
Astrazeneca (LSE:AZN)
Historical Stock Chart
From Aug 2024 to Sep 2024
Astrazeneca (LSE:AZN)
Historical Stock Chart
From Sep 2023 to Sep 2024
