By James Rundle
For many bosses and employees, there is a measure of relief in
returning to the office -- especially for those who have the
flexibility of continuing to work from home part of the time. But
for those teams working to protect their offices from hackers, the
new hybrid workplaces aren't nearly as welcome.
In a typical hybrid workplace, some employees will be in the
office, some will be working from home -- or spaces like coffee
shops and client headquarters -- and some will be cycling back and
forth. Devices, too, are moving in and out of the company network,
with employees bringing their laptops onto company networks and
then taking them back home -- where they're much more exposed to
hackers and can easily get infected with malware.
So, security chiefs are faced with the task of supporting a
constantly changing mix of office workers and remote workers, and
company and home devices. Whereas security teams were able to focus
on protecting the remote workforce during stay-at-home orders,
doing so when employees are in the office for certain days of the
week and at home for others will be difficult, says Rick McElroy,
principal cybersecurity strategist at VMware Inc.'s Security
Business Unit.
"It's hard to maintain a security staff that looks one way in
the data center or one way in an office, and then one way for
remote employees," he says.
Making things even worse: Security teams have been stretched
thin by the demands of the pandemic. For the past year, they've had
to make sure everyone is equipped to work from everywhere and can
use critical tools such as virtual meeting rooms. Things will only
get tighter now that businesses are hiring more workers and
launching into new projects they had put on hold during the
pandemic.
The issues associated with hybrid work follow a bruising year
for companies that were caught flat-footed by the coronavirus
pandemic, many of which had to move to a fully remote model for the
first time -- and often almost overnight. Hackers were quick to
realize that insecure home networks and a lack of security controls
typically found on corporate networks could work to their benefit.
The World Economic Forum estimates that cyberattacks jumped 238%
globally between February and April 2020.
Those attacks have continued to hammer corporate networks, and
in many cases target the technologies that companies implemented to
quickly provide for remote work, such as cloud services. A report
from Verizon Communications Inc., published in May 2021, found that
attacks against cloud-based email, remote desktop applications and
similar technologies designed to assist with remote work all
increased over 2020.
"I think many organizations probably rushed [the move to remote
work] and maybe haven't done it in the right way," says Phil
Venables, a vice president at Alphabet Inc.'s Google and the chief
information security officer of its cloud unit.
Now, the task gets even harder, as some workers return to the
office, some stay home and some do both. Here's a look at some of
the challenges businesses are facing as they make this transition
-- and how they're dealing with them.
Catching up on patches
One of the most basic problems security teams face is getting
their machines up to speed with the latest software patches. These
updates are released constantly to ensure that security
vulnerabilities aren't left open for hackers to exploit. If
companies miss just one of these, they can pay a high price in
terms of their vulnerability.
Now security chiefs are wary of the number of devices that may
have sat idle in offices for over a year -- turned off and unable
to download patches -- while employees have been absent, says Jadee
Hanson, chief information security officer at cybersecurity firm
Code42 Software Inc. And we're not talking about just one patch,
but potentially dozens or hundreds.
Of equal concern are devices that have been used by employees
during remote working. Because of the extended time away from the
office, users may have gotten negligent about installing patches,
leaving machines vulnerable when they reconnect to the corporate
network, says Ms. Hanson, a former security chief at Target
Corp.
"We push a lot of the patching stuff down to our end users,"
says Ms. Hanson. "But if they have not connected to the network in
a long period of time, we just don't know what's left unpatched out
there."
Keeping personal devices sequestered
When it comes to employees' work-from-home devices, it's not
just a lack of patches that's a problem. It's the fact that many
employees have gotten lax about security practices while stuck at
home for so long.
Email-security firm Tessian Ltd. published a survey of 2,000
workers in December, for instance, that found over half had
connected work devices to public wireless networks, which are often
regarded as insecure.
Similarly, a survey of over 3,000 workers published by AT&T
Inc. in March found that over half of respondents had used work
devices for personal business such as online banking and
downloading apps, and over a third had connected them to smart home
devices such as speakers.
Bringing those machines immediately into a company network,
where they might spread infections and give hackers a beachhead,
could be dangerous. Instead, the safest thing may be to have
personal devices log into a "quarantine network," says Mr. McElroy
of VMware.
Under this model, he says, user devices would connect to a
network that is separated from corporate systems until security
staff can ensure the devices are free of malware and appropriately
patched.
Security staff must also be vigilant for deeper threats that may
be waiting in employee devices -- such as malware that can stay
asleep for some time before it awakes and allows for further
infection.
Will quarantining work on a continuing basis? Quarantine
networks may be difficult to manage if workers are in and out of an
office frequently and have to continually quarantine devices,
rather than doing so once during a full office return, Ms. Hanson
of Code42 says.
"If somebody is doing 100% overnight, that might make sense" to
go with a quarantine, she says.
Removing the human factor
To some security chiefs, though, the hybrid model has so many
risks that we need to rethink the way we approach network safety
entirely. Imagine if we had hybrid work from the very beginning.
Would we really be treating cybersecurity the same way we do
now?
Not likely, the security chiefs say. The usual ways of training
employees to guard against hackers often don't work, they say, so
we should take that responsibility out of workers' hands -- and
create defenses that work behind the scenes as much as
possible.
"I think it's insane that we have basically said that we are
going to train people to filter phishing emails. We didn't train
people to filter spam emails, we just invented spam filters to take
the problem away," says Tim Sadler, Tessian's CEO.
So, what's the alternative? One possibility is a concept called
zero trust.
To understand zero trust, consider the traditional type of
network security. Usually, it focuses on building a perimeter
around the company network to keep intruders out -- think of
firewalls.
The problem is that hybrid work makes it very easy for intruders
to breach those outer defenses, because employees working at home
aren't as vigilant as they should be. And because traditional
security is focused on keeping hackers out, it's tough to stop them
once they get in -- so the bad guys can run wild.
Systems that are more vigilant use multifactor authentication:
Users might have to confirm their identity rigorously when they
sign in to the network, such as entering a password along with
something else, like responding to a message on their phone.
Zero trust takes that a step further. Even after users pass the
authentications, security checks constantly exchange information in
the background to verify whether users can access certain systems
or files, rather than assuming that because they passed through the
gateway, they should be allowed free movement.
By doing it this way, security staff assume hackers are already
inside a company's digital walls, and their job is to make it
difficult for them to wreak havoc. And, because these processes are
usually automated, zero trust doesn't have to rely on users to make
it all work.
At Microsoft Corp., CISO Bret Arsenault's team has built out a
zero-trust system to check employees' identities and devices at
every turn, including through multifactor authentication that can
include face, eye and fingerprint scans. Once the tools verify
Microsoft users, he says, they will push employees directly to
cloud-based apps such as the Office365 workplace suite, rather than
onto a corporate network.
Security veterans such as William O'Hern, the chief security
officer at AT&T, say that improving identity management and
other core zero-trust concepts can go a long way toward foiling
hackers, who often rely on compromised credentials such as breached
usernames and passwords. Around 61% of attacks during 2020 involved
this information to some degree, Verizon said in its May
report.
"If I had one thing to tell everyone to do, it would be to focus
on strong identity proofing, not only of individuals but of
[devices], too, " Mr. O'Hern says.
David Uberti and Steven Rosenbush contributed to this article.
Mr. Rundle is Wall Street Journal reporter in New York. He can be
reached at james.rundle@wsj.com .
(END) Dow Jones Newswires
June 08, 2021 11:14 ET (15:14 GMT)
Copyright (c) 2021 Dow Jones & Company, Inc.
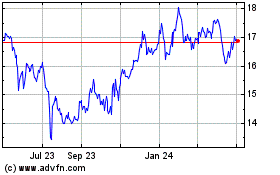
AT&T (NYSE:T)
Historical Stock Chart
From Aug 2024 to Sep 2024
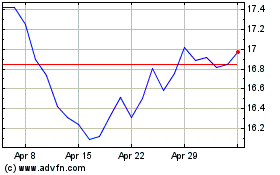
AT&T (NYSE:T)
Historical Stock Chart
From Sep 2023 to Sep 2024