Tenable Research Discovers Vulnerability in Zoom that Could Lead to Conference Hijacking
November 29 2018 - 9:00AM

Tenable®, Inc., the Cyber Exposure company, today announced that
its research team has discovered a serious vulnerability in Zoom’s
Desktop Conferencing Application [CVE-2018-15715] that would allow
a remote attacker or rogue meeting attendee to hijack screen
controls, impersonate meeting attendees via chat messages and kick
attendees out of meetings. The flaw exposes up to 750,000 companies
around the world that use Zoom to conduct day-to-day business.
As digital transformation surges and remote
workforces become increasingly common, conferencing services like
Zoom are nearly ubiquitous. In many ways, Zoom has become the new
conference room — used by organizations everywhere to host
confidential meetings, which can also be recorded and stored in the
cloud. Exploitation of this vulnerability could be extremely
disruptive and it poses serious reputational risk for organizations
that rely on the service for important conferences, such as
executive, client and prospect meetings.
A bad actor can leverage the vulnerability
to:
- Hijack screen control: Bypass screen
control permissions during remote attendee screen share to
completely control the victim’s desktop, allowing the attacker to
potentially download and execute malware.
- Spoof chat messages: Send chat messages that
impersonate other users in the meeting.
- Kick attendees out of the conference: Non-host
attendees can kick out and lock out other attendees.
“Conducting business in today’s digital economy
requires organizations to adopt new technology and services that
keep them connected. But every technology investment potentially
opens up new avenues of attack. This vulnerability is the perfect
example of the cyber attack surface that is expanded by seemingly
innocuous services, like Zoom,” said Renaud Deraison, co-founder
and chief technology officer, Tenable. “Tenable Research is focused
on finding vulnerabilities and collaborating with vendors to ensure
the technology we all rely on — as consumers and businesses — is
secure.”
Tenable Research disclosed the vulnerability to
Zoom following standard procedures outlined in its vulnerability
disclosure policy. The vulnerability affects Zoom version
4.1.33259.0925 for both macOS and Windows and Zoom version
2.4.129780.0915 for Ubuntu. Zoom was responsive and acted quickly
to release version 4.1.34814.1119 to fix the vulnerability in
Windows and version 4.1.34801.1116 for macOS. Users are urged to
ensure their Desktop Conferencing Application is up-to-date.
Tenable has released plugins to assess whether
organizations are exposed to this vulnerability. Click here for
details on the macOS plugins and here for Windows plugins.
For more information, read the Tenable Research
Advisory blog post.
About TenableTenable®, Inc. is
the Cyber Exposure company. Over 24,000 organizations around the
globe rely on Tenable to understand and reduce cyber risk. As the
creator of Nessus®, Tenable extended its expertise in
vulnerabilities to deliver the world’s first platform to see and
secure any digital asset on any computing platform. Tenable
customers include more than 50 percent of the Fortune 500, more
than 25 percent of the Global 2000 and large government agencies.
Learn more at www.tenable.com.
Contact Information:Cayla Baker
Tenable tenablepr@tenable.com 443-545-2102, x 1544
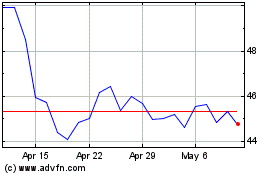
Tenable (NASDAQ:TENB)
Historical Stock Chart
From Mar 2024 to Apr 2024
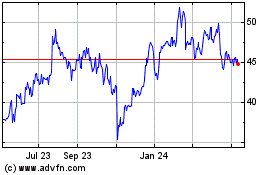
Tenable (NASDAQ:TENB)
Historical Stock Chart
From Apr 2023 to Apr 2024