By Jeff Stone
Multinational corporations are taking steps to more quickly
detect and report data breaches, in part to avoid steep penalties
under a sweeping set of regulations from the European Union.
The magic number: 72 hours.
The General Data Protection Regulation, which took effect in
May, requires firms that collect data about European Union citizens
to report a data breach to regulators within 72 hours of discovery.
Organizations that fail to comply with GDPR face fines of up to 4%
of their global revenue.
Other rules, such as a New York State Department of Financial
Services regulation that went into effect in 2017, also require
some firms to report breaches within 72 hours. But many more
companies need to comply with GDPR, and the penalties are much more
significant.
The fast turnaround creates a challenge for companies. "The
biggest challenge is knowing enough about the incident to actually
report it," says Jim Routh, chief security officer at Aetna Inc.
"We have to do some analysis to figure out what the scope or impact
is, and it's often days before we have that identified."
Aetna meets that challenge by informing regulators almost
immediately upon learning of a possible breach and then updating
them as the company learns more, Mr. Routh says.
Firms including Aetna, Cisco Systems Inc., Options Clearing
Corp. and others are working to speed up data-breach detection and
reporting procedures. Companies are rehearsing their breach
responses to identify who needs to be involved and what actions may
need to be accelerated. They're appointing incident-response
managers. And they're expediting the communication process by
prewriting news releases and scripts for the messages to notify
regulators and customers about a breach.
It's not like TV
The kinds of breaches that can happen vary dramatically, and so
do the responses. "We do a number of cyber-related exercises
assuming different scenarios based on what's happening," says Mark
Morrison, chief security officer at Options Clearing Corp., a
Chicago-based equities-derivatives clearing organization. "Not
everything is going to line up as you think it will. This isn't
like 'CSI: Cyber' on TV where they solve everything in an
hour."
Meeting a 72-hour deadline takes planning, says Michelle
Dennedy, Cisco's chief privacy officer. The company goes so far as
to track how long it takes designated executives to dial in to a
conference line to discuss a cybersecurity incident. It can take
just a few minutes or "well over an hour," depending on the number
of people involved, Ms. Dennedy says.
At Aetna, discovery of an attack triggers an incident record
describing the event as a phishing attack or another kind of hack,
says Mr. Routh. The record immediately goes via text message and
email to an on-call security team, which assigns oversight for the
incident to the internal security group most experienced with that
type of problem. That team then determines which business groups at
Aetna should be informed about the incident, says Mr. Routh.
"For example, if there's a news article that says there's a
major vulnerability in a commonly used mobile device, our job is to
figure out the impact of that for our clients," he says. "That
particular scenario involves consumers, the reputation of the brand
and potentially shareholders because of the financial impact. All
of that screams for escalation, and that report could go to the
board, CEO or audit committee."
Monitoring partners
It also has become commonplace for firms throughout the private
sector to use software to detect signs of a data breach at a
partner or customer to contain an attack before it spreads, says
Mr. Morrison, of Options Clearing Corp.
If OCC detects a breach originating outside the company, its
crisis-communications team and customer-service group draw from a
prewritten script to notify the external firm about the problem via
email or phone calls, says Mr. Morrison. OCC is installing secure
cloud-based communication services to contact customers should
OCC's own email be compromised, he says.
At Cisco, an incident-response manager coordinates the company's
actions. That manager organizes frequent phone conversations in
which Cisco executives in security, privacy, customer service,
technical support and other departments discuss hypothetical breach
scenarios, says Ms. Dennedy.
A typical phone rehearsal might be focused on a ransomware
attack or a system misconfiguration, which could result in
unprotected files, she says. In each practice session, Cisco tracks
how long it takes each executive to dial in to the conference line,
and how long it takes the group to decide what to do, she says.
"For a straightforward incident, like a ransomware attack where
you have all the information, you can figure out what to do within
an hour," Ms. Dennedy says. "If it's more complicated, where you
need to decide if we're going to start taking our products offline,
it can take days."
Cisco stepped up these exercises after recognizing that
cyberattacks and security regulations are a serious business risk,
she says.
Matt Palmer, senior director of cyberrisk management at Willis
Towers Watson PLC, says the risk-management firm has written
skeleton news releases for the communications department to fill
out in the event of a breach. The company also has outside
customer-service call centers standing by should Willis Towers
Watson customers learn of a breach and call seeking assistance, he
says.
"Worrying about these things once a breach happens is too late,"
he says.
Mr. Stone is a Wall Street Journal reporter in New York. He can
be reached at jeff.stone@wsj.com.
(END) Dow Jones Newswires
September 18, 2018 22:14 ET (02:14 GMT)
Copyright (c) 2018 Dow Jones & Company, Inc.
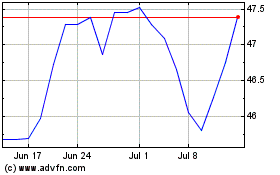
Cisco Systems (NASDAQ:CSCO)
Historical Stock Chart
From Aug 2024 to Sep 2024
Cisco Systems (NASDAQ:CSCO)
Historical Stock Chart
From Sep 2023 to Sep 2024
