Cryptocurrency Mining Presents New Threat to Business, says Check Point
November 13 2017 - 12:38PM

Check Point® Software Technologies Ltd. (NASDAQ:CHKP), a
leading provider of cyber-security solutions globally, revealed
that according to the company’s latest Global Threat Impact Index,
cryptocurrency mining was an increasingly prevalent form of malware
during October, as organizations were targeted with the CoinHive
variant.
Following up on recent Check Point research that found that
crypto-miners can fraudulently use up to 65% of an end-user’s total
CPU resources without the end-user’s approval, the CoinHive variant
entered the Index in 6th place in October. The malware is designed
to mine the Monero cryptocurrency when a user visits a web page,
without the user's approval. CoinHive implants JavaScript, which
then uses high levels of the end-users’ CPU, severely impact the
machine’s performance.
As in September, RoughTed and Locky remained the two most
prevalent threats. However, there was a new entry to the top
three: the ‘Seamless traffic redirector’ malware. This malware
silently redirects the victim to a malicious web page, leading to
infection by an exploit kit. Successfully infecting the target
allows the attacker to download additional malware.
Maya Horowitz, Threat Intelligence, Group Manager at Check Point
commented: “The emergence of Seamless and CoinHive once again
highlights the need for advanced threat prevention technologies in
securing networks against cyber-criminals. Crypto mining is a new,
silent, yet significant actor in the threat landscape, allowing
threat actors to make significant revenues while victims’ endpoints
and networks suffer from latency and decreased performance.”
October 2017’s Top 3 ‘Most Wanted’
Malware:*Arrows indicate change in rank compared to the
previous month.
- ↔ RoughTed - a purveyor of
ad-blocker aware malvertising responsible for a range of scams,
exploits, and malware. It can be used to attack any type of
platform and operating system, and utilizes ad-blocker bypassing
and fingerprinting in order to make sure it delivers the most
relevant attack.
- ↔ Locky - Ransomware that started its
distribution in February 2016, and spreads mainly via spam emails
containing a downloader disguised as a Word or Zip attachment and
then downloads and installs the malware that encrypts the user
files.
- ↑ Seamless - Traffic Distribution System
(TDS), which operates by silently redirecting the victim to a
malicious web page, leading to infection by an exploit kit.
Successful infection will allow the attacker to download additional
malware to the target
The most popular malware used to attack organizations’ mobile
assets saw one change from September, with Android ransomware
LeakerLocker appearing in 2nd place.
Top 3 ‘Most Wanted’ mobile malware:
- Triada - Modular Backdoor for Android that
grants super-user privileges to downloaded malware and helps it to
get embedded into system processes. Triada has also been seen
spoofing URLs loaded in the browser.
- LeakerLocker - Android ransomware that reads
personal user data, and then presents it to the user and threatens
to leak it online if ransom payments aren’t met.
- Lotoor - Hack tool that exploits
vulnerabilities on Android operating system to gain root privileges
on compromised mobile devices.
Check Point’s Global Threat Impact Index and its ThreatCloud Map
is powered by Check Point’s ThreatCloud intelligence, the largest
collaborative network to fight cybercrime which delivers threat
data and attack trends from a global network of threat sensors. The
ThreatCloud database holds over 250 million addresses analyzed for
bot discovery, more than 11 million malware signatures and over 5.5
million infected websites, and identifies millions of malware types
daily.
* The complete list of the top 10 malware families in October
can be found on the Check Point Blog:
http://blog.checkpoint.com/2017/11/13/octobers-wanted-malware-cryptocurrency-mining-presents-new-threat/
Check Point’s Threat Prevention Resources are available
at:
http://www.checkpoint.com/threat-prevention-resources/index.html
Follow Check Point
via:Twitter: http://www.twitter.com/checkpointswFacebook: https://www.facebook.com/checkpointsoftwareBlog:
http://blog.checkpoint.com
YouTube: http://www.youtube.com/user/CPGlobalLinkedIn:
https://www.linkedin.com/company/check-point-software-technologies
About Check Point Software Technologies
Ltd.Check Point Software Technologies Ltd.
(www.checkpoint.com) is a leading provider of cyber security
solutions to governments and corporate enterprises globally.
Its solutions protect customers from cyber-attacks with an industry
leading catch rate of malware, ransomware and other types of
attacks. Check Point offers a multilevel security architecture that
defends enterprises’ cloud, network and mobile device held
information, plus the most comprehensive and intuitive one point of
control security management system. Check Point protects over
100,000 organizations of all sizes.
INVESTOR CONTACT: Kip E.
Meintzer Check Point Software Technologies
+1.650.628.2040
ir@checkpoint.com
MEDIA CONTACT:Emilie Beneitez LefebvreCheck
Point Software TechnologiesTel: +44 (0) 7785 381
302press@checkpoint.com
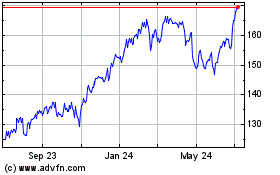
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From Aug 2024 to Sep 2024
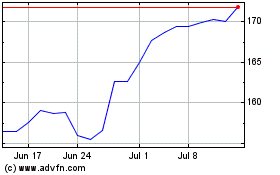
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From Sep 2023 to Sep 2024