Cloud and Mobile Deployments Are the Weakest Links in Enterprise Networks, shows Check Point’s 2019 Security Report
February 20 2019 - 9:00AM

CPX – Check Point® Software Technologies Ltd.
(NASDAQ: CHKP), a leading provider of cyber security solutions
globally, has published the third instalment of its 2019 Security
Report. It highlights how threat actors are increasingly
targeting the weakest, least protected points in an organization’s
IT infrastructure – their public cloud and mobile
deployments.
The third instalment of the 2019 Security Report reveals the key
cyber-attack trends used by criminals to target enterprise cloud
and mobile estates during 2018. It also reveals enterprise IT and
security teams’ key security concerns about these deployments.
Highlights of the third instalment include:
- 18% of organizations globally had a cloud security
incident in the past year: the most common incident
types were data leaks / breaches, account hijacks, and malware
infections.
- The top four public cloud security
threats: IT professionals rated misconfiguration of
cloud platforms, leading to data loss or breaches as the biggest
threat, cited by 62%; followed by unauthorized access to cloud
resources (55%); insecure interfaces and APIs (50%); hijacking of
accounts or data traffic (47%).
- 30% of IT professionals still consider security is the
responsibility of the cloud service
provider: this worrying finding
negates recommendations that cloud security should follow the
mutual responsibility model, in which security is shared by both
the cloud provider and the customer.
- 59% of IT professionals do not use mobile threat
defences: a majority of organizations have not
deployed mobile security solutions capable of detecting leading
threats including mobile malware, fake or malicious apps,
man-in-the-middle attacks and system vulnerabilities.
- Only 9% of IT professionals consider threats on mobile
a significant security risk: yet malware can
propagate from unprotected mobile devices to organizations’ cloud-
or on-premise networks, exploiting this weak link in enterprise
security defences.
“The third instalment of our 2019 Security Report shows just how
vulnerable organizations are to attacks targeting their cloud and
mobile estates, because there is a lack of awareness of the threats
they face and how to mitigate them. As nearly 20% or
organizations have experienced a cloud incident in the past year,
it’s clear that criminals are looking to exploit these security
gaps,” said Zohar Alon, Head of Cloud Product Line, Check Point
Software Technologies. “By reviewing and highlighting these
developments in the Report, organizations can get a better
understanding of the threats they face, and how they prevent them
impacting on their business.”
Check Point’s 2019 Security Report is based on data from Check
Point’s ThreatCloud intelligence, the largest collaborative network
for fighting cybercrime which delivers threat data and attack
trends from a global network of threat sensors; from Check Point’s
research investigations over the last 12 months; and on a brand new
survey of IT professionals and C-level executives that assesses
their preparedness for today’s threats. The report examines
the latest emerging threats against various industry sectors, and
gives a comprehensive overview of the trends observed in the
malware landscape, in emerging data breach vectors, and in
nation-state cyber-attacks. It also includes expert analysis
from Check Point’s thought leaders, to help organizations
understand and prepare themselves for today’s and tomorrow’s
complex fifth-generation cyber-attacks and threats.
For full report go to:
https://research.checkpoint.com/vol-3-2019-security-report/
Follow Check Point
via:Twitter: http://www.twitter.com/checkpointswFacebook: https://www.facebook.com/checkpointsoftwareBlog:
http://blog.checkpoint.com
YouTube: http://www.youtube.com/user/CPGlobalLinkedIn: https://www.linkedin.com/company/check-point-software-technologies
About Check Point Research Check Point Research
provides leading cyber threat intelligence to Check Point Software
customers and the greater intelligence community. The research team
collects and analyzes global cyber-attack data stored on
ThreatCloud to keep hackers at bay, while ensuring all Check Point
products are updated with the latest protections. The research team
consists of over 100 analysts and researchers cooperating with
other security vendors, law enforcement and various CERTs.
About Check Point Software Technologies
Ltd.Check Point Software Technologies Ltd.
(www.checkpoint.com) is a leading provider of cyber security
solutions to governments and corporate enterprises globally. Its
solutions protect customers from cyber-attacks with an industry
leading catch rate of malware, ransomware and other types of
attacks. Check Point offers a multilevel security architecture that
defends enterprises’ cloud, network and mobile device held
information, plus the most comprehensive and intuitive one point of
control security management system. Check Point protects over
100,000 organizations of all sizes.
INVESTOR
CONTACT:
MEDIA CONTACT:Kip E. Meintzer
Gil
MessingCheck Point Software Technologies
Check Point Software
Technologies+1.650.628.2040
+972.3753.4514ir@checkpoint.com
press@checkpoint.com
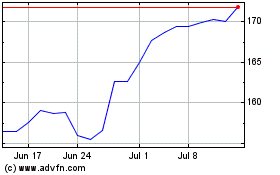
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From Mar 2024 to Apr 2024
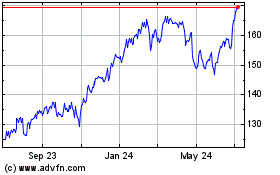
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From Apr 2023 to Apr 2024