RoughTed Malvertising Peaks in June, According to Check Point's Latest Global Threat Impact Index
July 17 2017 - 9:00AM

Check Point® Software Technologies Ltd. (NASDAQ:CHKP) has revealed
that 28% of organizations globally1 were affected by the
RoughTed malvertising campaign during June, according to the
company’s latest Global Threat Impact Index.
A large-scale malvertising campaign, RoughTed is used to deliver
links to malicious websites and payloads such as scams, adware,
exploit kits and ransomware. It began to spike in late May, before
continuing to peak in June, impacting organizations in 150
countries. The most affected organisations by RoughTed were in the
fields of communications, education, retail & wholesale. The
malvertising related infection rates have spiked in recent months
as attackers only have to compromise one online ad provider to
reach a wide range of victims with little effort as there is no
need to maintain a heavy distribution infrastructure for the
malware.
Second placed Fireball, which impacted 20% of organizations in
May, declined sharply and affected only 5% of businesses in June.
The Slammer worm was the third most common variant, impacting
4% of organizations.
The most prevalent malware highlight the wide range of attack
vectors and targets cyber-criminals are utilizing, impacting all
stages of the infection chain. In contrast to RoughTed,
Fireball takes over target browsers and turns them into zombies,
which it can then use for a wide range of actions including
dropping additional malware, or stealing valuable credentials,
while Slammer is a memory resistant worm that can cause denial of
service attacks.
This wide variety of attack vectors being utilized was reflected
throughout the top ten common malware, which included the
Cryptowall (4th) and Jaff (6th) ransomware, HackerDefender, a user
mode root kit used to hide files, and Zeus (9th) a banking
Trojan.
June 2017’s Top 3 ‘Most Wanted’ Malware:*The
arrows relate to the change in rank compared to the previous
month.
1. ↑
RoughTed: Large-scale malvertising used to deliver
various malicious websites and payloads such as scams, adware,
exploit kits and ransomware. It can be used to attack any type of
platform and operating system, and utilizes ad-blocker bypassing
and fingerprinting in order to make sure it delivers the most
relevant attack.2. ↓ Fireball:
Browser-hijacker that can be turned into a full-functioning
malware downloader. It is capable of executing any code on the
victim machines, resulting in a wide range of actions from stealing
credentials to dropping additional malware.3. ↑
Slammer: Memory resident worm targeted to attack Microsoft
SQL 2000. By propagating rapidly, the worm can cause a denial of
service condition on affected targets.
In mobile malware, Hummingbad was the most common form of
malware and was closely followed by Hiddad and Lootor:
Top 3 ‘Most Wanted’ mobile
malware:1. Hummingbad:
Android malware that establishes a persistent rootkit on the
device, installs fraudulent applications, and with slight
modifications could enable additional malicious activity such as
installing a key-logger, stealing credentials and bypassing
encrypted email containers used by
enterprises.2. Hiddad:
Android malware, which repackages legitimate apps and then released
them to a third-party store. Its main function is displaying ads,
however it is also able to gain access to key security details
built into the OS, allowing an attacker to obtain sensitive user
data.3. Lotoor: Hack tool
that exploits vulnerabilities on Android operating system in order
to gain root privileges on compromised mobile devices.
“Throughout
May and June organizations have been heavily focused on ensuring
that they are protected against ransomware, in response to the high
profile WannaCry and Petya attacks,” commented Maya Horowitz,
Threat Intelligence, Group Manager at Check Point. “However the
wide variety of attack vectors being utilized in this month’s index
serves as a reminder to organizations that they need to ensure
their security infrastructures robustly protect them against all
tactics and methods used by cyber-criminals. Organizations in every
industry sector need a multi-layered approach to their
cybersecurity. Our SandBlast™ Zero-Day Protection and Mobile
Threat Prevention, for example, protect against the widest range of
continually evolving attack types, and also protect against
zero-day malware variants.”
Check Point’s Global Threat Impact Index and its ThreatCloud Map
is powered by Check Point’s ThreatCloud intelligence, the largest
collaborative network to fight cybercrime which delivers threat
data and attack trends from a global network of threat sensors. The
ThreatCloud database holds over 250 million addresses analyzed for
bot discovery, more than 11 million malware signatures and over 5.5
million infected websites, and identifies millions of malware types
daily.
* The complete list of the top 10 malware families in June can
be found on the Check Point Blog:
http://blog.checkpoint.com/2017/07/17/junes-wanted-malware-roughted-malvertising-campaign-impacts-28-organizations/
Check Point’s Threat Prevention Resources are available
at:
http://www.checkpoint.com/threat-prevention-resources/index.html
Follow Check Point
via:Twitter: http://www.twitter.com/checkpointswFacebook: https://www.facebook.com/checkpointsoftwareBlog:
http://blog.checkpoint.com
YouTube: http://www.youtube.com/user/CPGlobalLinkedIn:
https://www.linkedin.com/company/check-point-software-technologies
____________________________1 Based on Check Point’s
ThreatCloud database of 250 million addresses analyzed
About Check Point Software Technologies
Ltd.
Check Point Software Technologies Ltd. (www.checkpoint.com) is
the largest pure-play security vendor globally, provides
industry-leading solutions, and protects customers from
cyberattacks with an unmatched catch rate of malware and other
types of attacks. Check Point offers a complete security
architecture defending enterprises’ networks to mobile devices, in
addition to the most comprehensive and intuitive security
management. Check Point protects over 100,000 organizations of all
sizes.
INVESTOR CONTACT:
Kip E. Meintzer
Check Point Software Technologies
+1.650.628.2040
ir@checkpoint.com
MEDIA CONTACT:
Emilie Beneitez Lefebvre
Check Point Software Technologies
Tel: +44 (0) 7785 381 302
press@checkpoint.com
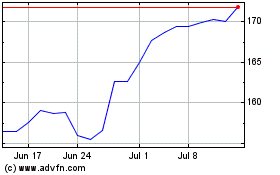
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From Mar 2024 to Apr 2024
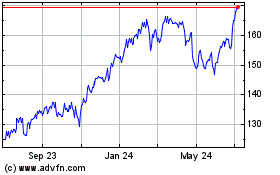
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From Apr 2023 to Apr 2024