Tenable Research Reveals Nearly Half of Organizations Use Strategic Vulnerability Assessment as Foundation of Cyber Defense
August 08 2018 - 12:00PM

Tenable®, Inc., the Cyber Exposure company, released The Cyber
Defender Strategies Report today that uses data science against
real-world telemetry data to analyze how 2,100 organizations are
assessing their exposure to vulnerabilities, a critical component
to improving overall cybersecurity posture. The report shows that
nearly 48 percent of organizations globally have embraced strategic
vulnerability assessment -- defined as mature or moderately mature
programs that include targeted and tailored scanning and
prioritizing computing resources based on business criticality --
as a foundational element of their cyber defense and a critical
step toward reducing risk. Of those organizations, however, only
five percent display the highest degree of maturity, with
comprehensive asset coverage as a cornerstone of their programs. On
the other end of the spectrum, 33 percent of organizations take a
minimalistic approach to vulnerability assessments, doing the bare
minimum as required by compliance mandates and increasing the risk
of a business-impacting cyber event.
Tenable’s last report, “Quantifying the Attacker’s First-Mover
Advantage,” revealed that attackers generally have a median
seven-day window of opportunity to exploit a known vulnerability,
before defenders have even determined they are vulnerable. The
resulting seven-day gap is directly related to how enterprises are
conducting vulnerability assessments -- the more strategic and
mature the approach, the smaller the gap is likely to be and the
lesser the risk to the business.
“In the not too distant future, there will be two types of
organizations -- those who rise to the challenge of reducing cyber
risk and those who fail to adapt to a constantly evolving and
accelerating threat landscape in modern computing environments,”
said Tom Parsons, senior director of product management, Tenable.
“This research is a call to action for our industry to get serious
about giving the advantage back to cyber defenders, starting with
the rigorous and disciplined assessment of vulnerabilities as the
basis for mature vulnerability management and ultimately, Cyber
Exposure.”
Tenable Research analyzed telemetry data for over three months
from organizations in more than 60 different countries using data
science to identify distinct security maturity styles and strategic
insights which can help organizations manage, measure and
ultimately reduce cyber risk. The objective was to analyze and
ultimately help to improve how defenders are responding.
Key findings include:
|
|
• |
There are
four distinct strategies of vulnerability assessment: |
|
|
|
- The Minimalist executes bare minimum
vulnerability assessments as required by compliance mandates.
Thirty-three percent of organizations fall into
this category, running limited assessments on only selected assets.
That represents a lot of enterprises which are exposed to risk and
still have some work to do, with critical decisions to make on
which KPIs to improve first.
- The Surveyor conducts frequent broad-scope
vulnerability assessments, but with little authentication and
customization of scan templates. Nineteen percent of
organizations follow the Surveying style, placing them at
a low to medium maturity.
- The Investigator executes vulnerability
assessments with a high maturity, but only assesses selective
assets. Forty-three percent follow the
Investigative style, indicating a solid strategy based on a good
scan cadence, targeted scan templates, broad asset authentication
and prioritization. Considering the challenges involved in managing
vulnerabilities, securing buy-in from management, cooperating with
disparate business units such as IT operations, maintaining staff
and skills, and the complexities of scale, this is a great
achievement and provides a solid foundation upon which to mature
further.
- The Diligent represents the highest level of
maturity, achieving near-continuous visibility into where an asset
is secure or exposed and to what extent through high assessment
frequency. Only five percent of organizations fall
into this category, displaying comprehensive asset coverage,
targeted, customized assessments and tailoring scans as required by
use case.
|
|
|
• |
Across all
levels of maturity, organizations benefit from avoiding a
scattershot approach to vulnerability assessment and instead making
strategic decisions and employing more mature tactics such as
frequent, authenticated scans to improve the efficacy of
vulnerability assessment programs. |
For more information on the research, read the Tenable Research
blog post here,
https://www.tenable.com/blog/how-mature-are-your-cyber-defender-strategies.
Visit Tenable at Black Hat USA 2018 in Las Vegas (booth
404).
About TenableTenable®, Inc. is the Cyber
Exposure company. Over 24,000 organizations around the globe rely
on Tenable to understand and reduce cyber risk. As the creator of
Nessus®, Tenable extended its expertise in vulnerabilities to
deliver Tenable.io®, the world’s first platform to see and secure
any digital asset on any computing platform. Tenable customers
include 53 percent of the Fortune 500, 29 percent of the Global
2000 and large government agencies. Learn more at tenable.com.
Contact Information:Cayla Baker Tenable
tenablepr@tenable.com 443-545-2102, x 1544
A photo accompanying this announcement is available at
http://www.globenewswire.com/NewsRoom/AttachmentNg/808f4cdd-bfc6-4f7a-b4f6-9d30e2198a66
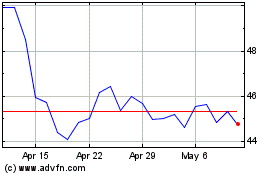
Tenable (NASDAQ:TENB)
Historical Stock Chart
From Mar 2024 to Apr 2024
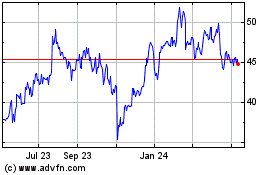
Tenable (NASDAQ:TENB)
Historical Stock Chart
From Apr 2023 to Apr 2024