CyberArk Research: Lack of Security Controls and Visibility Into User Activity Continue to Put Organizations at Risk
November 02 2021 - 8:30AM
Business Wire
News summary:
- 80 percent of organizations report employee misuse or abuse of
access to business applications
- Nearly half of organizations said they have limited ability to
view user logs and audit user activity
- The average end-user has access to more than 10 business
applications, many of which contain high-value data
New research released today by CyberArk (NASDAQ: CYBR), the
global leader in Identity Security, reveals that organizations
continue to operate with limited visibility into user activity and
sessions associated with web applications, despite the ever-present
risk of insider threats and credential theft. While the adoption of
web applications has brought flexibility and increased
productivity, organizations often lag in implementing the security
controls necessary to mitigate risk of human error or malicious
intent.
This press release features multimedia. View
the full release here:
https://www.businesswire.com/news/home/20211102005728/en/
Across organizations, users have access
to high-value data in business applications (Graphic: Business
Wire)
The global survey of 900 enterprise security leaders found that
80 percent of organizations experienced employees misusing or
abusing access to business applications in the past year. This
comes as 48 percent of organizations surveyed said they have
limited ability to view user logs and audit user activity, leaving
a blind spot for catching potentially risky behavior in user
sessions.
The new research coincides with the general availability of the
first-of-its-kind CyberArk Identity Secure Web Sessions, a
cloud-based solution that enables organizations to record and
protect user web application sessions.
Consider financial, healthcare, marketing or developer web
applications that contain sensitive, high-value data like financial
records, customer or patient information or intellectual property.
Most security and compliance teams have limited resources,
visibility and control over how confidential data is being handled,
or what is being done during a user session.
According to the research, in 70 percent of organizations, the
average end-user has access to more than 10 business applications,
many of which contain high-value data – creating ample opportunity
for a malicious actor. To that end, the top-three high-value
applications that organizations were most concerned with protecting
against unauthorized access were IT service management apps such as
ServiceNow, cloud consoles such as Amazon Web Services, Azure and
Google Cloud Platform and marketing and sales enablement
applications such as Salesforce.
For many security teams, investigation into questionable user
activity represents a significant investment of time and drag on
thin resources, and must be balanced with other priorities such as
improving incident response and enforcing consistent controls
across applications to reduce threat of credential theft.
According to the research:
- More than half (54 percent) of organizations investigate user
activity stemming from security incidents or compliance at least
weekly vs. 34 percent of organizations that investigate
monthly
- Forty four percent of organizations said they need to enable
the same security controls across all applications amid disparate
built-in application controls
- Forty one percent of respondents said that better visibility
into user activity would enable them to identify the source of a
security incident more quickly
“Ensuring security and usability is key. As more high-value data
migrates to the cloud, organizations should make certain the proper
controls follow suit to manage risk accordingly while enabling
their workforce to operate without disruption,” said Gil Rapaport,
general manager, Access Management, CyberArk. “Today, any user can
have a certain level of privileged access, making it ever more
important that enterprises add security layers to protect the
entire workforce as part of a comprehensive Identity Security
strategy and Zero Trust framework.”
Secure Web Sessions Adds Layers of Security to High-Risk User
Activity
CyberArk Identity Secure Web Sessions helps enterprises gain
visibility into user activity within web-based applications
protected by CyberArk Workforce Identity and third-party Single
Sign-On (SSO) providers. Secure Web Sessions enables organizations
to:
- Record and search every click and data change made within a
protected app while maintaining a frictionless user experience
- Implement continuous monitoring and re-authentication, such as
when a user steps away from a device during a session, reducing
risk of abuse
- Protect web sessions from threats originating on the endpoint
and restrict data exfiltration actions, such as copying of data and
file downloads.
Additional Resources:
- Video: Secure Web Sessions Overview
- Free trial: Secure Web Sessions
- Website: Secure Web Sessions
About the Survey
Commissioned by CyberArk, this research is based on a Censuswide
survey of 900 security decision makers and leaders at medium to
enterprise-sized organizations in the United States, United
Kingdom, France, Germany, Australia and Singapore.
About CyberArk
CyberArk (NASDAQ: CYBR) is the global leader in Identity
Security. Centered on privileged access management, CyberArk
provides the most comprehensive security offering for any identity
– human or machine – across business applications, distributed
workforces, hybrid cloud workloads and throughout the DevOps
lifecycle. The world’s leading organizations trust CyberArk to help
secure their most critical assets. To learn more about CyberArk,
visit https://www.cyberark.com, read the CyberArk blogs or follow
on Twitter via @CyberArk, LinkedIn or Facebook.
View source
version on businesswire.com: https://www.businesswire.com/news/home/20211102005728/en/
Media Contacts: Jordan Fylonenko, CyberArk Email:
press@cyberark.com
Highwire PR Email: cyberark@highwirepr.com
Investor Relations: Erica Smith, CyberArk Phone: +1
617-630-6426 Email: ir@cyberark.com
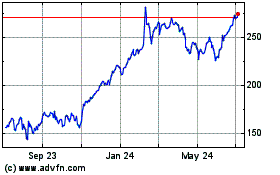
CyberArk Software (NASDAQ:CYBR)
Historical Stock Chart
From May 2024 to Jun 2024
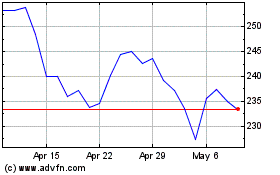
CyberArk Software (NASDAQ:CYBR)
Historical Stock Chart
From Jun 2023 to Jun 2024