Hancitor Makes First Appearance in Top Five "Most Wanted" Malware in Check Point’s February Global Threat Impact Index
March 13 2017 - 10:17AM

Check Point® Software Technologies Ltd. (NASDAQ:CHKP) has revealed
that the Hancitor downloader has surged into the top five "most
wanted" malware families worldwide for the first time, according to
the company’s February Global Threat Impact Index.
The downloader, that installs malicious payloads such as banking
trojans and ransomware on infected devices, climbed 22 places after
more than tripling its global impact in the past month. Hancitor,
also known as Chanitor, is usually delivered as a macro-enabled
Office document in phishing emails with "important" messages such
as voicemails, faxes or invoices.
The index ranked Kelihos, a botnet used in bitcoin theft, as the
most prevalent malware family overall, with 12% of organizations
globally impacted by it. Having been active since 2010, the
resilient Kelihos has evolved from a "pump and dump" spam campaign
into a botnet-for-hire, sending spam for anyone willing to pay.
Despite being taken down in 2011 and again a year later, it has
continued to resurface, culminating in the botnet and growing by
more than three times in just two days last August. Today, Kelihos
continues to grow as one of the most prominent distributors of spam
in the world, with over 300,000 infected machines, each capable of
sending more than 200,000 emails a day.
Overall, the top 3 malware families revealed that hackers were
using a wide range of attack vectors and tactics to target
businesses. These threats impact all steps of the infection chain,
including spam emails which are spread by botnets, and contain
downloaders that eventually place ransomware or a Trojan on the
victim’s machine.
The top three most common malware in February were Kelihos in
first, impacting 12% of organizations, followed by HackerDefender,
impacting 5% and Cryptowall which affected 4.5% of businesses
globally.
February 2017’s Top 3 "Most Wanted"
Malware:
- Kelihos - Botnet mainly involved in bitcoin
theft and spamming. It utilizes peer-to-peer communications,
enabling each individual node to act as a Command & Control
server.
- HackerDefender - User-mode rootkit for
Windows, can be used to hide files, processes and registry keys,
and also implements a backdoor and port redirector that operates
through TCP ports opened by existing services. This means it is not
possible to find the hidden backdoor through traditional
means.
- Cryptowall - Ransomware that started as a
Cryptolocker doppelgänger, but eventually surpassed it. After the
takedown of Cryptolocker, Cryptowall became one of the most
prominent ransomwares to date. Cryptowall is known for its use of
AES encryption and for conducting its C&C communications over
the Tor anonymous network. It is widely distributed via exploit
kits, malvertising and phishing campaigns.
In mobile malware, Hiddad moved up from third in January to
become the most active variant, followed by Hummingbad and last
month’s leader Triada in second and third place, respectively.
* The complete list of the top 10 malware families in February
can be found on the Check Point
Blog: http://blog.checkpoint.com/2017/03/13/check-point-february-top-malware/
Top 3 "Most Wanted" mobile malware:
- Hiddad - Android malware that repackages
legitimate apps and then releases them to a third-party store. Its
main function is displaying ads, however it is also able to gain
access to key security details built into the OS, allowing an
attacker to obtain sensitive user data.
- Hummingbad - Android malware that establishes
a persistent rootkit on the device, installs fraudulent
applications, and with slight modifications could enable additional
malicious activity such as installing a key-logger, stealing
credentials and bypassing encrypted email containers used by
enterprises.
- Triada - Modular backdoor for Android, which
grants super-user privileges to download malware and helps it to
get embedded into system processes. Triada has also been seen
spoofing URLs loaded in the browser.
Nathan Shuchami, VP of Emerging Products at Check Point
commented: “The rapid growth in the use of some malware variants
grew during February, highlighting the challenges faced by IT
departments worldwide. It is imperative organizations are
sufficiently equipped to deal with the ever-increasing number of
threats by adopting advanced security systems across their entire
business network such as Check Point’s SandBlast™ Zero-Day
Protection and Mobile Threat Prevention.”
The ThreatCloud Map is powered by Check Point’s ThreatCloudTM
intelligence, the largest collaborative network to fight
cybercrime, which delivers threat data and attack trends from a
global network of threat sensors. The ThreatCloud database
holds over 250 million addresses analyzed for bot discovery, more
than 11 million malware signatures and over 5.5 million infected
websites, and identifies millions of malware types daily.
Check Point’s Threat Prevention Resources are available
at:
http://www.checkpoint.com/threat-prevention-resources/index.html
Follow Check Point
via:Twitter: http://www.twitter.com/checkpointswFacebook: https://www.facebook.com/checkpointsoftwareBlog:
http://blog.checkpoint.com
YouTube: http://www.youtube.com/user/CPGlobalLinkedIn:
https://www.linkedin.com/company/check-point-software-technologies
About Check Point Software Technologies
Ltd.Check Point Software Technologies Ltd.
(www.checkpoint.com) is the largest network cyber security vendor
globally, providing industry-leading solutions and protecting
customers from cyberattacks with an unmatched catch rate of malware
and other types of threats. Check Point offers a complete security
architecture defending enterprises – from networks to mobile
devices – in addition to the most comprehensive and intuitive
security management. Check Point protects over 100,000
organizations of all sizes.
INVESTOR CONTACT:
Kip E. Meintzer
Check Point Software Technologies
+1.650.628.2040
ir@checkpoint.com
MEDIA CONTACT:
Emilie Beneitez Lefebvre
Check Point Software Technologies
Tel: +44 (0) 7785 381 302
press@checkpoint.com
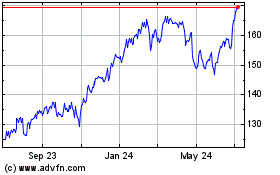
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From Aug 2024 to Sep 2024
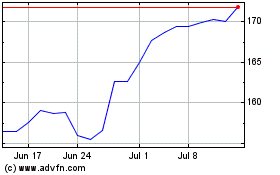
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From Sep 2023 to Sep 2024