Investigation Tracks Hospital Ransomware
Payments Through Bitcoin Accounts; Ransomware, Mobile, and Macro
Malware Threats Surge in Q2 2016
NEWS HIGHLIGHTS
- Intel Security tracks $100,000 in
targeted hospital ransomware payments through suspect Bitcoin
accounts.
- Intel Security survey shows healthcare
and manufacturing sectors are among the least prepared to prevent
data loss.
- More than 25 percent of companies
surveyed do not monitor sharing of or access to employee or
customer data.
- Only 37 percent of organizations
surveyed use endpoint monitoring of user activity and physical
media activity.
- Ninety percent of respondents have
cloud protection strategies, but only 12 percent have visibility
into data activity in the cloud.
- New mobile malware reaches highest
level recorded in Q2 2016; total mobile malware grows 151 percent
year over year.
- Total ransomware grows 128 percent year
over year; macro malware grows 106 percent.
Intel Security today released its McAfee Labs Threats Report:
September 2016, which assesses the growing ransomware threat to the
healthcare industry; surveys the “who and how” of data loss;
explains the practical application of machine learning in
cybersecurity; and details the growth of ransomware, mobile
malware, macro malware, and other threats in Q2 2016.
This Smart News Release features multimedia.
View the full release here:
http://www.businesswire.com/news/home/20160913006182/en/
Intel Security on Sept. 14, 2016,
released its "McAfee Labs Threats Report: September 2016," which
assesses the ransomware threat to the healthcare industry, among
other findings from 2016's second quarter. Following a rash of
targeted ransomware attacks on hospitals in early 2016, Intel
Security investigated the attacks, the ransomware networks behind
them, and the payment structures enabling cybercriminals to
monetize their activity. (Graphic: Business Wire)
Following a rash of targeted ransomware attacks upon hospitals
in early 2016, Intel Security investigated the attacks, the
ransomware networks behind them, and the payment structures
enabling cybercriminals to monetize their malicious activity. The
researchers identified nearly $100,000 in payments from hospital
ransomware victims to specific bitcoin accounts. While healthcare
is still clearly a small proportion of the overall ransomware
‘business,’ McAfee Labs expects a growing number of new industry
sectors to be targeted by the extensive networks launching such
attacks.
In the first half of 2016, McAfee researchers identified a
ransomware author and distributor who claimed to have received $121
million (BTC 189,813) in payments from ransomware operations
targeting a variety of sectors. Dark net discussion board
communications with network affiliates suggest that this particular
cybercrime actor had accumulated profits of $94 million during the
first six months of this year.
The scale of the operation is in line with research McAfee Labs
conducted with its Cyber Threat Alliance partners in late October
2015, when the group uncovered a ransomware operation using the
CryptoWall ransomware strain to extort nearly $325 million over the
course of two months.
The research team attributes the increased focus on hospitals to
such organizations’ reliance on legacy IT systems, medical devices
with weak or no security, third-party services that may be common
across multiple organizations and the need for hospitals to have
immediate access to information to deliver the best possible
patient care.
“As targets, hospitals represent an attractive combination of
relatively weak data security, complex environments and the urgent
need for access to data sources, sometimes in life or death
situations,” said Vincent Weafer, vice president for Intel
Security’s McAfee Labs. “The new revelations around the scale of
ransomware networks and the emerging focus on hospitals remind us
that the cybercrime economy has the capacity and motivation to
exploit new industry sectors.”
Intel Security 2016 Data Loss
Prevention Study
The Q2 report also features the results of a primary research
study assessing data loss incidents, including the types of data
leaking out, the ways data exits organizations, and the steps
organizations must take to take to improve the capabilities of data
loss prevention.
The survey found that retail and financial services
organizations have deployed the most extensive protections against
data loss, a finding McAfee Labs attributes to organizational
responses to the frequency of cyber-attacks and the value of the
data held by companies in these two sectors. Having sustained fewer
cyber-attacks historically, healthcare and manufacturing
enterprises have made fewer IT security investments and,
accordingly, possess the least comprehensive data protection
capabilities.
The weaker defenses in these two sectors are particularly
disturbing given that cybercriminals continue to shift their focus
from easily replaceable payment card numbers to less perishable
data such as personally identifiable information, personal health
records, intellectual property, and business confidential
information.
“Industry sectors such as healthcare and manufacturing present
both opportunity and motive for cybercriminals,” Weafer continued.
“Their relatively weak defensive capabilities coupled with highly
complex environments simplify breaches and subsequent data
exfiltration. The cybercriminals’ motive is ease of monetization,
with less risk. Corporations and individuals can easily cancel
stolen payment cards soon after a breach is discovered. But you
can’t change your most personal data or easily replace business
plans, contracts, and product designs.”
The research revealed that more than 25 percent of respondents
do not monitor the sharing of or access to sensitive employee or
customer information, and only 37 percent monitor the usage of
both, although this figure rises to almost 50 percent for the
largest organizations.
The survey results also show that nearly 40 percent of data
losses involve some kind of physical media, such as thumb drives,
but only 37 percent of organizations use endpoint monitoring of
user activity and physical media connections that could counter
such incidents. While 90 percent of respondents claim to have
implemented cloud protection strategies, only 12 percent are
confident in their visibility into the activity of their data in
the cloud.
Weafer concluded: “We will always face challenges as we work to
prevent the exfiltration of data, wherever it is stored and however
it is handled. But organizations can learn a great deal from this
study’s consistent theme of the value of greater visibility into
events and incidents across the enterprise, and the longer-term
value of the data drawn from this monitoring to construct stronger
security postures.”
Q2 2016 Threat Activity
In the second quarter of 2016, McAfee Labs’ global threat
intelligence network detected 316 new threats every minute, or more
than five every second, and registered notable surges in
ransomware, mobile malware, and macro malware growth:
- Ransomware. The 1.3 million new
ransomware samples in Q2 2016 were the highest ever recorded since
McAfee Labs began tracking this type of threat. Total ransomware
has increased 128 percent in the past year.
- Mobile malware. The nearly 2
million new mobile malware samples were the highest ever recorded
by McAfee Labs. Total mobile malware has grown 151 percent in the
past year.
- Macro malware. New downloader
Trojans such as Necurs and Dridex delivering Locky ransomware drove
a more than 200 percent increase in new macro malware in Q2.
- Mac OS malware. The diminished
activity from the OSX.Trojan.Gen adware family dropped new Mac OS
malware detections by 70 percent in the second quarter.
- Botnet activity. Wapomi, which
delivers worms and downloaders, increased by 8 percent in Q2. Last
quarter’s second most active botnet, Muieblackcat, which opens the
door to exploits, fell by 11 percent.
- Network Attacks. Assessing the
volume of network attacks in Q2, denial-of-service attacks gained
11 percent in the quarter to move into first place. Browser attacks
dropped by 8 percent from Q1. These most prominent attack types
were followed by brute force, SSL, DNS, Scan, backdoor, and
others.
For more information on the financial impact of ransomware
attacks on hospitals, please see our blog entitled “Healthcare
Organizations Must Consider the Financial Impact of Ransomware
Attacks.”
For more information on these focus topics, or more threat
landscape statistics for Q2 2016, visit www.mcafee.com for the full
report.
For guidance on how organizations can better protect their
enterprises from the threats detailed in this quarter’s report,
visit Enterprise Blog.
For online safety tips on how consumers can protect themselves
from the threats mentioned in this report, visit Consumer Safety
Tips Blog.
About McAfee Labs
McAfee Labs is the threat research division of Intel
Corporation’s Intel Security Group, and one of the world’s leading
sources for threat research, threat intelligence, and cybersecurity
thought leadership. The McAfee Labs team of researchers collects
threat data from millions of sensors across key threat
vectors—file, web, message, and network. It then performs
cross-vector threat correlation analysis and delivers real-time
threat intelligence to tightly integrated McAfee endpoint, content,
and network security products through its cloud-based McAfee Global
Threat Intelligence service. McAfee Labs also develops core threat
detection technologies—such as application profiling, and graylist
management—that are incorporated into the broadest security product
portfolio in the industry.
About Intel Security
Intel Security, with its McAfee product line, is dedicated to
making the digital world safer and more secure for everyone. Intel
Security is a division of Intel Corporation. Learn more at
www.intelsecurity.com.
Intel, the Intel logo, McAfee and the McAfee logo are trademarks
of Intel Corporation in the United States and other countries.
*Other names and brands may be claimed as the property of
others.
View source
version on businesswire.com: http://www.businesswire.com/news/home/20160913006182/en/
Intel SecurityChris Palm, 408-346-3089chris.palm@intel.comorZeno
Group, for Intel SecurityJanelle Dickerson,
650-801-0936janelle.dickerson@zenogroup.com
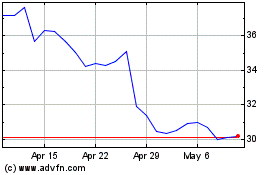
Intel (NASDAQ:INTC)
Historical Stock Chart
From Aug 2024 to Sep 2024
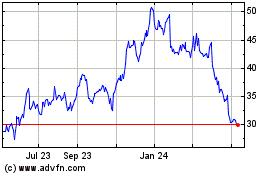
Intel (NASDAQ:INTC)
Historical Stock Chart
From Sep 2023 to Sep 2024