FBI Won't Share Hack With Apple -- WSJ
April 27 2016 - 3:04AM
Dow Jones News
By Devlin Barrett
The Federal Bureau of Investigation doesn't plan to tell Apple
Inc. how it cracked a San Bernardino, Calif., terrorist's phone,
said people familiar with the matter, leaving the company in the
dark on a security vulnerability on some iPhone models.
The FBI knows how to use the phone-hacking tool it bought to
open the iPhone 5c but doesn't specifically knows how it works,
allowing the tool to avoid a White House review, the people said,
The FBI plans to notify the White House of this conclusion in the
coming days, they added.
Any decision to not share details of the vulnerability with
Apple is likely to anger privacy advocates who contend the FBI's
approach to encryption weakens data security for many smartphone
and computer owners in order to preserve options for federal
investigators to open locked devices.
Asked for comment Wednesday, an Apple spokesman referred to
previous comments made by a lawyer for the company who said Apple
was confident the vulnerability the FBI apparently found would have
a short shelf life, and that the company would continue to make
security improvements to its phones.
At issue is a hacking tool FBI Director James Comey has
indicated cost the government more than $1 million and was used to
open the locked iPhone of Syed Rizwan Farook. Mr. Farook and his
wife killed 14 people and injured 22 others in a shooting rampage
in San Bernardino, Calif., in December before they were killed by
police
On Tuesday, Mr. Comey hinted at the FBI's plans regarding the
iPhone vulnerability at an appearance at Georgetown University. He
suggested that despite paying a high price for the hacking tool,
his agents may not know enough about how it works to begin the
broader White House review that would determine if the security gap
should be disclosed to Apple. Mr. Comey said the government was
"close" to deciding whether to start that review process.
The key question, the director said, is whether the FBI is
"aware of a vulnerability, or did we just buy a tool and don't have
sufficient knowledge of the vulnerability" to launch the White
House Vulnerability Equities Process, the policy it uses to decide
whether to disclose details of security flaws.
That process involves a number of government entities, including
intelligence agencies, who review security vulnerabilities in
software and then decide whether to alert the manufacturer or the
public about the weakness. The panel's decisions are based on such
factors as the number of people who may be vulnerable; the
likelihood of the vulnerability being exploited by malicious
hackers; and the value to national security and law enforcement of
keeping the security hole secret.
Obama administration officials have said the process leans
toward disclosing vulnerabilities so they can be patched, but some
privacy groups dispute that, saying the system is in fact weighted
in favor of national security and law-enforcement officials who
want to continue exploiting any software vulnerabilities for their
investigations.
Christopher Soghoian, chief technologist at the American Civil
Liberties Union, said the planned move by the FBI to avoid
notifying Apple shows that the government process for reviewing
software vulnerabilities "is riddled with loopholes."
"If the government can circumvent the process merely by buying
vulnerabilities, then the process becomes a farce," Mr. Soghoian
said. "The FBI is not interested in cybersecurity."
Two weeks ago, the Justice Department notified Apple of a
different, unrelated software vulnerability in iPhones and Mac
computers, said people familiar with the discussions, but the
company was already aware of the weakness and had deployed a fix
last year. That marked the first, and so far only, instance in
which the government has notified Apple of a security
vulnerability, these people said.
In his appearance on Tuesday, Mr. Comey said the FBI is working
to become "more predictive but less reactive" to hacking incidents
-- developing better relationships with victims and potential
victims so that companies can beef up their security measures and
be ready to respond quickly in the event of a hacking attack.
Write to Devlin Barrett at devlin.barrett@wsj.com
(END) Dow Jones Newswires
April 27, 2016 02:49 ET (06:49 GMT)
Copyright (c) 2016 Dow Jones & Company, Inc.
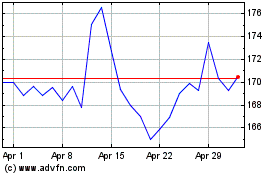
Apple (NASDAQ:AAPL)
Historical Stock Chart
From Apr 2024 to May 2024
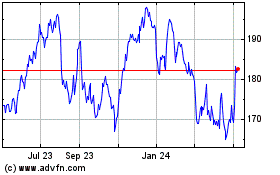
Apple (NASDAQ:AAPL)
Historical Stock Chart
From May 2023 to May 2024