April 2020’s Most Wanted Malware: Agent Tesla Remote Access Trojan Spreading Widely In COVID-19 Related Spam Campaigns
May 11 2020 - 6:00AM

Check Point Research, the Threat Intelligence arm of Check Point®
Software Technologies Ltd. (NASDAQ: CHKP), a leading provider of
cyber security solutions globally, has published its latest Global
Threat Index for April 2020. Researchers saw several COVID-19
related spam campaigns distributing a new variant of the Agent
Tesla remote access trojan, moving it up to 3rd place in the Index,
impacting 3% of organizations worldwide.
The new variant of Agent Tesla has been modified to steal Wi-Fi
passwords in addition to other information – such as Outlook email
credentials – from target PCs. During April, Agent Tesla was
distributed as an attachment in several malicious COVID-19 related
spam campaigns, which attempt to lure the victim into downloading
malicious files under the cover of providing interesting
information about the pandemic. One of these campaigns claimed to
be sent by the World Health Organization with the subject ‘URGENT
INFORMATION LETTER: FIRST HUMAN COVID-19 VACCINE TEST/RESULT
UPDATE.’ This highlights how hackers will exploit global news
events and public concerns to increase their attack success
rates.
The well-known banking trojan Dridex, which entered the Threat
Index top ten for the first time in March, had an even greater
impact in April. It moved up to 1st place in the index from 3rd
last month, impacting 4% of organizations worldwide. XMRig, March’s
most prevalent malware, dropped to second place.
“The Agent Tesla malspam campaigns we saw in April underline
just how agile cybercriminals can be when it comes to exploiting
news events and tricking unsuspecting victims to click on an
infected link,” said Maya Horowitz, Director, Threat Intelligence
& Research, Products at Check Point. “With both Agent Tesla and
Dridex in the top three of the threat index, criminals are focusing
on stealing users’ personal and business data and credentials so
that they can monetize them. So it’s essential that organizations
take a proactive and dynamic approach to user education, keeping
their staff informed of the latest tools and techniques,
particularly as more staff are now working from home.”
The research team also warns that “MVPower DVR Remote Code
Execution” remained the most common exploited vulnerability, though
its impact increased to cover 46% of organizations globally. This
was closely followed by “OpenSSL TLS DTLS Heartbeat Information
Disclosure” with a global impact of 41%, followed by “Command
Injection Over HTTP Payload” impacting 40% of organizations
worldwide.
Top malware families*The arrows relate to the
change in rank compared to the previous month.This month
Dridex rises to 1st place, impacting 4% of
organizations globally, followed by XMRig and
Agent Tesla impacting 4% and 3% of organizations
worldwide respectively.
- ↑ Dridex - Dridex is a Trojan that targets the
Windows platform and is reportedly downloaded via a spam email
attachment. Dridex contacts a remote server and sends information
about the infected system. It can also download and execute
arbitrary modules received from the remote server.
- ↓ XMRig - XMRig is an
open-source CPU mining software used for the mining process of the
Monero cryptocurrency, first seen in the wild in May 2017.
- ↑ Agent Tesla - Agent Tesla is an advanced RAT
functioning as a keylogger and information stealer, which is
capable of monitoring and collecting the victim’s keyboard input,
system keyboard, taking screenshots, and exfiltrating credentials
to a variety of software installed on a victim’s machine (including
Google Chrome, Mozilla Firefox and the Microsoft Outlook email
client).
Top exploited vulnerabilitiesThis month
“MVPower DVR Remote Code Execution” was the most
common exploited vulnerability, impacting 46% of organizations
globally, followed by “OpenSSL TLS DTLS Heartbeat
Information Disclosure” with a global impact of 41%. In
3rd place the “Command Injection Over HTTP
Payload” vulnerability impacted 40% of organizations
worldwide, mostly seen in attacks exploiting a zero-day
vulnerability in “DrayTek” routers and switch devices
(CVE-2020-8515).
- ↔ MVPower DVR Remote Code Execution – A remote
code execution vulnerability that exists in MVPower DVR devices. A
remote attacker can exploit this weakness to execute arbitrary code
in the affected router via a crafted request.
- ↑ OpenSSL TLS DTLS Heartbeat
Information Disclosure (CVE-2014-0160; CVE-2014-0346) - An
information disclosure vulnerability which exists in OpenSSL. The
vulnerability is due to an error when handling TLS/DTLS heartbeat
packets. An attacker can leverage this vulnerability to disclose
memory contents of a connected client or server.
- ↑ Command Injection Over HTTP Payload - A
remote attacker can exploit this issue by sending a specially
crafted request to the victim. Successful exploitation would allow
an attacker to execute arbitrary code on the target machine.
Top malware families - MobileThis month
xHelper is still holding 1st place as the most
prevalent mobile malware, followed by Lotoor and
AndroidBauts.
- xHelper - A malicious application seen in the
wild since March 2019, used for downloading other malicious apps
and display advertisement. The application is capable of hiding
itself from the user, and reinstalls itself if it is
uninstalled.
- Lotoor - Lotoor is a hacking tool which
exploits vulnerabilities on the Android operating system to gain
root privileges on compromised mobile devices.
- AndroidBauts - AndroidBauts is an Adware that
targets Android users. It exfiltrates IMEI, IMSI, GPS Location and
other device information and allows the installation of third-party
apps and shortcuts on mobile devices.
Check Point’s Global Threat Impact Index and its ThreatCloud Map
is powered by Check Point’s ThreatCloud intelligence, the largest
collaborative network to fight cybercrime which delivers threat
data and attack trends from a global network of threat sensors. The
ThreatCloud database inspects over 2.5 billion websites and 500
million files daily, and identifies more than 250 million malware
activities every day.
The complete list of the top 10 malware families in April can be
found on the Check Point Blog.
Follow Check Point Research via:Blog:
https://research.checkpoint.com/ Twitter:
https://twitter.com/_cpresearch_
About Check Point Research Check Point Research
provides leading cyber threat intelligence to Check Point Software
customers and the greater intelligence community. The research team
collects and analyzes global cyber-attack data stored on
ThreatCloud to keep hackers at bay, while ensuring all Check Point
products are updated with the latest protections. The research team
consists of over 100 analysts and researchers cooperating with
other security vendors, law enforcement and various CERTs.
About Check Point Software Technologies
Ltd.Check Point Software Technologies Ltd.
(www.checkpoint.com) is a leading provider of cyber security
solutions to governments and corporate enterprises globally. Check
Point’s solutions protect customers from 5th generation
cyber-attacks with an industry leading catch rate of malware,
ransomware and advanced targeted threats. Check Point offers a
multilevel security architecture, “Infinity Total
Protection with Gen V advanced threat prevention”, this
combined product architecture defends an enterprises’ cloud,
network and mobile devices. Check Point provides the most
comprehensive and intuitive one point of control security
management system. Check Point protects over 100,000 organizations
of all sizes.
| MEDIA CONTACT: |
|
INVESTOR CONTACT: |
| Emilie Beneitez Lefebvre |
|
Kip E. Meintzer |
| Check Point Software Technologies |
|
Check Point Software Technologies |
| press@checkpoint.com |
|
ir@us.checkpoint.com |
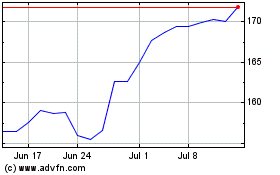
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From Aug 2024 to Sep 2024
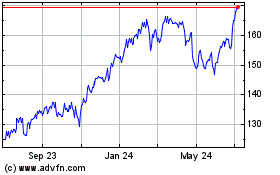
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From Sep 2023 to Sep 2024