Cyberattack wasn't intended to extort money, rather aimed to
cripple businesses
By Robert McMillan
This article is being republished as part of our daily
reproduction of WSJ.com articles that also appeared in the US print
edition of The Wall Street Journal (June 30, 2017).
This week's global virus outbreak that grounded airplanes in
Ukraine, slowed FedEx courier deliveries in Europe and disrupted
Maersk container ships around the world was devised simply to
damage businesses, not earn profits for the hackers behind it,
security experts now believe.
The latest attack was similar, yet more sophisticated than last
month's WannaCry virus, which also appeared as though designed to
extort money, security experts said.
The likelihood that a damaging attack on the Ukranian computer
system was disguised as ransomware is a disturbing revelation for
the world's corporate executives whose companies are at risk of
being collateral damage from such targeted attacks.
The software was coded to look like a variant of a known form of
ransomware -- malicious software called Petya that makes files
unreadable until the victim makes a $300 payment. But that appears
to have been a ruse: The virus's underlying software was different
from Petya and made it technically impossible for files to be
recovered, even by the attackers, researchers say.
"The attackers have no actual means of decrypting the files,"
said Juan Andrés Guerrero-Saade, a security researcher with
antivirus vendor Kaspersky Lab ZAO. "It's masquerading as a
ransomware."
The disguise slowed down the international response to the
outbreak by leading cyber-responders down investigative dead-ends,
said Lesley Carhart, a computer-security researcher who studied the
latest attack.
The Petya clone attack began Tuesday after hackers broke into
the servers belonging to Intellekt Servis, a little-known Ukranian
company that makes the country's most popular tax software,
security researchers say. The hackers then modified the M.E. Docs
software to include the malicious virus, which rapidly spread to
other corporate networks when companies installed a software
update.
Intellekt Servis, said there was no evidence supporting the idea
that its clients downloaded a corrupted update of its accounting
program. Still, the company said it was cooperating with police and
IT experts to determine how the virus spread.
The virus employed remarkably effective password-stealing
software along with attack code, allegedly stolen from the National
Security Agency, to worm through corporate networks. The alleged
NSA code "may have been used to compromise a few systems," but the
password-stealing tools led to the bulk of the computer infections,
said Charles Carmakal, a vice president at FireEye Inc.
An NSA spokeswoman didn't respond to an email seeking
comment.
M.E. Docs is the most popular software used to electronically
file tax forms with the Ukranian government, and it is widely used
by international companies doing business in Ukraine, said Hennadiy
Voytsitskyi, a partner with the law firm Baker & McKenzie
LLP.
After an M.E. Docs software update, a computer at Baker
McKenzie's Kiev office was seized with the ransomware Tuesday,
demanding the $300 payment in the digital currency bitcoin, Mr.
Voytsitskyi said. But the law firm didn't pay, he said. The
infected computer was isolated from the rest of the company and the
virus didn't spread, he said.
Other companies weren't so lucky. The world's largest
containership operator, A.P. Moeller-Maersk A/S, was forced to shut
down ports in the U.S., Europe and India after experiencing
widespread computer outages at its APM Terminals unit. Delivery
giant FedEx Corp. said a courier division in Europe was crippled by
the virus. Other victims included French construction giant Saint
Gobain and in the U.S., pharmaceutical giant Merck & Co. and
law firm DLA Piper.
Kaspersky, the Russian antivirus company, said that half of the
companies targeted by the infection were industrial companies in
industries such as oil and gas, transportation and electricity
production.
Within some of these companies, the virus spread like
wildfire.
On Tuesday, the fake ransomware infected 5,000 computers within
a matter of minutes at a large U.S. manufacturing company, said
David Kennedy, chief executive at security consultancy TrustedSec
LLC. When the company, which Mr. Kennedy declined to identify,
contacted TrustedSec for help on Tuesday, investigators initially
believed the company had been hit by ransomware spread via
email.
By the next day, they concluded that M.E. Docs was the source of
the attack, he said.
"When this company called, their entire infrastructure was shut
down. Gone," Mr. Kennedy said. Two days later the company was "at
about 50% capacity," he said.
Companies were already on edge after the WannaCry attack, which
began on May 12 and ultimately infected more than 200,000 computers
around the world by exploiting a bug in the Microsoft Windows
operating system. Security researchers have linked that attack to
North Korea.
Mr. Kennedy believes the newest attack, with its sophistication,
subterfuge, and its targeting of Ukranian systems, shows "signs of
nation-state hands in it."
The attack has netted its authors just under four bitcoins in
ransom payments to date, or roughly $10,000. Security experts say
this is a small amount for such a technically advanced attack.
The lawyer, Mr. Voytsitskyi, said he continues to feel the
effects of the outbreak even though his firm evaded a massive
disruption. Because some financial systems in Ukraine remained
offline Thursday, he was unable to pay for his lunch because the
restaurant's credit-card machine remained offline. "It's not just a
nuisance," he said. "It's more than that."
--David Gauthier-Villars contributed to this article.
Write to Robert McMillan at Robert.Mcmillan@wsj.com
(END) Dow Jones Newswires
June 30, 2017 02:47 ET (06:47 GMT)
Copyright (c) 2017 Dow Jones & Company, Inc.
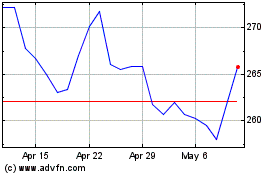
FedEx (NYSE:FDX)
Historical Stock Chart
From Mar 2024 to Apr 2024
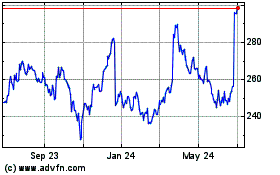
FedEx (NYSE:FDX)
Historical Stock Chart
From Apr 2023 to Apr 2024