Combination of New Targeted Behavioral
Analytics with Proven Privilege Management and Application Control
Capabilities Enables Organizations to Better Detect and Contain
Cyber Attacks
CyberArk (NASDAQ: CYBR), the company that protects organizations
from cyber attacks that have made their way inside the network
perimeter, today announced new behavioral analytics to block and
contain advanced threats targeting credential theft at the
endpoint. CyberArk Viewfinity, with enhanced threat protection
features, is now available as CyberArk Endpoint Privilege
Manager.
CyberArk also released new research from CyberArk Labs today
demonstrating security weaknesses in Windows operating systems that
allow attackers with local administrator rights to steal and use
encrypted service credentials to achieve lateral movement and full
domain compromise. This research supports a recent FBI flash alert
that recommends prioritizing credential protection, including
implementing least privilege and restricting local accounts, to
limit a threat actor’s ability to gain highly privileged account
access and move throughout a network.
CyberArk Endpoint Privilege Manager protects against advanced
threats that exploit privileged credentials by interlocking three
core capabilities: privilege management, application control and
new targeted credential theft detection and blocking to stop and
contain damaging attacks at the endpoint.
According to testing done by CyberArk Labs on more than 150,000
ransomware samples, the removal of local administrator rights,
combined with application control and greylisting, was 100 percent
effective in preventing this ransomware from encrypting files.
Despite recognition that the removal of local administrator rights
on the endpoint is an established best practice, a recent survey
highlighted that an alarming 62 percent of organizations have not
taken steps to remove them.1
“Even if malware disappeared tomorrow, attacks and breaches
would still occur. Organizations need to be thinking about long
term solutions, not just addressing the latest threat in the
headlines,” said Adrian Sanabria, senior security analyst, 451
Research. “With attackers getting better and better at evading
short-term prevention methods, organizations must also focus
efforts on reducing the endpoint attack surface and hardening,
including defending admin privileges against malicious abuse.”
Reducing the Attack Surface with Privilege Security on the
EndpointCyberArk Endpoint Privilege Manager now helps
organizations detect and block credential theft attempts by
malicious users and applications including Windows credentials,
remote access application credentials and those credentials stored
by popular web browsers such as corporate network and cloud
applications. CyberArk is also able to block hash harvesting at the
endpoint to prevent Pass-the-Hash, an attack leveraging stolen
credentials.
New targeted behavioral analytics are based on cyber threat
detection technology acquired from Cybertinel last year, combined
with continuous research from CyberArk Labs focused on identifying
common privileged account-based attack patterns and malware
behavior to further reduce the risk of emerging threats. These new
capabilities complement enterprise security best practices for
hardening the endpoint, including:
- Removing local administrator
credentials: CyberArk automates the removal of local
administrator rights to reduce risk while alleviating pressure on
help desk support, and minimizing impact on user activity by
seamlessly elevating privileges for authorized applications or
tasks.
- Enabling flexible application
control: CyberArk application control capabilities, featuring
automatic policy creation, allow organizations to prevent malicious
applications from executing and utilize greylisting to run unknown
applications in a restricted mode.
Additionally, by focusing specifically on detecting and
containing credential theft at the endpoint, security teams are
alerted on the specific threats that can pose the most danger to an
organization, allowing them to reduce “noise” and prioritize
remediation efforts accordingly.
“Instead of adding layer after layer of preventative endpoint
security controls on a weak foundation, CyberArk offers customers a
different, proactive approach – one that prioritizes securing
privilege across the organization and extends it to the endpoint,”
said Roy Adar, senior vice president, product management, CyberArk.
“We know advanced attacks start at the endpoint with attackers
going after credentials, so we combined powerful technology, deep
research and known best practices to stop them from advancing and
doing damage.”
With CyberArk Endpoint Privilege Manager as part of the CyberArk
Privileged Account Security Solution, customers gain a complete,
centralized solution to protect, monitor, detect, alert and respond
to privileged account activity. Additionally, the CyberArk
Discovery and Audit (DNA) tool v7.0 helps organizations broaden
their visibility into privileged accounts and privileged account
risks by extending discovery capabilities into public cloud
environments and uncovering credential-harvesting risks at the
endpoint.
AvailabilityCyberArk Endpoint Privilege Manager,
previously CyberArk Viewfinity, will be available in Q4 2016 via
direct sale or through CyberArk’s network of global channel
partners. The product is available as a single agent and part of
the CyberArk Privileged Account Security Solution. CyberArk
Endpoint Privilege Manager is available as a SaaS or on-premises
solution. For more information visit:
http://www.cyberark.com/endpoint-privilege-manager.
Additional Resources
- Video: Securing Privilege and
Containing Attacks on the Endpoint
- eBook: Achieving Security and
Productivity with Least Privilege and Application Control
1- CyberArk Global Advanced Threat Landscape Survey 2016
About CyberArkCyberArk is the only security company
focused on eliminating the most advanced cyber threats; those that
use insider privileges to attack the heart of the enterprise.
Dedicated to stopping attacks before they stop business, CyberArk
proactively secures against cyber threats before attacks can
escalate and do irreparable damage. The company is trusted by the
world’s leading companies – including 45 percent of the Fortune 100
– to protect their highest value information assets, infrastructure
and applications. A global company, CyberArk is headquartered in
Petach Tikvah, Israel, with U.S. headquarters located in Newton,
Mass. The company also has offices throughout EMEA and Asia Pacific
and Japan. To learn more about CyberArk, visit www.cyberark.com,
read the company blog, http://www.cyberark.com/blog/, follow
on Twitter @CyberArk or Facebook
at https://www.facebook.com/CyberArk.
Forward-Looking StatementsThis release may contain
forward-looking statements, which express the current beliefs and
expectations of CyberArk’s (the “Company”) management. In some
cases, forward-looking statements may be identified by terminology
such as “believe,” “may,” “estimate,” “continue,” “anticipate,”
“intend,” “should,” “plan,” “expect,” “predict,” “potential” or the
negative of these terms or other similar expressions. Such
statements involve a number of known and unknown risks and
uncertainties that could cause the Company’s future results,
performance or achievements to differ significantly from the
results, performance or achievements expressed or implied by such
forward-looking statements. Important factors that could cause or
contribute to such differences include risks relating to: changes
in the rapidly evolving cyber threat landscape; failure to
effectively manage growth; near-term declines in the Company’s
operating and net profit margins and its revenue growth rate; real
or perceived shortcomings, defects or vulnerabilities in the
Company’s solutions or internal network system, or the failure of
the Company’s customers or channel partners to correctly implement
the Company’s solutions; fluctuations in quarterly results of
operations; the inability to acquire new customers or sell
additional products and services to existing customers; competition
from IT security vendors; the Company’s ability to successfully
integrate recent and or future acquisitions; and other factors
discussed under the heading “Risk Factors” in the Company’s most
recent annual report on Form 20-F filed with the Securities and
Exchange Commission. Forward-looking statements in this release are
made pursuant to the safe harbor provisions contained in the
Private Securities Litigation Reform Act of 1995. These
forward-looking statements are made only as of the date hereof, and
the Company undertakes no obligation to update or revise the
forward-looking statements, whether as a result of new information,
future events or otherwise.
Copyright © 2016 CyberArk Software. All Rights Reserved. All
other brand names, product names, or trademarks belong to their
respective holders.
View source
version on businesswire.com: http://www.businesswire.com/news/home/20161116005310/en/
Media Relations Contacts:fama PRBrian Merrill,
+1-617-986-5005cyberark@famapr.comorLiz Campbell, CyberArk,
+1-617-558-2191press@cyberark.comInvestor Relations
Contact:CyberArkErica Smith, +1 617-630-6426ir@cyberark.com
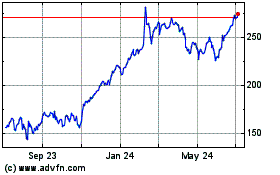
CyberArk Software (NASDAQ:CYBR)
Historical Stock Chart
From Aug 2024 to Sep 2024
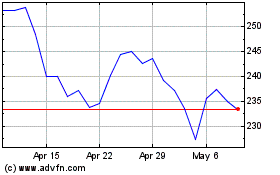
CyberArk Software (NASDAQ:CYBR)
Historical Stock Chart
From Sep 2023 to Sep 2024