McAfee Labs Report Reveals New Mobile App Collusion Threats
June 14 2016 - 12:41AM
Business Wire
Delayed Software Updates Enable
Cybercriminals to Exploit Mobile Apps; Pinkslipbot Trojan Returns
with New Capabilities
NEWS HIGHLIGHTS
- McAfee Labs identifies more than 5,000
versions of 21 consumer mobile apps containing colluding code
capable of data exfiltration, file inspection, fake SMS messages,
and other malicious activity
- New strain of Pinkslipbot Trojan
features anti-analysis and multi-layered encryption
- New ransomware grew 24%
quarter-over-quarter in Q1 2016
- Threat researchers saw a 17%
quarter-over-quarter increase in new mobile malware samples in Q1
2016
- Mac malware spiked Q1 primarily due to
an increase in VSearch adware
Intel Security today released its McAfee Labs Threats Report:
June 2016, which explains the dynamics of mobile app collusion,
where cybercriminals manipulate two or more apps to orchestrate
attacks capable of exfiltrating user data, inspecting files,
sending fake SMS messages, loading additional apps without user
consent, and sending user location information to control servers.
McAfee Labs has observed such behavior across more than 5,000
versions of 21 apps designed to provide useful user services such
as mobile video streaming, health monitoring, and travel planning.
Unfortunately, the failure of users to regularly implement
essential software updates to these 21 mobile apps raises the
possibility that older versions could be commandeered for malicious
activity.
Widely considered a theoretical threat for many years, colluding
mobile apps carry out harmful activity together by leveraging
interapp communication capabilities common to mobile operating
systems. These operating systems incorporate many techniques to
isolate apps in sandboxes, restrict their capabilities, and control
which permissions they have at a fairly granular level.
Unfortunately, mobile platforms also include fully documented ways
for apps to communicate with each other across sandbox boundaries.
Working together, colluding apps can leverage these interapp
communication capabilities for malicious purposes.
McAfee Labs has identified three types of threats that can
result from mobile app collusion:
- Information theft: An app with
access to sensitive or confidential information willingly or
unwillingly collaborates with one or more other apps to send
information outside the boundaries of the device
- Financial theft: An app sends
information to another app that can execute financial transactions
or make financial API calls to achieve similar objectives
- Service misuse: One app controls
a system service and receives information or commands from one or
more other apps to orchestrate a variety of malicious
activities.
Mobile app collusion requires at least one app with permission
to access the restricted information or service, one app without
that permission but with access outside the device, and the
capability to communicate with each other. Either app could be
collaborating on purpose or unintentionally due to accidental data
leakage or inclusion of a malicious library or software development
kit. Such apps may use a shared space (files readable by all) to
exchange information about granted privileges and to determine
which one is optimally positioned to serve as an entry point for
remote commands.
“Improved detection drives greater efforts at deception,” said
Vincent Weafer, vice president of Intel Security’s McAfee Labs
group. “It should not come as a surprise that adversaries have
responded to mobile security efforts with new threats that attempt
to hide in plain sight. Our goal is to make it increasingly harder
for malicious apps to gain a foothold on our personal devices,
developing smarter tools and techniques to detect colluding mobile
apps.”
The McAfee Labs report discusses forward-looking research to
create tools, initially used by threat researchers manually but
eventually to be automated, to detect colluding mobile apps. Once
identified, colluding apps may be blocked using mobile security
technology. The report suggests a variety of user approaches to
minimize mobile app collusion, including downloading mobile apps
only from trusted sources, avoiding apps with embedded advertising,
not “jailbreaking” mobile devices, and most importantly, always
keeping operating system and app software up-to-date.
For online safety tips on how consumers can protect themselves
from the threats mentioned in this report, visit Consumer Safety
Tips Blog.
This quarter’s report also documents the return of the
W32/Pinkslipbot Trojan (also known as Qakbot, Akbot, QBot). This
backdoor Trojan with worm-like abilities initially launched in 2007
and quickly earned a reputation for being a damaging, high-impact
malware family capable of stealing banking credentials, email
passwords, and digital certificates. The Pinkslipbot malware
reemerged in late 2015 with improved features such as anti-analysis
and multi-layered encryption abilities to thwart malware
researchers’ efforts to dissect and reverse engineer it. The report
also provides details about the Trojan’s self-update and data
exfiltration mechanism, and McAfee Labs’ effort to monitor
Pinkslipbot infections and credential theft in real-time.
Finally, McAfee Labs assesses the state of mainstream hashing
functions, and urges organizations to keep their systems up to date
with the latest, strongest hashing standards.
Q1 2016 Threat
Statistics
- Ransomware. New ransomware
samples rose 24% this quarter due to the continued entry of
relatively low-skilled criminals into the ransomware cybercrime
community. This trend is the result of widespread adoption of
exploit kits to deploy the malware.
- Mobile. New mobile malware
samples grew 17% quarter over quarter in Q1 2016. Total mobile
malware samples grew 23% quarter over quarter and 113% over the
last four quarters.
- Mac OS malware. Mac OS malware
grew quickly in Q1, primarily due to an increase in VSearch adware.
While the absolute number of Mac OS samples is still low, the total
number of samples has increased 68% quarter over quarter and 559%
over the last four quarters.
- Macro malware. Macro malware
continues on the growth trajectory begun in 2015 with a 42% quarter
over quarter increase in new macro malware samples. The new breed
of macro malware continues to attack corporate networks primarily
through sophisticated spam campaigns that leverage information
gathered through social engineering to appear legitimate.
- Gamut botnet. The Gamut botnet
became the most productive spam botnet in Q1, increasing its volume
nearly 50%. Prevalent spam campaigns offer get-rich-quick schemes
and knockoff pharmaceutical supplies. Kelihos, the most prolific
spamming botnet during Q4 2015 and a widespread malware
distributor, slipped to fourth place.
For more information on these focus topics, or more threat
landscape statistics for Q1 2016, visit
http:/www.mcafee.com/June2016ThreatsReport for the full report.
For guidance on how organizations can better protect their
enterprises from the threats detailed in this quarter’s report,
visit Enterprise Blog.
About McAfee Labs
McAfee Labs is the threat research division of Intel
Corporation’s Intel Security Group, and one of the world’s leading
sources for threat research, threat intelligence, and cybersecurity
thought leadership. The McAfee Labs team of researchers collects
threat data from millions of sensors across key threat
vectors—file, web, message, and network. It then performs
cross-vector threat correlation analysis and delivers real-time
threat intelligence to tightly integrated McAfee endpoint, content,
and network security products through its cloud-based McAfee Global
Threat Intelligence service. McAfee Labs also develops core threat
detection technologies—such as application profiling, and graylist
management—that are incorporated into the broadest security product
portfolio in the industry.
About Intel Security
McAfee Labs is now part of Intel Security. With its Security
Connected strategy, innovative approach to hardware-enhanced
security and unique McAfee Global Threat Intelligence, Intel
Security is intensively focused on developing proactive, proven
security solutions and services that protect systems, networks and
mobile devices for business and personal use around the world.
Intel Security is combining the experience and expertise of McAfee
with the innovation and proven performance of Intel to make
security an essential ingredient in every architecture and on every
computing platform. The mission of Intel Security is to give
everyone the confidence to live and work safety and securely in the
digital world. www.intelsecurity.com
Intel, the Intel logo, McAfee and the McAfee logo are trademarks
of Intel Corporation in the United States and other countries.
*Other names and brands may be claimed as the property of
others.
View source
version on businesswire.com: http://www.businesswire.com/news/home/20160613006581/en/
Intel SecurityChris Palm, 408-346-3089chris.palm@intel.comorZeno
Group, for Intel SecurityJanelle Dickerson,
650-801-0936janelle.dickerson@zenogroup.com
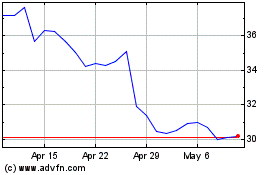
Intel (NASDAQ:INTC)
Historical Stock Chart
From Mar 2024 to Apr 2024
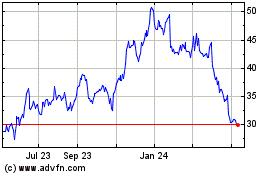
Intel (NASDAQ:INTC)
Historical Stock Chart
From Apr 2023 to Apr 2024