December’s Most Wanted Malware: Crypto-Miners Affect 55% of Businesses Worldwide
January 15 2018 - 9:00AM

Check Point® Software Technologies Ltd. (NASDAQ:CHKP), a
leading provider of cyber-security solutions globally, has revealed
a steep rise in crypto-mining malware during December 2017.
Check Point’s researchers found that crypto-miners had
impacted 55% of organizations globally during December, with ten
different variants in the top 100 list of malware, and two variants
in the top three. Using crypto-miners, cybercriminals hijack
the victim’s CPU or GPU power and existing resources to mine
cryptocurrency.
Furthermore, Check Point found that cryptocurrency miners have
intentionally been injected into some top websites, mostly media
streaming and file sharing services, without notifying the users.
While some of this activity is legal and legitimate, the tools can
be hacked to dominate more power and generate more revenue, using
as much as 65% of the end-users’ CPU power.
Maya Horowitz, Threat Intelligence Group Manager at Check Point
at Check Point commented: “Users are increasingly distrusting
pop-up and banner adverts and using ad-blocking software, so
websites are increasingly using crypto-miners as an alternative
revenue source – often without the knowledge or permission of
users, whose machines are being harnessed for mining.” Maya
continues: “As a result, threat actors are also using crypto-mining
tools to drain even more of users’ computing power for their own
gain, and it’s likely we’ll see this trend continue to rise over
the coming months.”
In December, the crypto-miner Coinhive replaced RoughTed as the
most prevalent threat, while the Rig ek exploit kit maintained its
position in second. Another new entry to the top ten, the
crypto-miner Cryptoloot is in third.
December 2017’s Top 3 ‘Most Wanted’
Malware:*The arrows relate to the change in rank compared
to the previous month.
- ↑ Coinhive - Crypto-Miner
designed to perform online mining of Monero cryptocurrency when a
user visits a web page without the user's approval.
- ↔ Rig ek - Rig delivers Exploits for Flash,
Java, Silverlight and Internet Explorer
- ↑Cryptoloot - Crypto-Miner, using the victim’s
CPU or GPU power and existing resources for crypto mining - adding
transactions to the blockchain and releasing new
currency.
Triada, a modular backdoor for Android, continues to be the most
popular malware used to attack organizations’ mobile estates
followed by the Lokibot and Lotoor.
December’s Top 3 ‘Most Wanted’ mobile
malware:
- Triada - Modular Backdoor for Android which
grants superuser privileges to downloaded malware.
- Lokibot - Android banking Trojan and
info-stealer, which can also turn into a ransomware that locks the
phone.
- Lotoor- Hack tool that exploits
vulnerabilities on Android operating system in order to gain root
privileges.
Check Point’s Global Threat Impact Index and its ThreatCloud Map
is powered by Check Point’s ThreatCloud intelligence, the largest
collaborative network to fight cybercrime which delivers threat
data and attack trends from a global network of threat sensors. The
ThreatCloud database holds over 250 million addresses analyzed for
bot discovery, more than 11 million malware signatures and over 5.5
million infected websites, and identifies millions of malware types
daily.
*The complete list of the top 10 malware families in December
can be found on the Check Point Blog:
http://blog.checkpoint.com/2018/01/15/decembers-wanted-malware-crypto-miners-affect-55-businesses-worldwide/
Check Point’s Threat Prevention Resources are available
at:
http://www.checkpoint.com/threat-prevention-resources/index.html
Follow Check Point
via:Twitter: http://www.twitter.com/checkpointswFacebook: https://www.facebook.com/checkpointsoftwareBlog:
http://blog.checkpoint.com
YouTube: http://www.youtube.com/user/CPGlobalLinkedIn:
https://www.linkedin.com/company/check-point-software-technologies
About Check Point Software Technologies
Ltd.Check Point Software Technologies Ltd.
(www.checkpoint.com) is a leading provider of cyber security
solutions to governments and corporate enterprises globally.
Its solutions protect customers from cyber-attacks with an industry
leading catch rate of malware, ransomware and other types of
attacks. Check Point offers a multilevel security architecture that
defends enterprises’ cloud, network and mobile device held
information, plus the most comprehensive and intuitive one point of
control security management system. Check Point protects over
100,000 organizations of all sizes.
INVESTOR CONTACT: Kip E. MeintzerCheck
Point Software
Technologies+1.650.628.2040 ir@checkpoint.com
MEDIA CONTACT:Emilie Beneitez LefebvreCheck
Point Software TechnologiesTel: +44 (0) 7785 381
302press@checkpoint.com
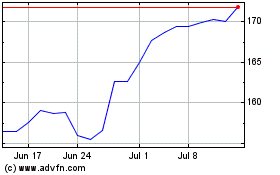
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From Mar 2024 to Apr 2024
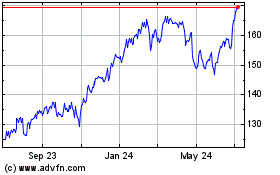
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From Apr 2023 to Apr 2024