Threat Actors Get Creative with Building Block Style Attacks, Finds HP
August 23 2023 - 9:00AM

HP Inc. (NYSE: HPQ) today issued its quarterly HP Wolf Security
Threat Insights Report, showing how threat actors are chaining
different combinations of attacks together like toy bricks to sneak
past detection tools.
By isolating threats that have evaded detection tools on PCs, HP
Wolf Security has specific1 insight into the latest techniques used
by cybercriminals in the fast-changing cybercrime landscape. To
date, HP Wolf Security customers have clicked on over 30 billion
email attachments, web pages, and downloaded files with no reported
breaches.
Based on data from millions of endpoints running HP Wolf
Security2, the researchers found:
- It’s playtime for cybercriminals using building block
style attacks: Attack chains are often formulaic, with
well-trodden paths to the payload. Yet creative QakBot campaigns
saw threat actors connecting different blocks together to create
unique infection chains. By switching up different file types and
techniques, they were able to bypass detection tools and security
policies. 32% of the QakBot infection chains analyzed by HP in Q2
were unique.
- Spot the difference – blogger or keylogger:
Attackers behind recent Aggah campaigns hosted malicious code
within popular blogging platform, Blogspot. By hiding the code in a
legitimate source, it makes it harder for defenders to tell if a
user is reading a blog or launching an attack. Threat actors then
use their knowledge of Windows systems to disable some anti-malware
capabilities on the users’ machine, execute XWorm or the AgentTesla
Remote Access Trojan (RAT), and steal sensitive information.
- Going against protocol: HP also identified
other Aggah attacks using a DNS TXT record query – typically used
to access simple information on domain names – to deliver the
AgentTesla RAT. Threat actors know the DNS protocol is not often
monitored or protected by security teams, making this attack
extremely hard to detect.
- Multi-lingual malware: A recent campaign
uses multiple programming language to avoid detection. Firstly, it
encrypts its payload using a crypter written in Go, disabling the
anti-malware scanning features that would usually detect it. The
attack then switches language to C++ to interact with the victim’s
operating system and run the .NET malware in memory – leaving
minimal traces on the PC.
Patrick Schläpfer, Senior Malware Analyst at the HP Wolf
Security threat research team, comments:
“Today’s attackers are becoming better organized and more
knowledgeable. They research and analyze operating system
internals, making it much easier for them to exploit the gaps. By
knowing which doors to push, they can navigate internal systems
with ease, using relatively simple techniques in very effective
ways – without sounding the alarm.”
The report details how cybercriminal groups are diversifying
attack methods to bypass security policies and detection tools. Key
findings include:
- Archives were the most popular malware delivery type for the
fifth quarter running, used in 44% of cases analyzed by HP.
- Q2 saw a 23% rise in HTML threats stopped by HP Wolf Security
compared to Q1.
- There was a 4%-point increase in executables from 14% to 18%
from Q1 to Q2, mainly caused by usage of the PDFpower.exe file,
which bundled software with a browser hijacking malware.
- HP noted a 6%-point drop in spreadsheet malware (19% to 13%) in
Q1 compared to Q4, as attackers move away from Office formats that
are more difficult to run macros in.
- At least 12% of email threats identified by HP Sure Click
bypassed one or more email gateway scanner in Q2.
- The top threat vectors in Q2 were email (79%) and browser
downloads (12%).
Dr. Ian Pratt, Global Head of Security for Personal Systems, HP
Inc., comments:
“While infection chains may vary, the methods of initiation
remain the same – it inevitably comes down to the user clicking on
something. Instead of trying to second guess the infection chain,
organizations should isolate and contain risky activities such as
opening email attachments, clicking on links, and browser
downloads.”
HP Wolf Security runs risky tasks in isolated, hardware-enforced
virtual machines running on the endpoint to protect users, without
impacting their productivity. It also captures detailed traces of
attempted infections. HP’s application isolation technology
mitigates threats that slip past other security tools and provides
unique insights into novel intrusion techniques and threat actor
behavior.
About the data
This data was anonymously gathered within HP Wolf Security
customer virtual machines from April-June
2023.
About HP
HP Inc. (NYSE: HPQ) is a global technology leader and creator of
solutions that enable people to bring their ideas to life and
connect to the things that matter most. Operating in more than 170
countries, HP delivers a wide range of innovative and sustainable
devices, services and subscriptions for personal computing,
printing, 3D printing, hybrid work, gaming, and more. For more
information, please visit: http://www.hp.com.
About HP Wolf Security
HP Wolf Security is a new breed of endpoint security. HP’s
portfolio of hardware-enforced security and endpoint-focused
security services are designed to help organizations safeguard PCs,
printers, and people from circling cyber predators. HP Wolf
Security provides comprehensive endpoint protection and resiliency
that starts at the hardware level and extends across software and
services. Visit
https://www.hp.com/uk-en/security/endpoint-security-solutions.html.
_________________
1 HP has specific insight into the latest cybercriminal
techniques because it analyzes real world malware samples in
micro-virtual machines (micro-VMs), capturing detailed traces of
attempted infections.2 HP Security is now HP Wolf Security.
Security features vary by platform, please see product data sheet
for details.
Media ContactVanessa Godsal, HP Media
Relationsvgodsal@hp.com
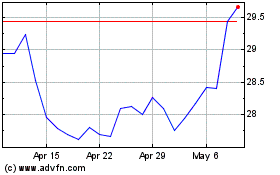
HP (NYSE:HPQ)
Historical Stock Chart
From Jun 2024 to Jul 2024
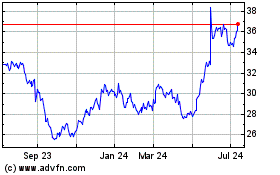
HP (NYSE:HPQ)
Historical Stock Chart
From Jul 2023 to Jul 2024