By David Uberti and Catherine Stupp
Companies that moved to remote work because of the coronavirus
now face another long-term question mark: security.
Stay-at-home workers have become targets for hackers, and they
are exposed in a way that company networks aren't. The use of
personal devices and internet connections, coupled with the anxiety
of balancing work with child care and other tasks at home, has
introduced a different set of weak points, says Tami Erwin, chief
executive of Verizon Communications Inc.'s business segment.
Home Wi-Fi networks are often not well-secured, relying on
weaker equipment, protected with insufficient passwords and shared
by different users and devices -- which may become infected with
malware that collects vital information. Home workers may also be
more vulnerable to phishing scams that open up access to company
networks, because they may feel less security-conscious outside the
office. And remote work has prompted many workplaces to adopt
applications such as teleconferencing tools that have their own
security weaknesses.
"You've almost got the perfect scenario where people are less
prepared, and bad guys have lots of time," says Ms. Erwin, whose
division sent about 20,000 employees home in response to the
pandemic, to join 10,000 more who already worked remotely.
In response to the shift, companies are urging employees to be
more wary about cyber hygiene, as well as beefing up their
abilities to investigate attacks from afar and turning to tools
that authenticate remote employees or detect threats to their
devices.
How many of the changes stick remains an open question as a
battered economy forces corporate chiefs to rethink long-term
spending plans and hiring practices. Still, the combination of
factors will likely accelerate several broader trends reshaping
cybersecurity.
Putting up a gateway
Virtual private networks, which keep data private even when it
is shared on public networks, have long been used to allow off-site
employees to access their workplace's perimeter defenses. Workers
log in using passwords or other authentication tools to set up shop
inside.
The huge numbers of employees now working remotely raises
challenges for companies that use VPNs. Some workers have never
used the technology before, and companies have to explain how to
operate it and remind workers to be vigilant about using it.
Another problem: bandwidth. Too many users on a VPN can damage
connection quality, so companies have moved to expand capacity to
meet the staggering new need.
Equifax Inc. faced just such a surge in users. Before the
coronavirus outbreak, around 10% to 20% of its employees worked
from home on a normal workday, Chief Technology Officer Bryson
Koehler says. But within one week's time in March, as lockdown
orders went into place around the world, that figure surpassed
90%.
The company expanded its VPN technology so all employees could
use it while working remotely, Mr. Koehler says, and a small team
of network specialists worked around the clock during the first
week to make sure the network ran smoothly.
British e-commerce company Made.com's VPN usage doubled after
lockdown orders went into place in March, so Chief Information
Security Officer Paul McCourt ditched physical keys employees used
to log in. The USB key was clunky and a potential security risk if
employees lost it, he says.
Now, Made.com employees access its VPN through the Okta Inc.
platform. The system enables workers to reach different workplace
applications by multifactor authentication, which requires users to
provide more than one way to verify identity.
Moving further into the cloud
Some companies, though, have sidestepped the VPN question
altogether. They are accelerating a move they had started making
before the pandemic hit -- switching to cloud-based services.
These platforms, such as online versions of the Microsoft 365
suite, host corporate applications on their own servers, easing the
pressure on company systems and offering employees more flexibility
to access software at home.
Fearing the shift to home offices and personal devices could
hamper developers' work, Microsoft Corp. Chief Information Security
Officer Bret Arsenault moved about 32,000 employees onto
cloud-based workstations within 48 hours in March. "That is the
beauty of the ability of the cloud to both surge and scale," Mr.
Arsenault says, adding that the shift will be permanent.
Thanks to that kind of migration, the cloud-computing market saw
37% year-over-year growth in the first quarter, according to
Synergy Research Group Inc., and the pandemic could accelerate the
trend.
"I believe this is an inflection point," says Sean Joyce, U.S.
and global cybersecurity and privacy leader at consulting firm
PricewaterhouseCoopers LLP.
There is a big trade-off to cloud services, though: They require
cybersecurity teams to put new technology in place to monitor their
workforce as closely as they could inside a company network.
Never trust, always verify
The pace of change could also help hasten a philosophical shift.
Many cybersecurity teams previously viewed cyber defenses as a
castle and moat, with firewalls and virtual private networks
monitoring for unwanted visitors who were trying to come inside --
and assuming everyone inside had been vetted.
Now, with many more remote workers beyond companies' outer
defenses, security professionals are focusing on securing
individual employees and their devices. This "zero trust" model
prioritizes verifying users' identities and devices at various
checkpoints with passwords and other authenticators, says Stephen
Schmidt, chief information security officer for Amazon.com Inc.'s
cloud-computing arm, Amazon Web Services.
At the same time, teams limit access to sensitive material and
use automated tools to scan devices and applications for abnormal
spikes in traffic or unusual queries. The architecture is designed
to detect attacks by people who have already made it inside
networks, including disgruntled current or former employees.
"We've been on a journey to a zero-trust network for a long
time," Mr. Schmidt says. "This really reinforced that that is
something that has to be completed."
Getting past passwords
Along with adding new checkpoints within the system, companies
are changing how you prove your identity at those points --
demanding a variety of identification methods instead of just
traditional passwords.
Lost or stolen credentials comprised the second-most common
cause of data breaches in 2019 after phishing emails, according to
Verizon, while the leading form of malware was password dumpers,
which extract credentials for crooks who seek access to company
networks.
Enter multifactor authentication, which often combines passwords
with other security measures, such as fingerprints or other
biometric identification. Microsoft, for one, said last year that
90% of its employees no longer use passwords.
Multifactor authentication has also been critical for Swiss
pharmaceutical firm Roche Holding AG as it secures its corporate
applications while employees work from home.
Since the pandemic began, the number of employees connecting to
the corporate network using a VPN roughly doubled, says Chief
Information Security Officer Vicky Imber. To prevent bottleneck
problems, Ms. Imber says, employees no longer need to log into VPNs
to access certain applications, such as Roche's enterprise-software
platform from Workday Inc. Instead, they use multifactor
authentication to securely use those apps outside the VPN.
But employees still need the VPN to use applications where they
access more-sensitive data such as financial information.
The shift away from passwords is a "no-brainer," says Frank
Dickson, program vice president at research firm IDC.
"If I'm going to give you the keys to the entire house...I want
to make sure you are who you say you are," Mr. Dickson says.
Mr. Uberti is a Wall Street Journal reporter based in New York,
and Ms. Stupp is a Wall Street Journal reporter based in Brussels.
They can be reached at david.uberti@wsj.com and
catherine.stupp@wsj.com.
(END) Dow Jones Newswires
November 17, 2020 17:23 ET (22:23 GMT)
Copyright (c) 2020 Dow Jones & Company, Inc.
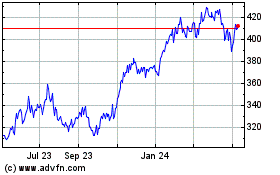
Microsoft (NASDAQ:MSFT)
Historical Stock Chart
From Aug 2024 to Sep 2024
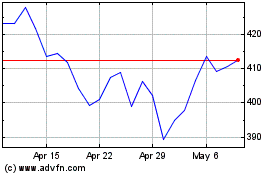
Microsoft (NASDAQ:MSFT)
Historical Stock Chart
From Sep 2023 to Sep 2024