Locky Ransomware Attackers Take Christmas Vacation, Shows Check Point Research
January 16 2017 - 9:00AM

Check Point® Software Technologies Ltd. (NASDAQ:CHKP) has revealed
that Locky ransomware attacks dramatically decreased during
December 2016. These findings are part of Check Point’s monthly
Global Threat Index, a ranking of the most prevalent malware
families attacking organizations’ networks.
Locky, which uses massive spam campaigns as a major distribution
vector, only surfaced in 2016 but has rapidly become one of the
most popular tools for cybercriminals, part of a growing trend for
ransomware cyberattacks that encrypt data on the target machine and
demand payment in return for decrypting it. In December, Check
Point recorded an 81% drop in the average number of Locky
infections per week, compared with the weekly averages of October
and November causing it to drop out of the top 10 global malware
families for the first time since June 2016.
Overall, Check Point tracked an 8% decrease in the number of
recognized malware attacks on organizations in December, which
could be attributed to a Christmas holiday slowdown. A similar
decrease was witnessed last December with 9% fewer attacks than the
previous months – with numbers returning to normal levels in
January.
Globally, Conficker remained the most prevalent malware type,
accounting for 10% of all known attacks during the period. It was
followed by Nemucod in second place with 5%, and Slammer with 4% of
the recognized attacks. Overall, the top ten malware families were
responsible for 42% of all known attacks.
- ↔ Conficker - Worm that allows remote
operations and malware download. The infected machine is controlled
by a botnet, which contacts its Command & Control server to
receive instructions.
- ↑ Nemucod - JavaScript or VBScript downloader
which is commonly used to download ransomware variants or other
malicious payloads.
- ↑ Slammer - Memory resident worm targeted to
attack Microsoft SQL 2000. By propagating rapidly, the worm can
cause a denial of service condition on affected targets.
Check Point’s research also revealed the most prevalent mobile
malware during December 2016, and once again attacks against
Android devices were significantly more common than iOS. The top
three mobile malware were:
- ↔ Hummingbad - Android
malware that establishes a persistent rootkit on the device,
installs fraudulent applications, and with slight modifications
could enable additional malicious activity such as installing a
key-logger, stealing credentials and bypassing encrypted email
containers used by enterprises.
- ↔ Triada – Modular Backdoor for Android which
grants superuser privileges to downloaded malware, as it helps it
to get embedded into system processes. Triada has also been seen
spoofing URLs loaded in the browser.
- ↔ Ztorg - Trojan that uses root privileges to
download and install applications on the mobile phone without the
user’s knowledge.
Nathan Shuchami, Head of Threat Prevention at Check Point said:
“The massive decrease in Locky attacks during December is part of a
wider trend which saw malware attacks decrease by around 8%
compared to the previous months. Organizations should be under no
illusions - this is not a reason to rest on their laurels. The most
likely cause genuinely is that cybercriminals have opted to take a
Christmas holiday too – perhaps to spend some of the fruits of
their labours. Ransomware remains a threat that businesses need to
take seriously into 2017.”
The ThreatCloud Map is powered by Check Point’s ThreatCloudTM
intelligence, the largest collaborative network to fight cybercrime
which delivers threat data and attack trends from a global network
of threat sensors. The ThreatCloud database holds over 250
million addresses analyzed for bot discovery, over 11 million
malware signatures and over 5.5 million infected websites, and
identifies millions of malware types daily.
* The complete list of the top 10 malware families in December
can be found on the Check Point Blog.
Check Point’s Threat Prevention Resources are available
at:
http://www.checkpoint.com/threat-prevention-resources/index.html.
Follow Check Point
via:Twitter: http://www.twitter.com/checkpointswFacebook: https://www.facebook.com/checkpointsoftwareBlog:
http://blog.checkpoint.com
YouTube: http://www.youtube.com/user/CPGlobal
About Check Point Software Technologies
Ltd.Check Point Software Technologies Ltd.
(www.checkpoint.com) is the largest pure-play security vendor
globally, provides industry-leading solutions, and protects
customers from cyberattacks with an unmatched catch rate of malware
and other types of attacks. Check Point offers a complete security
architecture defending enterprises’ networks to mobile devices, in
addition to the most comprehensive and intuitive security
management. Check Point protects over 100,000 organizations of all
sizes. At Check Point, we secure the future.
INVESTOR CONTACT:
Kip E. Meintzer
Check Point Software Technologies
+1.650.628.2040
ir@checkpoint.com
MEDIA CONTACT:
Emilie Beneitez Lefebvre
Check Point Software Technologies
Tel: +44 (0) 7785 381 302
press@checkpoint.com
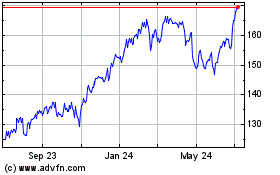
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From Aug 2024 to Sep 2024
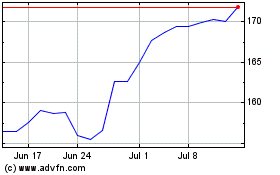
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From Sep 2023 to Sep 2024