Exploit Kits Continue Attacks, While Slammer Worm Resurfaces in Check Point’s ‘Most Wanted’ Malware
May 17 2017 - 9:00AM

Check Point® Software Technologies Ltd. (NASDAQ:CHKP) has detected
a continued increase in the number of cyber-attacks using Exploit
Kits globally, as Rig EK became the most prevalent form of attack
in the company’s April Global Threat Impact Index.
Exploit Kits are designed to discover and exploit
vulnerabilities on machines in order to download and execute
further malicious code. Until last month their usage had been in
decline globally, but March 2017 saw a surge in attacks using the
Rig and Terror Exploit Kits.
During the month Check Point also revealed a sudden resurgence
in use of the Slammer worm, which has seen it jump back into the
top three most prevalent malware families after a long hiatus. The
Slammer worm first emerged in 2003 and spread extremely rapidly.
It was developed to target Microsoft SQL 2000, and propagated
so quickly that it was able to cause a denial-of-service condition
on some affected targets. This is the second time the worm
has entered Check Point’s Global Threat Impact Index top ten in
recent months, showing how even decades-old malware can
successfully resurface.
The top three global malware families reveal a wide range of
attack vectors and targets, which impact all stages of the
infection chain. The most common malware in April were Rig EK
and HackerDefender, impacting 5% and 4.5% of organizations
worldwide respectively, while the Slammer worm came in third
impacting 4% of organizations.
April 2017’s Top 3 ‘Most Wanted’ Malware:*The
arrows relate to the change in rank compared to the previous
month.
1.
↑ Rig EK – Exploit Kit first
introduced in 2014. Rig delivers Exploits for Flash, Java,
Silverlight and Internet Explorer. The infection chain starts with
a redirection to a landing page that contains JavaScript that
checks for vulnerable plug-ins and delivers the
exploit. 2.
↓ HackerDefender – User-mode
Rootkit for Windows, can be used to hide files, processes and
registry keys, and also implements a backdoor and port redirector
that operates through TCP ports opened by existing services. This
means it is not possible to find the hidden backdoor through
traditional means. 3.
↑ Slammer – Memory resistant worm
targeted to attack Microsoft SQL 2000. By propagating rapidly, the
worm can cause a denial of service condition on affected
targets.
In mobile malware, the top two families remained the same as in
March, while Lotoor climbed back into the top three.
Top 3 ‘Most Wanted’ mobile
malware: 1. Hiddad
– Android malware which repackages legitimate apps and then
released them to a third-party store. Its main function is
displaying ads, however it is also able to gain access to key
security details built into the OS, allowing an attacker to obtain
sensitive user
data. 2. Hummingbad
– Android malware that establishes a persistent rootkit on the
device, installs fraudulent applications, and with slight
modifications could enable additional malicious activity such as
installing a key-logger, stealing credentials and bypassing
encrypted email containers used by
enterprises. 3. Lotoor
– Hack tool that exploits vulnerabilities on Android operating
system in order to gain root privileges on compromised mobile
devices. “Last
month we saw how attacks using Exploit Kits suddenly surged,
underlining the fact old but effective cyberthreats don’t vanish –
they often re-emerge, retooled with tweaks and updates making them
dangerous all over again. The fact the Slammer worm has now joined
two Exploit Kits in the top three underlines that point even
further,” said Nathan Shuchami, VP of Emerging Products at Check
Point. “Cybercriminals will always choose to adapt the tools they
already have at their disposal if possible, rather than developing
brand new ones, simply because it’s faster and more cost-effective.
It’s a vital warning to organizations in multiple sectors – you
must remain vigilant and deploy sophisticated security systems that
protect against a wide range of attack types.”
The ThreatCloud Map is powered by Check Point’s ThreatCloudTM
intelligence, the largest collaborative network to fight cybercrime
which delivers threat data and attack trends from a global network
of threat sensors. The ThreatCloud database holds over 250 million
addresses analyzed for bot discovery, more than 11 million malware
signatures and over 5.5 million infected websites, and identifies
millions of malware types daily.
* The complete list of the top 10 malware families in April can
be found on the Check Point Blog:
http://blog.checkpoint.com/2017/05/17/aprils-wanted-malware/
Check Point’s Threat Prevention Resources are available
at:
http://www.checkpoint.com/threat-prevention-resources/index.html
Follow Check Point
via:Twitter: http://www.twitter.com/checkpointswFacebook: https://www.facebook.com/checkpointsoftwareBlog:
http://blog.checkpoint.com
YouTube: http://www.youtube.com/user/CPGlobalLinkedIn:
https://www.linkedin.com/company/check-point-software-technologies
About Check Point Software Technologies
Ltd.Check Point Software Technologies Ltd.
(www.checkpoint.com) is the largest network cyber security vendor
globally, providing industry-leading solutions and protecting
customers from cyberattacks with an unmatched catch rate of malware
and other types of threats. Check Point offers a complete security
architecture defending enterprises – from networks to mobile
devices – in addition to the most comprehensive and intuitive
security management. Check Point protects over 100,000
organizations of all sizes.
INVESTOR CONTACT:
Kip E. Meintzer
Check Point Software Technologies
+1.650.628.2040
ir@checkpoint.com
MEDIA CONTACT:
Emilie Beneitez Lefebvre
Check Point Software Technologies
Tel: +44 (0) 7785 381 302
press@checkpoint.com
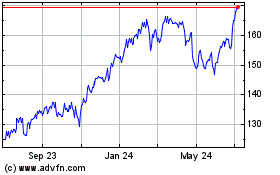
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From Aug 2024 to Sep 2024
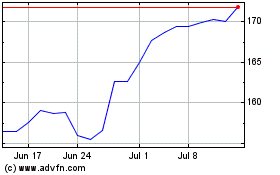
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From Sep 2023 to Sep 2024