Rapid7, Inc. (NASDAQ:RPD), a leading provider of analytics
solutions for security and IT operations, today released its first
threat intelligence report, an analysis of threats faced by
organizations in Q1 of 2017. Designed to provide a clear picture of
the threat landscape and share key learnings on threat types by
industry, the report also provides a glimpse into a day in the life
of an incident responder.
Rapid7 believes that collaboration and information sharing is
critical to solving today’s complex security challenges. With the
passage of the Cybersecurity Information Sharing Act (CISA) in late
2015, the private and public sectors were empowered to safely share
more information about cyber threats and work together to jointly
defend against attacks. This threat intelligence report reaffirms
Rapid7’s commitment to openly sharing security information and
supporting the industry in raising and addressing issues that
affect the cybersecurity community. This report follows the
February announcement of Rapid7 as an affiliate member of the Cyber
Threat Alliance (CTA), which describes itself as the industry’s
first group of cybersecurity practitioners from organizations that
work together in good faith to share threat information and improve
global defenses against advanced cyber adversaries.
“The CTA commends Rapid7 for producing this report. It provides
very useful insights into how the threat landscape is evolving. It
also demonstrates why proactive, robust information sharing is a
critical element of mitigating cyber vulnerabilities in such a
rapidly evolving threat landscape,” said Michael Daniel, president
of the CTA. “The CTA information sharing platform fulfills this
role by enabling the automated near-real time sharing of rich,
contextual cyber threat information. Automated information sharing,
paired with context, enables CTA Members like Rapid7 to more
efficiently deploy proactive defenses and provide more effective
incident response to their respective customers.”
The report leverages intelligence from Rapid7’s Insight
platform, Rapid7 Managed Services, Rapid7 Incident Response
engagements, and the Metasploit community. Rapid7 plans to issue
its threat analysis findings on a quarterly basis. The analysis was
led by Rapid7’s Rebekah Brown, threat intelligence lead, and Bob
Rudis, chief data scientist, and provides actionable guidance to
assist incident response teams to more quickly adapt to new and
emerging threats.
“Often, threat intelligence and data science reports present an
abundance of statistics that are inaccessible and difficult to
apply. Our goal with this report, and the ones to follow, is to
provide incident response teams and SOC analysts with distilled
learnings and practical, actionable guidance from the complex
wealth of data Rapid7 gathers continuously,” said Rudis.
Key takeaways from the Q1 2017 report include:
#1. More is less. Less is more. Reducing alert
fatigue should always be a goal, but there’s more to it: A better
signal-to-noise ratio means responders and analysts are more likely
to see meaningful trends. By observing the timing of alerts
generated, this Q1 analysis observed that attackers still heavily
rely on user interaction. For instance, on Monday holidays, alerts
dipped significantly, which our analysts attributed to a lack of
employees interacting with malicious emails, attachments, etc.
#2. You find what you are looking for. If you
design indicators based only on currently available information,
rather than seeking out additional intelligence or adding industry-
and company-specific context, the result will be low-quality
alerts. In other words: while most alerts are triggered from known,
malicious activity, the quality of these alerts is entirely
dependent on the established indicators.
#3. Advanced Persistent Threat (APT) is dead, long live
APT.Advanced Persistent Threats, Sophisticated
Adversaries, Nation State Actors ... there are many ways to
describe the types of sophisticated, targeted attacks many
organizations fear. Understanding an organization’s threat profile
can help determine whether or not these types of attackers should
be accounted for in the threat landscape. For organizations in
industries that align with nation state interests — government,
manufacturing, aerospace — sophisticated attack activity is alive
and kicking. For the most part, this analysis observed that
organizations outside those industries were not significantly
affected by highly targeted attacks.
#4. I feel the need, the need to Strut with
speed. While a 30-day patching cycle was once generally
effective, the Apache Struts vulnerability (CVE-2017-5638)
presented a strong case to reevaluate this traditional thinking.
Just days after the Apache Struts vulnerability was publicly
disclosed, our analysts began to detect mass-exploitation attempts.
Understanding the threat presented by new vulnerabilities, mapped
to specific threat profiles, can help to determine when something
needs to be prioritized.
For the full report, please visit:
https://www.rapid7.com/info/threat-report
To hear about this inaugural report, join authors Rebekah Brown
and Bob Rudis for a webcast on May 2, 2017:
https://information.rapid7.com/threat-intel-report-webcast-may.html
Threat intelligence analysis fuels Rapid7 understanding
of the attacker mindset
In addition to reporting out to the community, Rapid7’s threat
intelligence findings are leveraged to inform and help guide the
Company’s products and services. Strengthening Rapid7’s
understanding of the attacker mindset, the team’s analysis is used
to evaluate threats, understand the behavioral markers associated
with those threats, and adapt solutions to defend against them.
Rapid7 also uses threat intelligence to help prioritize its
handling of checks for newly disclosed vulnerabilities.
“Our goal is to build solutions that can quickly implement the
learnings of our intelligence findings to get ahead of attacks
before they’re reported in the wild,” said Brown. “For example,
once we understand the behavior of a threat group, we use
Metasploit to simulate that behavior and build detections for our
incident detection and response products and services — and that’s
hopefully before a real-world attack has occurred.”
The newly expanded Rapid7 Insight analytics platform allows for
the fast application of threat learnings across its offering,
including incident detection and response, vulnerability
management, operations, and application security solutions. The
cloud-based platform gives customers the ability to collect the
necessary data and leverage the appropriate analytics to detect,
prioritize, and stop threats. Specifically, InsightIDR customers
can subscribe to curated threat analysis and alerts through the
Company’s complimentary MDR Threat Intel service for live, advanced
detection.
About Rapid7Rapid7 (NASDAQ:RPD) is trusted by
IT and security professionals around the world to manage risk,
simplify modern IT complexity, and drive innovation. Rapid7
analytics transform today’s vast amounts of security and IT data
into the answers needed to securely develop and operate
sophisticated IT networks and applications. Rapid7 research,
technology, and services drive vulnerability management,
penetration testing, application security, incident detection and
response, and log management for more than 6,200 organizations
across more than 110 countries, including 38% of the Fortune 1000.
To learn more about Rapid7 or join our threat research, visit
www.rapid7.com.
Press contact:
Rachel E. Adam
Rapid7, Senior PR Manager
press@rapid7.com
(857) 415-4443
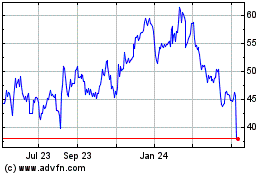
Rapid7 (NASDAQ:RPD)
Historical Stock Chart
From Aug 2024 to Sep 2024
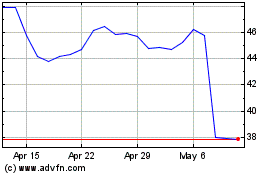
Rapid7 (NASDAQ:RPD)
Historical Stock Chart
From Sep 2023 to Sep 2024