Aluminum maker tests artificial intelligence to detect hacking
of its industrial equipment Aluminum maker tests using artificial
intelligence to secure industrial equipment
By Catherine Stupp
This article is being republished as part of our daily
reproduction of WSJ.com articles that also appeared in the U.S.
print edition of The Wall Street Journal (August 20, 2019).
Norsk Hydro ASA's investigation of a ransomware attack it
suffered in March has revealed new vulnerabilities, leading it to
test using artificial intelligence to secure its industrial
equipment.
The Norway-based aluminum company, whose business includes
mining, smelting and renewable-energy generation, also reorganized
its security team to better detect and respond to cyber
incidents.
Norsk Hydro is developing an AI tool to detect hackers as they
attempt to access its industrial equipment, Chief Information
Officer Jo De Vliegher said in an interview. The tool looks for
unusual activity that could signal hacking, such as frequent
password changes on devices. It then triggers an alarm to Norsk
Hydro's cybersecurity team.
"There are things that are obviously part of normal business,
unless they start to happen too frequently in too many sites," Mr.
De Vliegher said.
The ransomware, which Norsk Hydro identified as the LockerGoga
virus, brought down some operations after gaining access to the
company's corporate IT network. Norsk Hydro determined a few weeks
ago that the situation was stable, Mr. De Vliegher said. The
hackers didn't compromise industrial equipment, but they could
have, he said: "There weren't enough proper mechanisms in place to
stop the attack, had it come that far."
The attack has cost the company 550 million to 650 million
Norwegian kroner ($61 million to 72 million), a spokesman said.
An internal investigation revealed security holes that could
have allowed the virus to infect industrial equipment, Mr. De
Vliegher said. Its machines communicate with each other in ways the
security team hadn't known about, which could make them vulnerable
to attacks, he added.
The AI tool is designed to shore up those security gaps by
identifying areas where industrial equipment might be exposed to
hackers and monitoring for small changes over time. Human analysts
can't assess the huge amount of internet traffic on the company's
network, Mr. De Vliegher said.
His team set the tool to detect if multiple password changes are
made within one week to programmable logic controllers, industrial
computers that communicate with machines. Hackers often reset
passwords to take over accounts.
The security team is testing the AI tool but it hasn't been
rolled out yet.
Industrial companies operate in two technology spaces, combining
an IT environment for email and other routine business applications
with operational equipment, some of which runs constantly to
process materials or perform critical functions. Industrial
companies generally isolate such equipment from corporate IT
networks that are used for other business operations to avoid cyber
threats.
Norsk Hydro was surprised to discover that some of its
programmable logic controllers were connected to its IT
networks.
"We think a PLC is isolated, it can't get any commands from the
IT world, but then all of a sudden we see that there is a
connection," Mr. De Vliegher said.
Industrial companies are increasingly looking to AI to help them
prevent cyberattacks, said Rob McNutt, chief technology officer at
cybersecurity firm Forescout Technologies Inc.
AI can help protect factories, power plants and other critical
infrastructure sites that often lack safeguards, such as encrypted
devices, that are common in corporate networks, he said. Such
companies should instead set up additional lines of defense and AI
could help them identify suspicious activity, he said.
Mr. De Vliegher would like to expand Norsk Hydro's use of AI but
first needs to figure out how to train the tool on specific hacking
behavior.
"We need to think like hackers, so we also need to come up with
scenarios of what hackers could do," he said.
Norsk Hydro is also looking to hire three to five
cyber-automation specialists as it delves further into AI, Mr. De
Vliegher said. The new employees would operate the AI tool and
monitor areas where the company's industrial equipment could be
vulnerable. Some of the new hires will likely be based in Brazil
because the company has plants there and the country is home to
significant hacker activity, he said.
The internal investigation revealed that attackers first
infiltrated Norsk Hydro's system in December through an infected
email sent to an employee that appeared to come from a business
partner, referring to an expected order, Mr. De Vliegher said.
Hackers remained undetected while they moved around the company's
network.
In the aftermath of the attack, Mr. De Vliegher reorganized the
cybersecurity team into three units focused on investigating the
incident, recovering and supporting operations, Mr. De Vliegher
told WSJ Pro Cybersecurity in April.
Two of those three units have since merged and the team is now
split into a forensic group and an operational-support group,
providing two lines of defense. "No matter how good your cyber
defense is, you need a second-level defense. You need a couple of
people that look into whether the first group is effective," he
said.
Write to Catherine Stupp at Catherine.Stupp@wsj.com
(END) Dow Jones Newswires
August 20, 2019 02:47 ET (06:47 GMT)
Copyright (c) 2019 Dow Jones & Company, Inc.
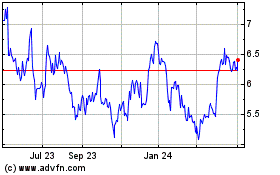
Norsk Hydro ASA (QX) (USOTC:NHYDY)
Historical Stock Chart
From Aug 2024 to Sep 2024
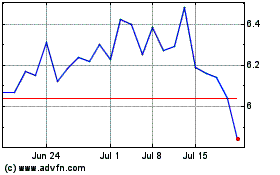
Norsk Hydro ASA (QX) (USOTC:NHYDY)
Historical Stock Chart
From Sep 2023 to Sep 2024