Check Point’s Threat Index Reveals RoughTed and Fireball Drop-off in July
August 21 2017 - 9:00AM

Check Point® Software Technologies Ltd. (NASDAQ:CHKP) reveals that
according to its latest Global Threat Impact Index, the number of
organizations impacted by the RoughTed malvertising campaign fell
by more than a third during July, from 28% to 18%.
RoughTed is a large-scale malvertising campaign
used to deliver malicious websites and payloads such as scams,
adware, exploit kits and ransomware. Despite its drop-off, RoughTed
remained the most prevalent form of malware during July. Hacker
Defender, a user-mode rootkit for Windows, increased to second
place and affected 5% of organizations globally.
The Index also reveals a sharp decline in the
prevalence of Fireball, which fell to third place. In July, it
impacted 4.5% of organizations, down from 20% of organizations only
two months ago, following the arrest of the suspected distributors
during the month.
“The drop in Fireball is encouraging and can be
related to the arrest of its suspected distributors in China. This
highlights the positive impact that law enforcement authorities can
have when working in tandem with the cyber security industry,” said
Maya Horowitz, Threat Intelligence Group Manager at Check
Point.
July 2017’s Top 3 ‘Most Wanted’
Malware:*The arrows relate to the change in rank compared
to the previous month.
- ↔ RoughTed - Large scale Malvertising used to
deliver various malicious websites and payloads such as scams,
adware, exploit kits and ransomware. It can be used to attack any
type of platform and operating system, and utilizes ad-blocker
bypassing and fingerprinting in order to make sure it delivers the
most relevant attack.
- ↑ Hacker Defender - User-mode Rootkit for
Windows, can be used to hide files, processes and registry keys,
and also implements a backdoor and port redirector that operates
through TCP ports opened by existing services. This means it is not
possible to find the hidden backdoor through traditional
means.
- ↓ Fireball - Browser-hijacker that can be
turned into a full-functioning malware downloader. It is capable of
executing any code on the victim machines, resulting in a wide
range of actions from stealing credentials to dropping additional
malware.
For the first time in 2017, Hummingbad did not
appear in the top three of the most common mobile malware as
spyware. This month, TheTruthSpy had the highest impact on
organizations mobile estates - followed by Lotoor and Triada.
Top 3 ‘Most Wanted’ mobile
malware:
- TheTruthSpy – Mobile spyware which can be
installed in stealth mode and used to track and record data from a
device.
- Lotoor - Hack tool that exploits
vulnerabilities on Android operating system in order to gain root
privileges on compromised mobile devices.
- Triada - Modular Backdoor for Android which
grants super-user privileges to downloaded malware and helps it
embed into system processes. Triada has also been spoofing URLs
loaded in the browser.
“It is encouraging to see highly infectious malware
variants becoming less impactful, but it is critical that
organizations do not see this as a signal that they can drop their
guard. While RoughTed’s effectiveness dropped considerably, nearly
one in five organizations were still impacted by it during July. It
is also important to be aware that as soon as one avenue for
attackers is shut down, cyber-criminals quickly devise new malware
forms to attack targets with. Organizations in every industry need
a multi-layered approach to their cyber security.
SandBlast™ Zero-Day Protection and Mobile Threat
Prevention, for example, protect against the widest range of
continually evolving attack types, and also protect against
zero-day malware variants,” concluded Horowitz.
Check Point’s Global Threat Impact Index and its
ThreatCloud Map is powered by Check Point’s ThreatCloud
intelligence, a collaborative network to fight cybercrime which
delivers threat data and attack trends from a global network of
threat sensors. The ThreatCloud database holds over 250 million
addresses analyzed for bot discovery, more than 11 million malware
signatures and over 5.5 million infected websites, and identifies
millions of malware types daily.
* The complete list of the top 10 malware families
in July can be found on the Check Point Blog:
http://blog.checkpoint.com/2017/08/21/julys-wanted-malware-roughted-fireball-decrease-stay-prevalent/
Check Point’s Threat Prevention Resources are
available at:
http://www.checkpoint.com/threat-prevention-resources/index.html
Follow Check Point via:Check Point
Research: https://research.checkpoint.com
Twitter: http://www.twitter.com/checkpointswFacebook: https://www.facebook.com/checkpointsoftwareBlog:
http://blog.checkpoint.com
YouTube: http://www.youtube.com/user/CPGlobalLinkedIn:
https://www.linkedin.com/company/check-point-software-technologies
About Check Point Software Technologies
Ltd.Check Point Software Technologies Ltd.
(www.checkpoint.com) is the largest pure-play security vendor
globally, provides industry-leading solutions, and protects
customers from cyber attacks with an unmatched catch rate of
malware and other types of attacks. Check Point offers a complete
security architecture defending enterprises’ networks to mobile
devices, in addition to the most comprehensive and intuitive
security management. Check Point protects over 100,000
organizations of all sizes.
INVESTOR CONTACT:
Kip E. Meintzer
Check Point Software Technologies
+1.650.628.2040
ir@checkpoint.com
MEDIA CONTACT:
Emilie Beneitez Lefebvre
Check Point Software Technologies
Tel: +44 (0) 7785 381 302
press@checkpoint.com
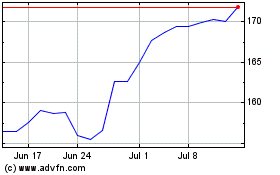
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From Mar 2024 to Apr 2024
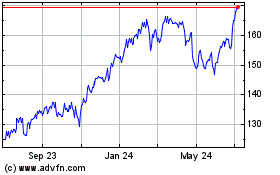
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From Apr 2023 to Apr 2024