Check Point Clears the Path to Web 2.0 Application Control
August 02 2010 - 8:30AM
Marketwired
Check Point® Software Technologies Ltd. (NASDAQ: CHKP), the
worldwide leader in securing the Internet, today announced its new
Application Control Software Blade that enables organizations to
secure and manage the use of thousands of Web 2.0 applications in
the enterprise. The new blade integrates Check Point's unique
UserCheck technology to engage employees in the decision-making
process and enables IT administrators to tailor application usage
policies. In addition, it delivers unmatched application visibility
by leveraging Check Point AppWiki, the world's largest application
library, with over 50,000 Web 2.0 widgets and more than 4,500
Internet applications, including social networking, instant
messaging and media streaming. For the first time, companies
benefit from a unique combination of technology, user awareness and
broad application control -- all available in a single solution.
According to a recent Check Point and Ponemon global survey of
over 2,100 IT security administrators, the majority of respondents
believe employees are essential to helping organizations mitigate
security risks associated with emerging Internet applications in
the enterprise. Check Point is bringing a differentiated, modern
approach to application control that provides a unique combination
of robust security technology and user awareness, both necessary
for employees to utilize Web 2.0 tools without jeopardizing the
security of the network. Check Point's new Application Control
software blade enables organizations to define granular policy
controls for web applications tailored to meet the organization and
employees' specific needs. In addition, the new blade integrates
Check Point's innovative UserCheck technology to alert users of the
potential risks applications may cause and asks employees whether
the purpose is for business or personal use. The solution educates
users on corporate use policies, while providing key usage trends
to IT administrators.
"We're bringing a new dynamic to application control by giving
businesses a strong combination of technology, employee awareness
and access to the largest database of web applications in the
industry," said Dorit Dor, vice president of products at Check
Point Software Technologies. "Organizations will benefit from
granular policy control that is truly customized based on their
employee, business and security needs."
"Internally, we struggle with how to enable access to certain
applications or websites based on employee roles and
responsibilities. For example, we may want to give employees access
to Facebook, but block non-business applications, such as games or
chat," said Erik Yunghans, network security administrator at
Bentley Systems, Inc. "It's great knowing Check Point gives our
security policies that level of granularity and flexibility."
Based on Check Point's Software Blade architecture, the
Application Control blade can be activated with a single click on
any Check Point security gateway, enabling organizations to
leverage their existing infrastructure. The new blade is centrally
managed from a single security management console, and IT
administrators can monitor and control application usage based on
identity, user or group, frequency and level of risk with unified
event analysis. The new blade also provides seamless, agent-based
and agent-less, Active Directory integration to allow individual or
group access to specific applications, while restricting
others.
"Internet threats today leverage Web applications, especially
social networking, to gain access to the corporate network," said
Charles Kolodgy, security research analyst at IDC. "Any company
looking at solutions to provide Web 2.0 protection should consider
the strength of the technology, the volume of the library of
protections available, where the solution is deployed in the
network and what role employees have in the process of mitigating
risk. Check Point's new Application Control Software Blade is a
strong and complete solution that addresses these
requirements."
Additional information about Check Point Application Control
Software Blade can be found at:
http://www.checkpoint.com/products/softwareblades/application-control.html.
To browse through a sampling of applications in the Check Point
AppWiki, visit: http://appwiki.checkpoint.com.
"Check Point's latest firewall innovation, combined with our
application library -- 50 times larger than any other in the
industry -- provides organizations with the broadest and most
flexible protection, without taking away the business advantages of
Web 2.0 use," concluded Dor.
Availability General availability for the
Check Point Application Identity/Control Software Blade will be
available for purchase through the Check Point worldwide network of
value-added resellers in the fourth quarter of 2010. To find a
Check Point partner, visit:
http://partners.us.checkpoint.com/partnerlocator/.
About Check Point Software Technologies
Ltd. Check Point Software Technologies Ltd.
(www.checkpoint.com), the worldwide leader in securing the
Internet, is the only vendor to deliver Total Security for
networks, data and endpoints, unified under a single management
framework. Check Point provides customers with uncompromised
protection against all types of threats, reduces security
complexity and lowers total cost of ownership. Check Point first
pioneered the industry with FireWall-1 and its patented stateful
inspection technology. Today, Check Point continues to innovate
with the development of the Software Blade architecture. The
dynamic Software Blade architecture delivers secure, flexible and
simple solutions that can be fully customized to meet the exact
security needs of any organization or environment. Check Point
customers include tens of thousands of businesses and organizations
of all sizes including all Fortune 100 companies. Check Point's
award-winning ZoneAlarm solutions protect millions of consumers
from hackers, spyware and identity theft.
©2010 Check Point Software Technologies Ltd. All rights
reserved
Image Available:
http://www2.marketwire.com/mw/frame_mw?attachid=1321601 Image
Available:
http://www2.marketwire.com/mw/frame_mw?attachid=1321597
Add to Digg Bookmark with del.icio.us Add to Newsvine
Media Contact Stephanie Look Check Point Software
Technologies +1 650.628.2171 press@us.checkpoint.com Investor
Contact Kip E. Meintzer Check Point Software Technologies +1
650.628.2040 ir@us.checkpoint.com
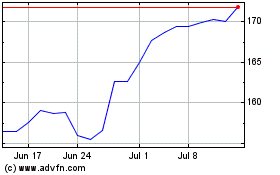
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From Apr 2024 to May 2024
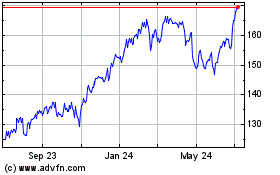
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From May 2023 to May 2024