By Rebecca Smith
PG&E Corp. and a municipal utility in Missouri broke rules
designed to protect the nation's electric system from cyber and
physical attacks and were sanctioned by federal regulators,
according to newly released documents that provided the identities
of the violators.
In addition, PG&E was the utility sanctioned in a separate
case for violations of these critical infrastructure protection
rules, along with Detroit-based utility DTE Energy Co., according
to people familiar with the cases and redacted documents reviewed
by The Wall Street Journal.
The identification of the violators follows the recent
revelation that Duke Energy Corp. broke the same set of rules.
The cases against DTE, PG&E and City Utilities of
Springfield, Mo., were lodged from 2014 to 2016 -- a time when
Russia was in the midst of a major campaign to penetrate utility
defenses, according to federal officials.
What is unusual isn't that companies were penalized, but that
the public now knows some of the identities. Most violators are
kept confidential in a system designed to encourage self-disclosure
by the utilities but some critics say is too protective of the
industry.
Although about 250 penalty cases have been lodged against U.S.
utilities in the past decade for violating rules designed to
protect essential infrastructure, few identities have been divulged
by the Federal Energy Regulatory Commission, the agency that
oversees the interstate electric system.
When the identities do come out, the reason is usually because
regulators released them in response to public-records requests
after they believe vulnerabilities have been remedied. That was the
case in FERC releasing documents disclosing City Utilities in its
case and PG&E in one of its cases.
The other way that identities are revealed is when they are
disclosed by people with knowledge of the matter. Such was the case
for DTE and another PG&E case, though redacted information
about their violations was already public.
Charlotte, N.C.-based Duke was outed in February as the company
that committed 127 violations of safety rules in recent years.
Among other things, Duke failed to protect sensitive information on
its most critical cyber assets, officials said. FERC is reviewing
the case and a $10 million settlement agreement.
Public officials are becoming more vocal about threats to
critical infrastructure. In late January, U.S. intelligence
agencies said Russian and Chinese agents possess the ability to
knock out power temporarily and disrupt gas pipelines "for days to
weeks" through cyber means.
A Journal investigation, published in January, showed how
Russian hackers targeted the unprotected computer systems of small
vendors in an attempt to move up the supply chain and compromise
defenses of electric companies.
Increased public attention on grid vulnerabilities has sent a
shudder through the electric industry.
Last week, three trade groups asked FERC to look at its rules on
disclosure practices and, in the meantime, to halt processing
records requests, including those by the Journal.
David Ortiz, deputy director of FERC's Office of Electric
Reliability, said cyberattacks are happening in large numbers, but
utilities report almost no successful attacks even when assured of
confidentiality. Recently, FERC has started requiring utilities
report attempts, not just successful hacks.
There is debate on how much of that information should be
public.
Regulators rely on utilities to self-report their violations and
accept audit findings. They fear that system will break down if
companies are exposed to public scrutiny.
Security researcher and blogger Michael Mabee, who has asked
FERC to identify utilities associated with more than 200 penalty
cases, said the regulatory system needs fixing, and "the only way
for that to happen is by shining the light of day on it."
Mr. Mabee also said penalties negotiated through settlement
agreements are too low. So far, they have not been made public.
FERC's Mr. Ortiz said identities are protected to honor
confidentiality requests from the North American Electric
Reliability Corp., called NERC, the federally appointed
organization that crafts utility standards and audits compliance.
It refers penalty cases to FERC for enforcement.
The cases involving DTE, City Utilities and PG&E demonstrate
why officials are worried about security.
DTE agreed to pay $1.7 million in 2016 to settle 36 infractions
of rules in prior years, according to people with knowledge of the
case. The utility said it takes a duty "to protect the bulk power
system very seriously," but declined additional comment.
NERC said auditors found "serious, systemic security and
compliance issues" that persisted from one examination to the next,
according to public case documents.
The utility failed to apply 75 security patches to its Energy
Management System, a set of computer-aided tools that guides
engineers and helps control power flows. Auditors found the utility
stopped making updates as soon as a prior audit ended.
The utility also failed to keep backup software that it would
need to recover from a catastrophic cyber event.
City Utilities of Springfield, Mo., violated security rules by
failing to identify its primary and backup control centers as
critical facilities requiring special protections. Its identity was
disclosed in the 2014 case in response to a FOIA request by the
Journal and Mr. Mabee.
The utility didn't respond to requests for comment.
PG&E, California's biggest utility, now is known as the
company behind three penalty cases.
FERC said PG&E was fined $98,500 in 2014 for failing to keep
proper logs for 30 critical workstations. Without logs, auditors
said, the utility couldn't have identified hackers' "attacks,
multiple bad password attempts or irregular logons to these
workstations." PG&E later found similar issues with 150 other
workstations and servers.
Separately, PG&E was fined $1.125 million in 2016 for
failing to adequately protect new electrical substations against
potential attacks, according to one person familiar with the
case.
PG&E said its cybersecurity measures are "robust and
consistent with the best practices being employed in the industry."
It added that confidentiality "promotes self-reporting" and
disclosure "may jeopardize national security by exposing potential
grid vulnerabilities."
Last year, PG&E was identified by the Journal as the company
that lost control of a confidential database of its cyber assets in
2016 resulting in their internet exposure.
Write to Rebecca Smith at rebecca.smith@wsj.com
(END) Dow Jones Newswires
April 09, 2019 11:03 ET (15:03 GMT)
Copyright (c) 2019 Dow Jones & Company, Inc.
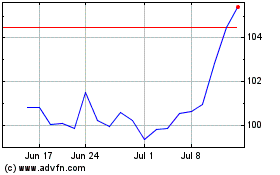
Duke Energy (NYSE:DUK)
Historical Stock Chart
From May 2024 to Jun 2024
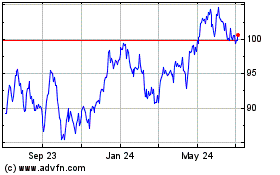
Duke Energy (NYSE:DUK)
Historical Stock Chart
From Jun 2023 to Jun 2024