Cybersecurity Professionals Face Challenges on the Path to Automation, Reveals Juniper Networks and Ponemon Institute Report
June 26 2018 - 7:45AM

Juniper Networks (NYSE:JNPR), an industry leader in automated,
scalable and secure networks, today announced a new study, The
Challenge of Building the Right Security Automation Architecture,
conducted with the Ponemon Institute that found that although
enterprises understand automation is crucial to addressing the
cybersecurity skills shortage and achieving a stronger security
posture, the majority are experiencing challenges with determining
how, when and where to automate.
By 2021, fighting cybercrime will cost businesses globally more
than $6 trillion annually and there will be 3.5 million unfilled
security jobs, according to Cybersecurity Ventures. Echoing this
issue, 57 percent of survey respondents say they are unable to
recruit the skilled personnel needed to deploy their security
automation tools. As cybercriminals continue to automate attacks
without being subject to the same regulations and compliance
constraints, organizations are struggling with understaffed
security teams, manual processes, disparate systems and complex
policies that leave them buried in low value tasks.
“The cybercrime landscape is incredibly vast, organized and
automated – cybercriminals have deep pockets and no rules, so they
set the bar,” said Amy James, Director of Security Portfolio
Marketing at Juniper Networks. “Organizations need to level the
playing field. You simply cannot have manual security solutions and
expect to successfully battle cybercriminals, much less get ahead
of their next moves. Automation is crucial.”
Report Highlights:
Security Automation is a MustThe growing threat
landscape and security skills gap facing cybersecurity teams demand
that organizations implement automation for a stronger security
posture. Respondents recognize this growing importance and how
automation can improve productivity, address the growing volume of
threats and reduce the rate of false positives.
- The top two benefits of security automation, according to
respondents, are: increased productivity of security personnel (64
percent) and automated correlation of threat behavior to address
the volume of threats (60 percent).
- 54 percent of respondents say these automation technologies
simplify the process of detecting and responding to cyber threats
and vulnerabilities.
Vendor Sprawl is Creating ChaosToday, security
environments are more complex and cybercriminals are more
determined than ever, yet organizations are utilizing security
solutions built on stand-alone security tools, resulting in vendor
sprawl and ineffective security strategies. Organizations now
recognize that the ability to integrate disparate security
technologies is the main challenge to achieving an effective
security automation architecture, according to 71 percent of
respondents.
- 57 percent have interoperability issues among security
technologies that diminish the effectiveness of automation
technologies.
- 63 percent say it is difficult to integrate security automation
technologies and tools with legacy systems.
- 59 percent believe their organization needs to streamline its
number of vendors.
Skills Shortage is a BarrierAs a result of this
vendor sprawl, security practitioners are finding themselves bogged
down for nearly two hours each day processing alerts, events and
logs to find malicious activity, according to the study. This
leaves them with limited manpower to implement critical automation
technologies and results in diminishing security postures. On top
of that, the market is dry when it comes to skilled security
personnel.
- Only 35 percent say their organizations currently have the
in-house expertise to be effective in using security automation to
respond to malicious threats.
- 62 percent say the lack of in-house expertise diminishes their
organization’s security posture.
- 57 percent say they are unable to recruit knowledgeable or
skilled personnel to deploy their security automation tools.
About the Report:“The Challenge of Building the
Right Security Automation Architecture” report, sponsored by
Juniper Networks and conducted by Ponemon Institute, highlights
findings and insights derived from a sample of 1,859 IT and IT
security practitioners located in Germany, France, the United
Kingdom and the United States and who are familiar with their
organizations’ use of security automation and have some
responsibility for evaluating and/or selecting security automation
technologies and vendors.
Additional Resources:
- Download the Juniper Networks and Ponemon Institute report “The
Challenge of Building the Right Security Automation Architecture”
here.
- Follow Juniper Networks online: Facebook |
Twitter | LinkedIn
- Juniper Blogs and Community: J-Net
- Juniper 1on1 app: Keep up with all things Juniper from your
smartphone. Download the app from iTunes and Google
Play store today.
About Juniper NetworksJuniper Networks
simplifies the complexities of networking with products, solutions
and services in the cloud era to transform the way we
connect, work and live. We remove the traditional constraints of
networking to enable our customers and partners to deliver
automated, scalable and secure networks that connect the
world. Additional information can be found at Juniper
Networks (www.juniper.net) or connect with Juniper
on Twitter, LinkedIn and Facebook.
Juniper Networks, the Juniper Networks logo and Junos are
registered trademarks of Juniper Networks, Inc. and/or its
affiliates in the United States and other countries. Other
names may be trademarks of their respective owners.
Media Relations:Emily ScherJuniper
Networks(408) 936-1226escher@juniper.net
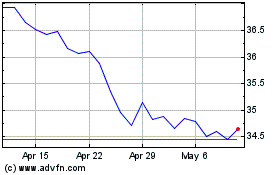
Juniper Networks (NYSE:JNPR)
Historical Stock Chart
From Aug 2024 to Sep 2024
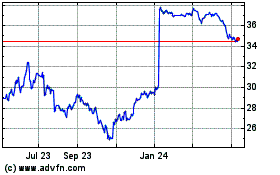
Juniper Networks (NYSE:JNPR)
Historical Stock Chart
From Sep 2023 to Sep 2024