Radware® (NASDAQ: RDWR), a leading provider of cyber security and
application delivery solutions, released its 2022 Global Threat
Analysis Report. The full-year report leverages intelligence
provided by network and application attack activity sourced from
Radware’s Cloud and Managed Services, Global Deception Network and
threat research team.
“‘More’ is the operative word for the global threat
landscape in 2022. Compared to 2021, there were not only more DDoS
attacks in terms of sheer number, but they were also more powerful,
frequent and complex, spanning more attack vectors,” said Pascal
Geenens, director of threat intelligence for Radware. “The surge
can be attributed in part to digitalization, the war in Ukraine,
and a long-tail of new vulnerabilities and exposed services driven
by work-from-home remote access during Covid. The ongoing tensions
between major world powers have also led to a rise in
state-sponsored cyberattacks and espionage activities.”
GLOBAL ATTACK TRENDS: THE UNRELENTING RISE
OF DDOSThe global DDoS landscape is rapidly evolving. In
2022, DDoS attack profiles were redefined by gains in number,
frequency, volume, power, duration and complexity.
- Number of attacks: In 2022,
the number of DDoS attacks grew 150% on a global basis compared to
the previous year. The number of attacks in the Americas rose even
faster, increasing 212% compared to 2021. More than half of the
attacks were aimed at organizations in EMEA. The Americas accounted
for 35% of the attacks while 7% of the attacks targeted APAC
organizations.
- Attack frequency: The
frequency of DDoS attacks also saw a significant and concerning
uptick. Globally, organizations mitigated an average of 29.3
attacks per day during the fourth quarter of 2022, 3.5 times more
compared to 8.4 attacks per day at the end of 2021. Attacks in EMEA
grew even faster than the global average and outpaced both the
Americas and APAC. Organizations in EMEA averaged 45 attacks per
day in the fourth quarter of 2022, four-times more compared to 11.3
attacks per day during the same period in 2021.
- Attack volume: While the total global attack
volume recorded in 2022 was 4.44PB, an increase of 32% compared to
2021, the Americas faced the heftiest increases. Last year, attack
volumes in the Americas outpaced global volumes, growing 110%
compared to 2021. While EMEA topped the Americas in frequency of
attacks, it saw total attack volume decline in 2022, decreasing by
44% compared to the previous year.
- Attack power: Globally, the largest recorded
attack in 2022 was 1.46Tbps, which is 2.8 times larger than the
largest attack recorded in 2021.
- Attack duration: The longest
attacks in 2022 ranged between 100 and 250Gbps on a global basis,
where on average the attacks lasted 66 hours or 2.75 days.
- Attack complexity: DDoS attacks continue to
increase in complexity. Attackers typically leverage multiple and
dissimilar vectors to increase the impact and make attack
mitigation harder. On a global basis in 2022, attacks above 1Gbps
on average had more than two dissimilar attack vectors per attack,
which doubled in complexity for attacks above 10Gbps. Attacks above
100Gbps had on average more than nine dissimilar attack vectors
with the most complex attacks leveraging 38 dissimilar attack
vectors.
“In 2023, the democratization of DDoS and patriotic
hacktivism will continue to drive an increase in smaller, more
frequent attacks – a trend we are already seeing in the increased
frequency of lower volume attacks in EMEA. At the same time, expect
the cybercrime underground to become even better organized and
funded in its pursuit of hard-hitting attacks,” said Geenens.
“Attackers are always looking for new more sophisticated ways to
advance their cyber agendas. As a result, organizations find
themselves in an escalating state of risk, trying to defend
themselves against next-generation threats.”
MOST ATTACKED INDUSTRIES
On a global basis, finance was the most attacked
industry in 2022, with 53% of the overall attack activity, followed
by technology (20%) and healthcare (11%).
Even on a geographic distribution, finance and
technology were among the industries shouldering the brunt of the
DDoS activity.
- In America, finance represented 32% of the attack activity,
followed by healthcare (24%) and technology (17%).
- In EMEA, finance (71%) also topped the list as the
most-attacked industry, followed by technology (16%) and government
(4%).
- In APAC, technology was the most attacked industry, with 70% of
the attack activity, followed by finance (9%) and government
(8%).
WEB APPLICATION ATTACKS
Web application and API attacks grew exponentially
in 2022.
- Web application and API attacks increased 128% year over year,
significantly out pacing the 88% increase in attacks between 2020
and 2021.
- Predictable resource location attacks accounted for almost half
of the attack activity. Together, code injection (14%) and SQL
injection (11%) attacks represented another quarter of the web
application attacks.
- The most attacked industries were retail and wholesale trade
(25%), followed by high-tech (20%), and carriers (15%), together
accounting for 60% of blocked web application attacks.
Radware’s complete 2022 Global Threat Analysis
Report can be downloaded here.
About RadwareRadware® (NASDAQ:
RDWR) is a global leader of cyber security and application delivery
solutions for physical, cloud, and software defined data centers.
Its award-winning solutions portfolio secures the digital
experience by providing infrastructure, application, and corporate
IT protection, and availability services to enterprises globally.
Radware’s solutions empower enterprise and carrier customers
worldwide to adapt to market challenges quickly, maintain business
continuity, and achieve maximum productivity while keeping costs
down. For more information, please visit the Radware website.
Radware encourages you to join our community and
follow us on: Facebook, LinkedIn, Radware Blog, Twitter, YouTube,
and Radware Mobile for iOS and Android.
©2023 Radware Ltd. All rights reserved. Any Radware
products and solutions mentioned in this press release are
protected by trademarks, patents, and pending patent applications
of Radware in the U.S. and other countries. For more details,
please see: https://www.radware.com/LegalNotice/. All other
trademarks and names are property of their respective owners.
THIS PRESS RELEASE AND THE RADWARE 2022 GLOBAL
THREAT ANALYSIS REPORT ARE PROVIDED FOR INFORMATIONAL PURPOSES
ONLY. THESE MATERIALS ARE NOT INTENDED TO BE AN INDICATOR OF
RADWARE'S BUSINESS PERFORMANCE OR OPERATING RESULTS FOR ANY PRIOR,
CURRENT, OR FUTURE PERIOD.
Radware believes the information in this document
is accurate in all material respects as of its publication date.
However, the information is provided without any express,
statutory, or implied warranties and is subject to change without
notice.
The contents of any website or hyperlinks mentioned
in this press release are for informational purposes and the
contents thereof are not part of this press release.
Safe Harbor Statement This press
release includes “forward-looking statements” within the meaning of
the Private Securities Litigation Reform Act of 1995. Any
statements made herein that are not statements of historical fact,
including statements about Radware’s plans, outlook, beliefs, or
opinions, are forward-looking statements. Generally,
forward-looking statements may be identified by words such as
“believes,” “expects,” “anticipates,” “intends,” “estimates,”
“plans,” and similar expressions or future or conditional verbs
such as “will,” “should,” “would,” “may,” and “could.” For example,
when we say organizations find themselves in an escalating state of
risk, trying to defend themselves against next-generation threats,
we are using a forward-looking statement. Because such statements
deal with future events, they are subject to various risks and
uncertainties, and actual results, expressed or implied by such
forward-looking statements, could differ materially from Radware’s
current forecasts and estimates. Factors that could cause or
contribute to such differences include, but are not limited to: the
impact of global economic conditions and volatility of the market
for our products; natural disasters and public health crises, such
as the coronavirus disease 2019 (COVID-19) pandemic; a shortage of
components or manufacturing capacity could cause a delay in our
ability to fulfill orders or increase our manufacturing costs; our
business may be affected by sanctions, export controls, and similar
measures, targeting Russia and other countries and territories, as
well as other responses to Russia’s military conflict in Ukraine,
including indefinite suspension of operations in Russia and
dealings with Russian entities by many multi-national businesses
across a variety of industries; our ability to successfully
implement our strategic initiative to accelerate our cloud
business; our ability to expand our operations effectively; timely
availability and customer acceptance of our new and existing
solutions; risks and uncertainties relating to acquisitions or
other investments; the impact of economic and political
uncertainties and weaknesses in various regions of the world,
including the commencement or escalation of hostilities or acts of
terrorism; intense competition in the market for cyber security and
application delivery solutions and in our industry in general, and
changes in the competitive landscape; changes in government
regulation; outages, interruptions, or delays in hosting services
or our internal network system; compliance with open source and
third-party licenses; the risk that our intangible assets or
goodwill may become impaired; our dependence on independent
distributors to sell our products; long sales cycles for our
solutions; changes in foreign currency exchange rates; undetected
defects or errors in our products or a failure of our products to
protect against malicious attacks; the availability of components
and manufacturing capacity; the ability of vendors to provide our
hardware platforms and components for our main accessories; our
ability to protect our proprietary technology; intellectual
property infringement claims made by third parties; changes in tax
laws; our ability to realize our investment objectives for our cash
and liquid investments; our ability to attract, train, and retain
highly qualified personnel; and other factors and risks over which
we may have little or no control. This list is intended to identify
only certain of the principal factors that could cause actual
results to differ. For a more detailed description of the risks and
uncertainties affecting Radware, refer to Radware’s Annual Report
on Form 20-F, filed with the Securities and Exchange Commission
(SEC) and the other risk factors discussed from time to time by
Radware in reports filed with, or furnished to, the SEC.
Forward-looking statements speak only as of the date on which they
are made and, except as required by applicable law, Radware
undertakes no commitment to revise or update any forward-looking
statement in order to reflect events or circumstances after the
date any such statement is made. Radware’s public filings are
available from the SEC’s website at www.sec.gov or may be obtained
on Radware’s website at www.radware.com.
Media Contact:Gerri
DyrekRadwareGerri.Dyrek@radware.com
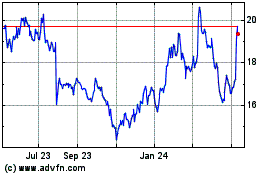
RADWARE (NASDAQ:RDWR)
Historical Stock Chart
From Jun 2024 to Jul 2024
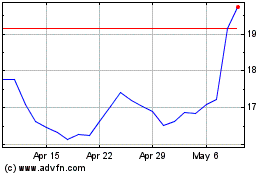
RADWARE (NASDAQ:RDWR)
Historical Stock Chart
From Jul 2023 to Jul 2024