The CISO View on DevOps: New Report Highlights Approaches to Reduce Cyber Security Risk
January 16 2019 - 8:30AM
Business Wire
Global 1000 CISOs Provide Recommendations for
Protecting Privileged Access in DevOps and Cloud Environments
CyberArk (NASDAQ: CYBR), the global leader in privileged
access security, today issued a new research report, “The CISO
View: Protecting Privileged Access in DevOps and Cloud
Environments.” Based on the direct experiences of a panel of Global
1000 CISOs, the report provides advice for security teams to help
effectively assess risk, drive developer collaboration, and
prioritize steps to protect DevOps processes while maintaining
developer velocity.
The report is part of The CISO View industry initiative and
features contributions from executives at leading organizations who
are adopting DevOps methodologies and tools, including American
Express Company, American Financial Group, Asian Development Bank,
Carlson Wagonlit Travel, CIBC, GIC Private Limited, ING Bank,
Lockheed Martin, NTT Communications, Orange Business Services,
Pearson, Rockwell Automation and Starbucks. Sponsored by CyberArk,
the initiative brings together leading CISOs for peer-to-peer
information sharing to help security teams build effective cyber
security programs.
While security strategies should address privileged access and
the risk of unsecured secrets and credentials, they should also
closely align with DevOps culture and methods to avoid negatively
impacting developer velocity and slowing the release of new
services. Despite this, 73 percent of organizations surveyed for
the 2018 CyberArk Global Advanced Threat Landscape report have no
strategy to address privileged access security for DevOps.
The report summarizes five key recommendations based on the
real-world experiences of participating CISOs, including:
- Transform the security team into
DevOps partners – Ensure security practitioners and developers
have the right skills, make it easy for developers to do the right
thing, encourage collaboration and adopt agile DevOps methods
within security.
- Prioritize securing DevOps tools and
infrastructure – Set and enforce policies for tools selection
and configuration, control access to DevOps tools, ensure least
privilege and protect and monitor infrastructure.
- Establish enterprise requirements
for securing credentials and secrets – Mandate the centralized
management of secrets, extend auditing and monitoring capabilities,
eliminate credentials from tools and applications, and develop
reusable code modules.
- Adapt processes for application
testing – Integrate automated testing of code, compel
developers to fix security issues using a “break the build”
approach and consider a bug bounty program.
- Evaluate the results of DevOps
security programs – Test secrets management solution
deployments, measure and promote improvements and educate
auditors.
“This CISO View report captures the experiences and
recommendations of senior executives who are securely embracing
DevOps workflows,” said Marianne Budnik, CMO, CyberArk. “For
organizations embarking on digital transformation initiatives, it
has never been more important to align security and risk postures
across new tools and technologies. In understanding organizational
and operational challenges, security teams can more effectively
drive productive discussions across executive, security and
developer teams.”
This report is the third in The CISO View report series, which
was developed in conjunction with independent research firm
Robinson Insight and relies on the insights and guidance
contributed by The CISO View panel of Global 1000 CISOs, members of
the security community and other industry experts.
To download “The CISO View: Protecting Privileged Access in
DevOps and Cloud Environments” and other reports in the series,
visit https://www.cyberark.com/cisoview/.
Additional Resources
- [Video] The CISO View: Protecting
Privileged Access in DevOps and Cloud Environments
- [Webinar] How CISOs at Leading Global
Organizations Secure Their DevOps Environments
About CyberArkCyberArk (NASDAQ: CYBR) is the global
leader in privileged access security, a critical layer of IT
security to protect data, infrastructure and assets across the
enterprise, in the cloud and throughout the DevOps pipeline.
CyberArk delivers the industry’s most complete solution to reduce
risk created by privileged credentials and secrets. The
company is trusted by the world’s leading organizations, including
50 percent of the Fortune 500, to protect against external
attackers and malicious insiders. A global company, CyberArk is
headquartered in Petach Tikva, Israel, with U.S. headquarters
located in Newton, Mass. The company also has offices throughout
the Americas, EMEA, Asia Pacific and Japan. To learn more about
CyberArk, visit www.cyberark.com, read the CyberArk blogs or follow
on Twitter via @CyberArk, LinkedIn or Facebook.
Copyright © 2019 CyberArk Software. All Rights Reserved. All
other brand names, product names, or trademarks belong to their
respective holders.
View source
version on businesswire.com: https://www.businesswire.com/news/home/20190116005123/en/
Media Relations Contacts:Brian Merrill, fama PRPhone:
+1-617-986-5005Email: cyberark@famapr.comLiz Campbell,
CyberArkPhone: +1-617-558-2191Email: press@cyberark.comInvestor
Relations Contact:Erica Smith, CyberArkPhone: +1
617-630-6426Email: ir@cyberark.com
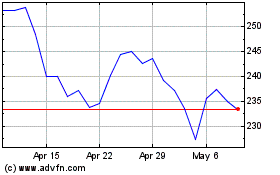
CyberArk Software (NASDAQ:CYBR)
Historical Stock Chart
From Aug 2024 to Sep 2024
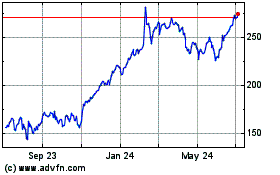
CyberArk Software (NASDAQ:CYBR)
Historical Stock Chart
From Sep 2023 to Sep 2024