November’s Most Wanted Malware: Return of Necurs Botnet Brings New Ransomware Threat
December 12 2017 - 9:00AM

Check Point® Software Technologies Ltd. (NASDAQ:CHKP), a
leading provider of cyber-security solutions globally, has revealed
that the Necurs botnet has returned to the top ten most prevalent
malware during November 2017, as cyber-criminals used it to
distribute a new form of ransomware, according to the company’s
latest Global Threat Impact Index.
Check Point researchers found that hackers were using Necurs,
considered to be the largest spam botnet in the world, to
distribute the relatively new Scarab ransomware that was first seen
in June 2017. The Necurs botnet started mass distribution of Scarab
during the U.S. Thanksgiving holiday, sending over 12 million
emails in a single morning. Necurs has previously been used to
distribute some of the most insidious malware variants to hit
business networks in the past 12 months, including the Locky and
Globeimposter families.
Maya Horowitz, Threat Intelligence, Group Manager at Check Point
at Check Point commented: “The re-emergence of the Necurs botnet
highlights how malware that may seem to be fading away doesn’t
always disappear or become any less of a threat. Despite Necurs
being well known to the security community, hackers are still
enjoying lots of success distributing malware with this highly
effective infection vehicle”.
This reinforces the need for advanced threat prevention
technologies and a multi-layered cybersecurity strategy that
protects against both previously encountered, established malware
families as well as brand new, zero-day threats. As in
October, RoughTed, a large scale malvertising campaign, remained
the most prevalent threat, ahead of the Rig ek exploit kit in
second, and Cornficker, a worm that allows remote download of
malware in third.
November 2017’s Top 3 ‘Most Wanted’
Malware:*The arrows relate to the change in rank compared
to the previous month.
- ↔ RoughTed - a
purveyor of ad-blocker aware malvertising responsible for a range
of scams, exploits, and malware. It can be used to attack any type
of platform and operating system, and utilizes ad-blocker bypassing
and fingerprinting in order to make sure it delivers the most
relevant attack.
- ↑ Rig ek - Exploit Kit first
introduced in 2014. Rig delivers Exploits for Flash, Java,
Silverlight and Internet Explorer. The infection chain starts with
a redirection to a landing page that contains JavaScript that
checks for vulnerable plug-ins and delivers the exploit.
- ↑ Conficker - Worm that allows remote
operations and malware download. The infected machine is controlled
by a botnet, which contacts its Command & Control server to
receive instructions.
The most popular malware used to attack organizations’ mobile
estates remained unchanged from October, as Triada, a modular
backdoor for Android, continued to increase in
prevalence.
November’s Top 3 ‘Most Wanted’ mobile
malware:
- Triada - Modular Backdoor for Android which
grants superuser privileges to downloaded malware, as helps it to
get embedded into system processes. Triada has also been seen
spoofing URLs loaded in the browser.
- Lokibot - Android banking Trojan
and info-stealer, which can also turn into a ransomware that locks
the phone in case its admin privileges are removed.
- LeakerLocker - Android ransomware that reads
personal user data, and then presents it to the user and threatens
to leak it online if ransom payments aren’t met.
Check Point’s Global Threat Impact Index and its ThreatCloud Map
is powered by Check Point’s ThreatCloud intelligence, the largest
collaborative network to fight cybercrime which delivers threat
data and attack trends from a global network of threat sensors. The
ThreatCloud database holds over 250 million addresses analyzed for
bot discovery, more than 11 million malware signatures and over 5.5
million infected websites, and identifies millions of malware types
daily.
* The complete list of the top 10 malware families in November
can be found on the Check Point Blog
Check Point’s Threat Prevention Resources are available
at:
http://www.checkpoint.com/threat-prevention-resources/index.html
Follow Check Point
via:Twitter: http://www.twitter.com/checkpointswFacebook: https://www.facebook.com/checkpointsoftwareBlog:
http://blog.checkpoint.com
YouTube: http://www.youtube.com/user/CPGlobalLinkedIn:https://www.linkedin.com/company/check-point-software-technologies
About Check Point Software Technologies
Ltd.Check Point Software Technologies Ltd.
(www.checkpoint.com) is a leading provider of cyber security
solutions to governments and corporate enterprises globally.
Its solutions protect customers from cyber-attacks with an industry
leading catch rate of malware, ransomware and other types of
attacks. Check Point offers a multilevel security architecture that
defends enterprises’ cloud, network and mobile device held
information, plus the most comprehensive and intuitive one point of
control security management system. Check Point protects over
100,000 organizations of all sizes.
INVESTOR CONTACT: Kip E.
Meintzer Check Point Software Technologies
+1.650.628.2040ir@checkpoint.com
MEDIA CONTACT:Emilie Beneitez LefebvreCheck
Point Software TechnologiesTel: +44 (0) 7785 381
302press@checkpoint.com
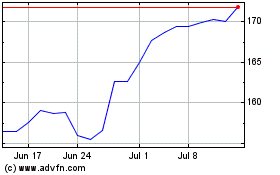
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From Aug 2024 to Sep 2024
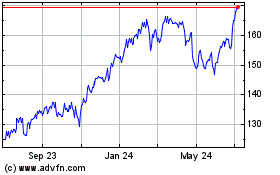
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From Sep 2023 to Sep 2024