Archive files “.ZIP past” Office docs as most common malicious file type for the first time
December 01 2022 - 9:00AM

HP Inc. (NYSE: HPQ) today issued its third quarter HP Wolf Security
Threat Insights Report, finding that archive file formats – such as
ZIP and RAR files – were the most common file type for delivering
malware, surpassing Office files for the first time in three years.
This report provides an analysis of real-world cyberattacks,
helping organizations to keep up with the latest techniques
cybercriminals use to evade detection and breach users in the
fast-changing cybercrime landscape.
Based on data from millions of endpoints running HP Wolf
Security, the research found 44% of malware was delivered inside
archive files – an 11% rise on the previous quarter – compared to
32% delivered through Office files such as Microsoft Word, Excel,
and PowerPoint.1
The report identified several campaigns that were combining the
use of archive files with new HTML smuggling techniques – where
cybercriminals embed malicious archive files into HTML files to
bypass email gateways – to then launch attacks.
For example, recent QakBot and IceID campaigns used HTML files
to direct users to fake online document viewers that were
masquerading as Adobe. Users were then instructed to open a ZIP
file and enter a password to unpack the files, which then deployed
malware onto their PCs.
As the malware within the original HTML file is encoded and
encrypted, detection by email gateway or other security tools is
very difficult. Instead, the attacker relies on social engineering,
creating a convincing and well-designed web page to fool people
into initiating the attack by opening the malicious ZIP file. In
October, the same attackers were also found using fake Google Drive
pages in an ongoing effort to trick users into opening malicious
ZIP files.
“Archives are easy to encrypt, helping threat actors to conceal
malware and evade web proxies, sandboxes, or email scanners. This
makes attacks difficult to detect, especially when combined with
HTML smuggling techniques. What was interesting with the QakBot and
IceID campaigns was the effort put in to creating the fake pages –
these campaigns were more convincing than what we’ve seen before,
making it hard for people to know what files they can and can’t
trust,” explains Alex Holland, Senior Malware Analyst, HP Wolf
Security threat research team, HP Inc.
HP also identified a complex campaign using a modular infection
chain, which could potentially enable attackers to change the
payload – such as spyware, ransomware, keylogger – mid-campaign, or
to introduce new features, like geo-fencing. This could enable an
attacker to change tactics depending on the target they have
breached. By not including malware directly in the attachment sent
to the target, it is also harder for email gateways to detect this
type of attack.
“As shown, attackers are constantly switching up techniques,
making it very difficult for detection tools to spot,” comments Dr
Ian Pratt, Global Head of Security for Personal Systems, HP Inc.
“By following the Zero Trust principle of fine-grained isolation,
organizations can use micro-virtualization to make sure potentially
malicious tasks – like clicking on links or opening malicious
attachments – are executed in a disposable virtual machine
separated from the underlying systems. This process is completely
invisible to the user, and traps any malware hidden within, making
sure attackers have no access to sensitive data and preventing them
from gaining access and moving laterally.”
HP Wolf Security runs risky tasks like opening email
attachments, downloading files and clicking links in isolated,
micro-virtual machines (micro-VMs) to protect users, capturing
detailed traces of attempted infections. HP’s application isolation
technology mitigates threats that can slip past other security
tools and provides unique insights into novel intrusion techniques
and threat actor behavior. By isolating threats on PCs that have
evaded detection tools, HP Wolf Security has specific insight into
the latest techniques being used by cybercriminals. To date, HP
customers have clicked on over 18 billion email attachments, web
pages, and downloaded files with no reported breaches.
About the data
This data was anonymously gathered within HP Wolf Security
customer virtual machines from July-September
2022.
About HP
HP Inc. is a technology company that believes one thoughtful
idea has the power to change the world. Its product and service
portfolio of personal systems, printers, and 3D printing solutions
helps bring these ideas to life. Visit http://www.hp.com.
About HP Wolf Security
HP Wolf Security is a new breed2 of endpoint security. HP’s
portfolio of hardware-enforced security and endpoint-focused
security services are designed to help organizations safeguard PCs,
printers, and people from circling cyber predators. HP Wolf
Security provides comprehensive endpoint protection and resiliency
that starts at the hardware level and extends across software and
services. Visit
https://www.hp.com/uk-en/security/endpoint-security-solutions.html.
Vanessa Godsalvgodsal@hp.com
1 As detailed in page 2 of the HP Wolf Security Q3 Threat
Insights Report
https://threatresearch.ext.hp.com/hp-wolf-security-threat-insights-report-q3-2022/
2 HP Security is now HP Wolf Security. Security features vary by
platform, please see product data sheet for details.
©Copyright 2022 HP Development Company, L.P. The information
contained herein is subject to change without notice. The only
warranties for HP products and services are set forth in the
express warranty statements accompanying such products and
services. Nothing herein should be construed as constituting an
additional warranty. HP shall not be liable for technical or
editorial errors or omissions contained herein.
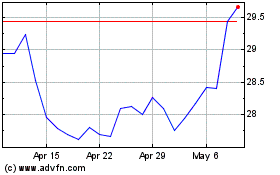
HP (NYSE:HPQ)
Historical Stock Chart
From Jun 2024 to Jul 2024
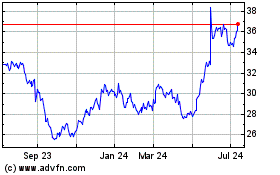
HP (NYSE:HPQ)
Historical Stock Chart
From Jul 2023 to Jul 2024