Radware® (NASDAQ: RDWR), a leading provider of cyber security and
application delivery solutions, released a new report—Hacktivism
Unveiled: Insights into the Footprints of Hacktivists. The tell-all
report provides an in-depth, comparative analysis of the
motivations, targets, tactics and techniques, and DDoS activities
of the world’s top 15 most active political and religious
hacktivists groups.
Radware’s threat intelligence reveals the rankings and profiles
of top attacking actors, the most attacked countries and websites,
as well as some misperceptions about well-known hacktivist groups.
The findings in Hacktivism Unveiled are based on the tracking and
analysis of messages from active hacktivists groups on Telegram
during the period between Feb. 18 - April 18, 2023.
Pascal Geenens, Radware’s director of threat intelligence, noted
the changing landscape of hacktivism. Geenens said, “While
religious hacktivism has remained a constant threat over the years,
Russia’s invasion of Ukraine has ushered in a whole new wave of not
only patriotic and political hacktivism, but also hacktivism in
general. Modern-day hacktivism with its barrage of
denial-of-service attacks is bolder, more determined, and more
media-driven than ever before.”
KEY FINDINGS
The Ranking of the Who’s Who of
HacktivistsDuring the period between Feb. 18 - April 18,
2023, over 1,800 denial-of-service attacks were claimed by
political and religious hacktivists across 80 Telegram
channels.
- NoName057(16) claimed almost 30% of the attacks, followed by
Anonymous Sudan (18%) and Mysterious Team (13%). NoName057(16) is
by far the most active DDoS hacktivist among the politically
driven, pro-Russian hacktivists.
- Anonymous Sudan, Mysterious Team, and Team Insane PK are
responsible for most of the religiously driven DDoS activity and
ranked second, third, and fourth respectively among hacktivists
claiming the most attacks.
- While there might be doubts about the alignment of Anonymous
Sudan to the Russian government, their attack motives and patterns
suggest a religiously motivated group rather than a politically
motivated one.
- Killnet, the group most prominently covered in the media and
often suspected of the most hacktivist DDoS activity, did not rank
among the top 15 of hacktivists, claiming 11 attacks during the
period compared to NoName057(16)’s 544 attacks.
- Passion, the pro-Russian, turned for-profit criminal hacktivist
group that provides DDoS-for-hire services, stands out among the
hacktivists targeting large U.S. cloud organizations.
Top Attacked CountriesDuring the period from
Feb. 18 - April 18, 2023:
- Israel topped the list of most attacked countries, shouldering
11% of the DDoS attacks, followed by India (9%), Poland (8%), and
Australia (8%). Israel, India, and Australia were targets of
pro-Islamic hacktivists during the recent #OpIsrael, #OpIndia, and
#OpAustralia operations.
- The United States (6%) and Germany (6%), followed by Sweden
(5%), Ukraine (5%), Denmark (4%), and Italy (4%) rounded out the
list of top 10 most targeted countries.
- Poland is the only country in the top five that was
specifically targeted by pro-Russian hacktivists in attacks
relating to the Russo-Ukrainian war.
Top Attacked WebsitesDuring the two-month
period:
- Business (19%), government (18%), and travel (13%) websites
were the most targeted by hacktivists, followed by financial
services (7%), education (6%), and health and medicine (4%).
- Business and government websites were attacked by most of the
top hacktivist groups that were tracked in the report.
- Financial services and travel websites were primarily targeted
by NoName057(16), Team Insane PK, Mysterious Team, and Anonymous
Sudan.
Geenens added, “Denial of service has always been an important
tactic used by hacktivist groups, and this will not change any time
soon. Any organization, independent of size and industry, can
become a target of hacktivists who desire to advance their cause
and hold organizations and governments accountable for their
actions. While there is no reason for panic, organizations need to
be prepared. It is widely known in the security community that
disrupting or impacting an organization or infrastructure requires
more perseverance than skills or sophistication.”
Radware’s complete Hacktivism Unveiled report can be found on
the company’s website.
About RadwareRadware® (NASDAQ: RDWR) is a
global leader of cyber security and application delivery solutions
for physical, cloud, and software defined data centers. Its
award-winning solutions portfolio secures the digital experience by
providing infrastructure, application, and corporate IT protection,
and availability services to enterprises globally. Radware’s
solutions empower enterprise and carrier customers worldwide to
adapt to market challenges quickly, maintain business continuity,
and achieve maximum productivity while keeping costs down. For more
information, please visit the Radware website.
Radware encourages you to join our community and follow us on:
Facebook, LinkedIn, Radware Blog, Twitter, YouTube, and Radware
Mobile for iOS and Android.
©2023 Radware Ltd. All rights reserved. Any Radware products and
solutions mentioned in this press release are protected by
trademarks, patents, and pending patent applications of Radware in
the U.S. and other countries. For more details, please
see: https://www.radware.com/LegalNotice/. All other
trademarks and names are property of their respective owners.
THIS PRESS RELEASE AND THE RADWARE CYBERSECURITY ADVISORY REPORT
ARE PROVIDED FOR INFORMATIONAL PURPOSES ONLY. THESE MATERIALS ARE
NOT INTENDED TO BE AN INDICATOR OF RADWARE'S BUSINESS PERFORMANCE
OR OPERATING RESULTS FOR ANY PRIOR, CURRENT OR FUTURE PERIOD.
Radware believes the information in this document is accurate in
all material respects as of its publication date. However, the
information is provided without any express, statutory, or implied
warranties and is subject to change without notice.
The contents of any website or hyperlinks mentioned in this
press release are for informational purposes and the contents
thereof are not part of this press release.
Safe Harbor Statement This press release
includes “forward-looking statements” within the meaning of the
Private Securities Litigation Reform Act of 1995. Any statements
made herein that are not statements of historical fact, including
statements about Radware’s plans, outlook, beliefs, or opinions,
are forward-looking statements. Generally, forward-looking
statements may be identified by words such as “believes,”
“expects,” “anticipates,” “intends,” “estimates,” “plans,” and
similar expressions or future or conditional verbs such as “will,”
“should,” “would,” “may,” and “could.” For example, when we say
that modern-day hacktivism with its barrage of denial-of-service
attacks is bolder, more determined, and more media-driven than ever
before, we are using a forward-looking statement. Because such
statements deal with future events, they are subject to various
risks and uncertainties, and actual results, expressed or implied
by such forward-looking statements, could differ materially from
Radware’s current forecasts and estimates. Factors that could cause
or contribute to such differences include, but are not limited to:
the impact of global economic conditions and volatility of the
market for our products; natural disasters and public health
crises, such as the coronavirus disease 2019 (COVID-19) pandemic; a
shortage of components or manufacturing capacity could cause a
delay in our ability to fulfill orders or increase our
manufacturing costs; our business may be affected by sanctions,
export controls, and similar measures, targeting Russia and other
countries and territories, as well as other responses to Russia’s
military conflict in Ukraine, including indefinite suspension of
operations in Russia and dealings with Russian entities by many
multi-national businesses across a variety of industries; our
ability to successfully implement our strategic initiative to
accelerate our cloud business; our ability to expand our operations
effectively; timely availability and customer acceptance of our new
and existing solutions; risks and uncertainties relating to
acquisitions or other investments; the impact of economic and
political uncertainties and weaknesses in various regions of the
world, including the commencement or escalation of hostilities or
acts of terrorism; intense competition in the market for cyber
security and application delivery solutions and in our industry in
general, and changes in the competitive landscape; changes in
government regulation; outages, interruptions, or delays in hosting
services or our internal network system; compliance with open
source and third-party licenses; the risk that our intangible
assets or goodwill may become impaired; our dependence on
independent distributors to sell our products; long sales cycles
for our solutions; changes in foreign currency exchange rates;
undetected defects or errors in our products or a failure of our
products to protect against malicious attacks; the availability of
components and manufacturing capacity; the ability of vendors to
provide our hardware platforms and components for our main
accessories; our ability to protect our proprietary technology;
intellectual property infringement claims made by third parties;
changes in tax laws; our ability to realize our investment
objectives for our cash and liquid investments; our ability to
attract, train, and retain highly qualified personnel; and other
factors and risks over which we may have little or no control. This
list is intended to identify only certain of the principal factors
that could cause actual results to differ. For a more detailed
description of the risks and uncertainties affecting Radware, refer
to Radware’s Annual Report on Form 20-F, filed with the Securities
and Exchange Commission (SEC) and the other risk factors discussed
from time to time by Radware in reports filed with, or furnished
to, the SEC. Forward-looking statements speak only as of the date
on which they are made and, except as required by applicable law,
Radware undertakes no commitment to revise or update any
forward-looking statement in order to reflect events or
circumstances after the date any such statement is made. Radware’s
public filings are available from the SEC’s website at www.sec.gov
or may be obtained on Radware’s website at www.radware.com.
Media Contact:Gerri
DyrekRadwareGerri.Dyrek@radware.com
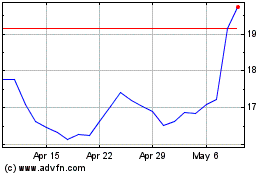
RADWARE (NASDAQ:RDWR)
Historical Stock Chart
From Jun 2024 to Jul 2024
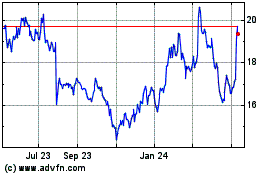
RADWARE (NASDAQ:RDWR)
Historical Stock Chart
From Jul 2023 to Jul 2024