February 2019’s Most Wanted Malware: Coinhive Quits While Still at the Top
March 11 2019 - 9:00AM

Check Point Research, the Threat Intelligence arm of Check Point®
Software Technologies Ltd. (NASDAQ: CHKP), a leading provider of
cyber security solutions globally, has published its latest Global
Threat Index for February 2019. The index reveals that, despite
shutting down on March 8th 2019, Coinhive has once again led the
Global Threat Index, marking the 15th consecutive month at the top
of the list.
Check Point researchers have also discovered several widespread
campaigns distributing the GandCrab ransomware that have targeted
Japan, Germany, Canada and Australia, among others. These
operations have emerged over the last two months, and Check Point’s
researchers noticed a new version of the ransomware being
distributed in one of the latest campaigns. The new version,
GandCrab V5.2, includes most of the features of the last, but with
a change in the encryption method that renders the decryption tool
ineffective.
In February, the most prevalent malware variants were
cryptominers. Coinhive remains the top malware, impacting 10% of
organizations worldwide. This follows a downward trend in
Coinhive’s global impact, from 18% in October 2018, to 12% in
January 2019, and now with a 2% drop this month. This decrease has
been caused by the rising cost of mining along with the decline in
Monero’s value. Cryptoloot rose to second place in February
replacing XMRig, and was followed by Emotet, an advanced,
self-propagate and modular Trojan, which replaced Jsecoin in third
place in the index.
Maya Horowitz, Threat Intelligence and Research Director at
Check Point commented: “As we saw in January, threat actors
continue to exploit new ways to distribute malware, while creating
new and more dangerous variants of existing malware forms.
GandCrab’s new version proves once again that although there are
seemingly static malware families that stay in the top malware list
for several months, they are actually evolving and developing to
evade detection. To effectively combat this, our researchers
continuously trace them based on their malware family DNA – so it’s
essential that organizations keep their security solutions fully
updated.”
February 2019’s Top 3 ‘Most Wanted’
Malware:*The arrows relate to the change in rank compared
to the previous month.
- ↔ Coinhive - Crypto Miner designed to perform
online mining of Monero cryptocurrency when a user visits a web
page without the user's knowledge or approval the profits with the
user. The implanted JavaScript uses a great deal of the
computational resources of end users’ machines to mine coins, and
may crash the system.
- ↑ Cryptoloot - Crypto-Miner
that uses the victim’s CPU or GPU power and existing resources for
crypto mining - adding transactions to the blockchain and releasing
new currency. It is a competitor to Coinhive, trying to pull the
rug under it by asking a smaller percentage of revenue from
websites.
- ↑ Emotet – Advanced, self-propagate and
modular Trojan. Emotet once used to employ as a banking Trojan, and
recently is used as a distributer to other malware or malicious
campaigns. It uses multiple methods for maintaining persistence and
evasion techniques to avoid detection. In addition, it can be
spread through phishing spam emails containing malicious
attachments or links.
This month Lotoor is the most prevalent Mobile malware,
replacing Hiddad at first place in the top mobile malware list.
Triada remains in third place.
February’s Top 3 ‘Most Wanted’ Mobile
Malware:1.
Lotoor- Hack tool that exploits vulnerabilities on
Android operating system in order to gain root privileges on
compromised mobile devices. 2.
Hiddad - Android malware which repackages
legitimate apps and then released them to a third-party store. Its
main function is displaying ads, however it is also able to gain
access to key security details built into the OS, allowing an
attacker to obtain sensitive user data.3.
Triada - Modular Backdoor for Android which grants
super user privileges to downloaded malware, as helps it to get
embedded into system processes. Triada has also been seen spoofing
URLs loaded in the browser.
Check Point’s researchers also analyzed the most exploited cyber
vulnerabilities. CVE-2017-7269 is still leading the top exploited
vulnerabilities with 45%. OpenSSL TLS DTLS Heartbeat Information
Disclosure is the second most prevalent vulnerability with a global
impact of 40%, followed by Web servers PHPMyAdmin Misconfiguration
Code Injection exploit, impacting 34% of organizations
worldwide.
February’s Top 3 ‘Most Exploited’
vulnerabilities:
- ↔ Microsoft IIS WebDAV ScStoragePathFromUrl
Buffer Overflow (CVE-2017-7269) - By sending a crafted
request over a network to Microsoft Windows Server 2003 R2 through
Microsoft Internet Information Services 6.0, a remote attacker
could execute arbitrary code or cause a denial of service
conditions on the target server. That is mainly due to a buffer
overflow vulnerability resulted by improper validation of a long
header in HTTP request.
- ↑ OpenSSL TLS DTLS Heartbeat Information Disclosure
(CVE-2014-0160; CVE-2014-0346) - An information disclosure
vulnerability exists in OpenSSL. The vulnerability is due to an
error when handling TLS/DTLS heartbeat packets. An attacker can
leverage this vulnerability to disclose memory contents of a
connected client or server.
- ↑ Web servers PHPMyAdmin Misconfiguration
Code Injection - A code injection vulnerability has been
reported in PHPMyAdmin. The vulnerability is due to PHPMyAdmin
misconfiguration. A remote attacker can exploit this vulnerability
by sending a specially crafted HTTP request to the target.
Check Point’s Global Threat Impact Index and its ThreatCloud Map
is powered by Check Point’s ThreatCloud intelligence, the largest
collaborative network to fight cybercrime which delivers threat
data and attack trends from a global network of threat sensors. The
ThreatCloud database holds over 250 million addresses analyzed for
bot discovery, more than 11 million malware signatures and over 5.5
million infected websites, and identifies millions of malware types
daily.
* The complete list of the top 10 malware families in June can
be found on the Check Point
Blog: http://blog.checkpoint.com/2019/03/11/february-2019s-most-wanted-malware-coinhive-quits-gandcrab-cryptomining-ransomware/
Check Point’s Threat Prevention Resources are available
at:
http://www.checkpoint.com/threat-prevention-resources/index.html
Follow Check Point Research via:Blog:
https://research.checkpoint.com/ Twitter:
https://twitter.com/_cpresearch_
About Check Point Research Check Point Research
provides leading cyber threat intelligence to Check Point Software
customers and the greater intelligence community. The research team
collects and analyzes global cyber-attack data stored on
ThreatCloud to keep hackers at bay, while ensuring all Check Point
products are updated with the latest protections. The research team
consists of over 100 analysts and researchers cooperating with
other security vendors, law enforcement and various CERTs.
About Check Point Software Technologies
Ltd.Check Point Software Technologies Ltd.
(www.checkpoint.com) is a leading provider of cyber security
solutions to governments and corporate enterprises globally.
Its solutions protect customers from cyber-attacks with an industry
leading catch rate of malware, ransomware and other types of
attacks. Check Point offers a multilevel security architecture that
defends enterprises’ cloud, network and mobile device held
information, plus the most comprehensive and intuitive one point of
control security management system. Check Point protects over
100,000 organizations of all sizes.
| INVESTOR CONTACT: |
MEDIA CONTACT: |
| Kip E. Meintzer |
Gil Messing |
| Check Point Software Technologies |
Check Point Software Technologies |
| +1.650.628.2040 |
+972.3753.4514 |
| ir@checkpoint.com |
press@checkpoint.com |
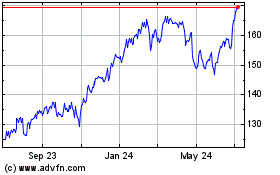
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From Aug 2024 to Sep 2024
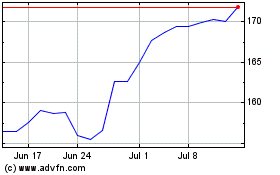
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From Sep 2023 to Sep 2024