Check Point Survey Reveals Nearly Half of Enterprises Are Victims of Social Engineering
September 21 2011 - 8:30AM
Marketwired
Check Point® Software Technologies Ltd. (NASDAQ: CHKP), the
worldwide leader in securing the Internet, today announced the
results of a new report revealing 48 percent of enterprises
surveyed have been victims of social engineering, experiencing 25
or more attacks in the past two years, costing businesses anywhere
from $25,000 to over $100,000 per security incident. The report,
The Risk of Social Engineering on Information Security, shows
phishing and social networking tools as the most common sources of
socially-engineering threats -- encouraging businesses to implement
a strong combination of technology and user awareness to minimize
the frequency and cost of attacks.
Socially-engineered attacks traditionally target people with an
implied knowledge or access to sensitive information. Hackers today
leverage a variety of techniques and social networking applications
to gather personal and professional information about an individual
in order to find the weakest link in the organization. According to
the global survey of over 850 IT and security professionals, 86
percent of businesses recognize social engineering as a growing
concern, with the majority of respondents (51%) citing financial
gain as the primary motivation of attacks, followed by competitive
advantage and revenge.
"The survey results show that nearly half of enterprises
surveyed know they have experienced social engineering attacks.
Knowing that many of these attacks go unnoticed, suggests that this
is a very wide and dangerous attack vector that must not be
ignored," said Oded Gonda, vice president of network security
products at Check Point Software Technologies.
While social engineering techniques rely on taking advantage of
a person's vulnerability, the prevalence of Web 2.0 and mobile
computing has also made it easier to obtain information about
individuals and has created new entry points to execute
socially-engineered attacks. New employees (60%) and contractors
(44%) who may be less familiar with corporate security policies
were considered to be the most susceptible to social engineering
techniques, in addition to contractors, assistants, human resources
and IT personnel.
"People are a critical part of the security process as they can
be misled by criminals and make mistakes that lead to malware
infections or unintentional data loss. Many organizations do not
pay enough attention to the involvement of users, when, in fact,
employees should be the first line of defense," added Gonda. "A
good way to raise security awareness among users is to involve them
in the security process and empower them to prevent and remediate
security incidents in real time."
To achieve the level of protection needed in modern day IT
environments, security needs to grow from a collection of disparate
technologies to an effective business process. Check Point 3D
Security helps companies implement a blueprint for security that
goes beyond technology and can educate employees by involving them
in the process. "Just as employees can make mistakes and cause
breaches or threats within the organization, they can also play a
large role in mitigating risks," added Gonda. With Check Point's
unique UserCheck™ technology, businesses can alert and educate
employees about corporate policies when accessing the corporate
network, data and applications -- helping companies minimize the
frequency, risk and costs associated with social engineering
techniques.
Key Findings from the Report:
- The Threat of Social Engineering is Real
-- 86 percent of IT and security professional are aware or highly
aware of the risks associated with social engineering.
Approximately 48 percent of enterprises surveyed admitted they have
been victims of social engineering more than 25 times in the last
two years.
- Social Engineering Attacks Are Costly --
Survey participants estimated each security incident costing
anywhere from $25,000 to over $100,000, including costs associated
with business disruptions, customer outlays, revenue loss and brand
damage.
- Most Common Sources of Social Engineering
-- Phishing emails were ranked the most common source of social
engineering techniques (47%), followed by social networking sites
that can expose personal and professional information (39%) and
insecure mobile devices (12%).
- Financial Gains are the Primary Motivation of
Social Engineering -- Financial gain was cited as the most
frequent reason for social engineered attacks, followed by access
to proprietary information (46%), competitive advantage (40%) and
revenge (14%).
- New Employees are Most Susceptible to Social
Engineering Techniques -- Survey participants believe new
employees are at high risk to social engineering risks, followed by
contractors (44%), executive assistants (38%), human resources
(33%), business leaders (32%) and IT personnel (23%). Regardless of
an employee's role within an organization, implementing proper
training and user awareness is a critical component of any security
policy.
- Lack of Proactive Training to Prevent Social
Engineering Attacks -- 34 percent of businesses do not have
any employee training or security policies in place to prevent
social engineering techniques, although 19 percent have plans
to.
The survey, The Risk of Social Engineering on Information
Security, was conducted in July and August 2011, surveying over 850
IT and security professionals located in the U.S., Canada, U.K.,
Germany, Australia and New Zealand. The survey sample represents
organizations of all sizes and across multiple industries,
including financial, industrial, defense, retail, healthcare and
education. Interested in learning more about social engineering and
want to add your input? Access the full report and take the online
survey here:
http://www.checkpoint.com/surveys/socialeng1509/socialeng.htm.
"Security is not just a problem for IT administrators; it must
be part of every professional's role. As the industry faces a rise
in sophisticated and targeted threats, user involvement makes
security technology smarter and more effective," concluded
Gonda.
About Check Point Software Technologies
Ltd. Check Point Software Technologies Ltd.
(www.checkpoint.com), the worldwide leader in securing the
Internet, provides customers with uncompromised protection against
all types of threats, reduces security complexity and lowers total
cost of ownership. Check Point first pioneered the industry with
FireWall-1 and its patented stateful inspection technology. Today,
Check Point continues to develop new innovations based on the
Software Blade Architecture, providing customers with flexible and
simple solutions that can be fully customized to meet the exact
security needs of any organization. Check Point is the only vendor
to go beyond technology and define security as a business process.
Check Point 3D Security uniquely combines policy, people and
enforcement for greater protection of information assets and helps
organizations implement a blueprint for security that aligns with
business needs. Customers include tens of thousands of
organizations of all sizes, including all Fortune and Global 100
companies. Check Point's award-winning ZoneAlarm solutions protect
millions of consumers from hackers, spyware and identity theft.
©2011 Check Point Software Technologies Ltd. All rights
reserved
Image Available:
http://www2.marketwire.com/mw/frame_mw?attachid=1739226 Image
Available:
http://www2.marketwire.com/mw/frame_mw?attachid=1739229
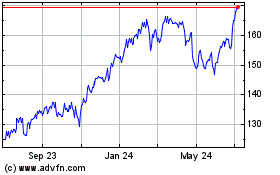
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From Apr 2024 to May 2024
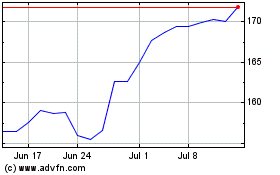
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From May 2023 to May 2024