Check Point and Ponemon Survey Validates Need for 3D Security
March 15 2011 - 8:30AM
Marketwired
Check Point® Software Technologies Ltd. (NASDAQ: CHKP), the
worldwide leader in securing the Internet, and the Ponemon
Institute, a leading privacy and information management research
firm, today released the findings of a global survey, Understanding
Security Complexity in 21st Century IT Environments, revealing that
security complexity is the number one obstacle that organizations
face today. Research shows organizations struggle with a growing
set of security priorities and limited employee awareness about
corporate policies in place. Key findings from the report validate
the importance of Check Point 3D Security, a new approach to
security that goes beyond technology and combines policy, people
and enforcement to help organizations align their IT policies with
their business needs.
According to the survey of over 2,400 IT security administrators
around the world, managing complex security environments is the
most significant challenge facing organizations today, with over 55
percent of companies using more than seven different vendors to
secure their network. Research shows that, when dealing with IT
consolidation, organizations struggle with minimizing the total
cost of ownership (TCO) and maximizing performance. To enforce better protection, organizations need to
approach security with a holistic view of their environment in
order to understand where risks can reside.
"To improve security in this day and age, organizations need to
accomplish a better understanding of their current environments and
prioritize their short and long term initiatives," said Juliette
Sultan, head of global marketing at Check Point Software
Technologies. "Check Point's approach with 3D Security goes beyond
technologies -- it also raises awareness on today's security
challenges, while providing better visibility and control to
organizations."
According to the survey, over 700 respondents believe the
primary concern with emerging technology adoption is compliance.
With the proliferation of cloud computing, mobility, Web 2.0 and
file sharing applications, organizations often struggle to apply
the appropriate levels of security across all layers of the
network, while also adhering to stringent compliance requirements.
Security and compliance in modern day environments begins with a
well-defined policy that aligns with an
organization's business needs and industry regulations.
While emerging technologies have created new methods of
communication and collaboration for enterprises, organizations
struggle with managing multifaceted IT environments; this often
contributes to greater security complexity and the risk of data
loss by employees or other insiders. In fact, 48.8 percent of
respondents believe their organizations' employees have little or
no awareness about their data protection or corporate policies. As
a result, more education and awareness is needed to help people realize their important role in maintaining the
organization's security profile. In addition, survey respondents
believe the ability to manage policies by user is a key
functionality to enforce better security overall, with 58 percent
citing identity awareness as a priority today and in the
future.
"Companies are constantly facing new and costly security risks
from both internal and external sources that can jeopardize the
business. Our research has shown that one cyber-attack can range
anywhere from $237,000 to $52 million," said Dr. Larry Ponemon,
chairman and founder, Ponemon Institute. "However, employees can
play a big role in being a first line of defense, helping their
company enforce stronger security measures and promoting more user
awareness within the organization."
Check Point's Software Blade Architecture™ and latest software,
Release R75 executes on the company's vision for 3D Security --
turning security into a three-dimensional business process by
combining policies, people and enforcement for stronger protection.
With a unique combination of innovative technology and user
awareness, organizations today are better positioned for
preemptively protecting their business against the next generation
of threats. For more information and access to the full report,
visit:
http://www.checkpoint.com/campaigns/3d-security/index.html.
The survey, Understanding Security Complexity in 21st Century IT
Environments, was independently conducted by the Ponemon Institute
in February 2011, surveying IT security administrators located in
the U.S., U.K. France, Germany and Japan. The survey sample
represents organizations of all sizes and across 14 different
industries, including financial, industrial, defense, retail,
healthcare and education.
"By educating end-users and enforcing security policies with a
holistic view of the organization, companies can minimize the
complexities associated with security and compliance in modern-day
business environments," concluded Sultan.
About the Ponemon Institute The Ponemon
Institute© is dedicated to advancing responsible information and
privacy management practices in business and government. To achieve
this objective, the Institute conducts independent research,
educates leaders from the private and public sectors and verifies
the privacy and data protection practices of organizations in a
variety of industries.
About Check Point Software Technologies
Ltd. Check Point Software Technologies Ltd.
(www.checkpoint.com), the worldwide leader in securing the
Internet, is the only vendor to deliver Total Security for
networks, data and endpoints, unified under a single management
framework. Check Point provides customers with uncompromised
protection against all types of threats, reduces security
complexity and lowers total cost of ownership. Check Point first
pioneered the industry with FireWall-1 and its patented stateful
inspection technology. Today, Check Point continues to innovate
with the development of the Software Blade architecture. The
dynamic Software Blade architecture delivers secure, flexible and
simple solutions that can be fully customized to meet the exact
security needs of any organization or environment. Check Point
customers include tens of thousands of businesses and organizations
of all sizes including all Fortune 100 companies. Check Point's
award-winning ZoneAlarm solutions protect millions of consumers
from hackers, spyware and identity theft.
©2011 Check Point Software Technologies Ltd. All rights
reserved
Media Contact Stephanie Look Check Point Software
Technologies +1 650.628.2171 press@us.checkpoint.com Investor
Contact Kip E. Meintzer Check Point Software Technologies +1
650.628.2040 ir@us.checkpoint.com
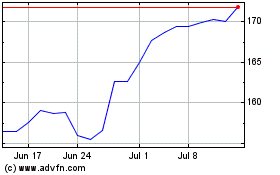
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From May 2024 to Jun 2024
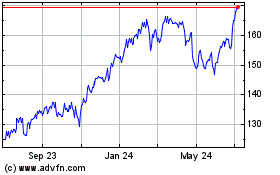
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From Jun 2023 to Jun 2024