Check Point Introduces 3D Security
February 08 2011 - 8:30AM
Marketwired
Check Point® Software Technologies Ltd. (NASDAQ: CHKP), the
worldwide leader in securing the Internet, today announced 3D
Security, a new vision that redefines security as a
three-dimensional business process by combining policies, people
and enforcement for stronger protection across all layers of
security. With 3D Security, corporations can now implement a
blueprint for security that goes beyond technology to ensure the
integrity of all information security.
"To achieve the level of protection needed in the 21st century,
security needs to grow from a mere collection of technologies to a
business process that incorporates three major dimensions --
policies, people and enforcement," said Gil Shwed, founder, chief
executive officer and chairman of Check Point Software
Technologies. "Check Point's 3D Security vision redefines security
as a business process that will enable companies to achieve the
required level of security while streamlining operations."
Check Point 3D Security enables organizations to transform
security into a business process by integrating the three following
dimensions: policy, people and enforcement.
- Policy: Security starts with a
well-defined and widely understood policy that outlines the
organization needs and strategies. Most organizations today do not
have such a policy; instead companies rely on lists of system-level
checks and on a collection of disparate technologies that do not
always deliver the desired level of security.
- People: Users of IT systems are a
critical part of the security process. It is often users who make
mistakes that result in malware infections and information leakage.
Most organizations do not pay much attention to the involvement of
users in the security process, when in fact, employees need to be
informed and educated on the security policy and their expected
behavior when surfing the Internet or sharing sensitive data. At
the same time, security should be as seamless and transparent as
possible and should not change the way users work.
- Enforcement: Security is about gaining
better control over the many layers of protection. Unfortunately,
corporations often find themselves losing control over the
disparate policies from various point products. In many cases
security systems generate violation reports but do not enforce the
policy. Companies should and can achieve a higher level of
visibility and control by consolidating their security
infrastructure, and using systems that prevent security incidents
rather than just detecting them.
"To improve security, businesses should rely on a combination of
technology, policy and people. Recognizing this need for 'defense
in depth,' Check Point's vision for 3D Security aligns with a lot
of the security needs and business priorities we hear from
customers," said John Grady, senior analyst, Security Products
research at IDC. "By adding an educational element and giving
employees the opportunity to participate in the security process,
businesses can significantly reduce their risks."
Today, Check Point also announced the release of Check Point
R75, the first major network security release to implement elements
of this multi-dimensional approach. For more information on Check
Point 3D Security and the Check Point R75 release, please visit:
http://www.checkpoint.com/campaigns/3d-security/index.html.
"Companies should look at security as a business enabler. Check
Point 3D Security redefines security as a business process that
will help customers develop a proactive blueprint for stronger,
better security," concluded Shwed.
About Check Point Software Technologies
Ltd. Check Point Software Technologies Ltd.
(www.checkpoint.com), the worldwide leader in securing the
Internet, is the only vendor to deliver Total Security for
networks, data and endpoints, unified under a single management
framework. Check Point provides customers with uncompromised
protection against all types of threats, reduces security
complexity and lowers total cost of ownership. Check Point first
pioneered the industry with FireWall-1 and its patented stateful
inspection technology. Today, Check Point continues to innovate
with the development of the Software Blade architecture. The
dynamic Software Blade architecture delivers secure, flexible and
simple solutions that can be fully customized to meet the exact
security needs of any organization or environment. Check Point
customers include tens of thousands of businesses and organizations
of all sizes including all Fortune 100 companies. Check Point's
award-winning ZoneAlarm solutions protect millions of consumers
from hackers, spyware and identity theft.
©2011 Check Point Software Technologies Ltd. All rights
reserved
Image Available:
http://www2.marketwire.com/mw/frame_mw?attachid=1504471
Add to Digg Bookmark with del.icio.us Add to Newsvine
Media Contact Stephanie Look Check Point Software
Technologies +1 650.628.2171 press@us.checkpoint.com Investor
Contact Kip E. Meintzer Check Point Software Technologies +1
650.628.2040 ir@us.checkpoint.com
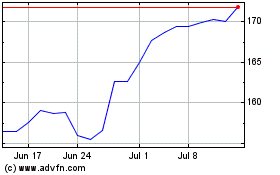
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From May 2024 to Jun 2024
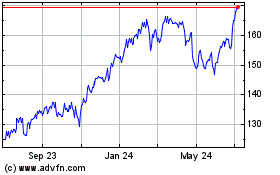
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From Jun 2023 to Jun 2024