Microsoft Releases Patch to Windows Flaw Found by NSA -- Update
January 14 2020 - 9:42PM
Dow Jones News
By Dustin Volz
WASHINGTON -- Microsoft Corp. released a patch to fix a software
vulnerability in its Windows operating system that could allow
hackers to breach or surveil targeted computer networks, after the
National Security Agency detected the flaw.
U.S. government officials described the vulnerability in Windows
10 -- Microsoft's most popular operating system -- as especially
severe and one that Microsoft customers should work to fix
immediately by updating their systems. Both Microsoft and the NSA
said they hadn't found evidence the flaw had been exploited for
malicious purposes.
"We are recommending that network owners expedite the patch
immediately, " Anne Neuberger, the chief of the NSA's newly
established cybersecurity directorate, told reporters on Tuesday.
The agency alerted Microsoft as soon as it discovered the bug, she
said.
In a sign of how severe officials considered the flaw, the
Department of Homeland Security issued an emergency directive on
Tuesday instructing federal agencies to take a series of steps to
apply patches to their systems immediately. DHS also said it would
hold calls with private industry partners warning about the risks
posed by the flaw, said Bryan Ware, a senior official at DHS's
Cybersecurity and Infrastructure Security Agency.
"A security update was released on January 14, 2020, and
customers who have already applied the update, or have automatic
updates enabled, are already protected," Jeff Jones, a Microsoft
senior director, said in a statement. "As always, we encourage
customers to install all security updates as soon as possible."
The flaw at issue involves a mistake in how Microsoft uses
digital signatures to verify software as authentic, which helps
block malware from being deployed on a computer. The error would
potentially enable hackers to install powerful malware on systems
undetected.
NSA hackers often uncover errors in major software that can be
exploited for malicious use. The agency has long said it notifies
vendors frequently of such flaws so they can be fixed, but it
sometimes retains and weaponizes them for offensive use, such as to
spy on a hostile foreign military's communications.
But the NSA has been criticized for not always alerting the
private sector to serious vulnerabilities. For example, Microsoft
publicly denounced the agency in 2017 after stolen NSA hacking
tools that were leaked online contributed to a global cyberattack
involving a Windows flaw.
In that instance, Microsoft President Brad Smith wrote a blog
post criticizing the U.S. government for keeping the flaw secret
for its own purposes, building a powerful cyber weapon and then
losing control of it. Mr. Smith at the time likened the situation
to "the U.S. military having some of its Tomahawk missiles
stolen."
The NSA said at the time that it had worked with Microsoft to
patch the problem after learning the hacking tools had been
compromised.
Later that year, the Trump administration released a
first-of-its-kind public road map outlining the administration's
policies regarding major cybersecurity flaws identified -- often in
popular consumer software -- by U.S. intelligence agencies. The
document lays out guidelines for when the government would disclose
the discovery of such flaws and when to keep them secret for
possible use in future offensive actions.
The public document that outlined the Vulnerabilities Equities
Process, or VEP, said that an annual report would be written "at
the lowest classification level permissible and include, at a
minimum, an executive summary written at an unclassified level"
that may be provided to Congress.
Years later, however, no such information has been made public,
and the lack of unclassified details has drawn frustration on
Capitol Hill, people familiar with the matter said.
NSA's acknowledgment Tuesday that it found the Microsoft flaw
and alerted the company was the first time the agency had done so
publicly, Ms. Neuberger said. The development represented a
philosophical shift at the NSA that has long sought to balance its
dual missions of foreign intelligence and cybersecurity, she
said.
"It's really the evolution of a mission," Ms. Neuberger said.
"We recognize that no government can secure its most critical
networks without the help of the private sector."
Write to Dustin Volz at dustin.volz@wsj.com
(END) Dow Jones Newswires
January 14, 2020 21:27 ET (02:27 GMT)
Copyright (c) 2020 Dow Jones & Company, Inc.
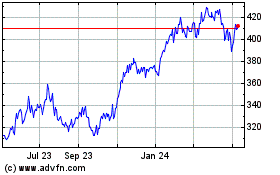
Microsoft (NASDAQ:MSFT)
Historical Stock Chart
From Mar 2024 to Apr 2024
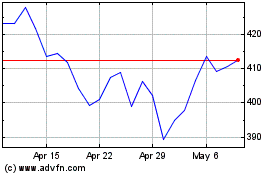
Microsoft (NASDAQ:MSFT)
Historical Stock Chart
From Apr 2023 to Apr 2024