CyberArk Labs Publishes New Research on Container Escape Routes
March 04 2019 - 8:30AM
Business Wire
Extends Industry-Leading Research into New
Attack Techniques in DevOps Environments
RSA Conference (Booth #6253 North) -- CyberArk (NASDAQ:
CYBR), the global leader in privileged access security, today
unveiled new research from CyberArk Labs demonstrating how
attackers can manipulate container defense-in-depth strategies to
gain access to an organization’s most valuable assets. The report
is the latest in a series of comprehensive CyberArk Labs research
reports examining how cyber attackers can utilize existing
vulnerabilities to circumvent container security and take advantage
of DevOps environments.
The blog, “The Route to Root: Container Escape Using Kernel
Exploitation,” describes how known kernel vulnerabilities can be
weaponized in container environments allowing an attacker to escape
to the host. The research found that Linux security controls like
seccomp and namespaces generally provide good security, limiting
the attacker’s ability to escape. However, in cases where the host
kernel is vulnerable, those security controls may be further
manipulated by weaponizing existing exploits to eventually escape
the container to the host.
“Containers offer clear operational benefits, and their default
security settings can make an attacker’s life quite difficult,”
said Lavi Lazarovitz, security research team lead, CyberArk Labs. “The goal of this research was to
understand how an attacker could manipulate existing
vulnerabilities in the host from within the container to escalate
privileges and eventually escape to the host. Understanding how
attackers work is important to improving how organizations can
mitigate damage and better protect their assets.”
CyberArk Labs is committed to researching post-exploit
environments to better understand the attack cycle and the movement
of attackers. In this case, the team adapted a publicly available
Linux kernel exploit code to escape a containerized environment and
describes mitigation strategies to limit damage.
For more CyberArk Labs research, visit the CyberArk Threat
Research Blog to read previous research in this area,
including:
- How I Hacked Play-with-Docker and
Remotely Ran Code on the Host
- Securing Kubernetes Clusters by
Eliminating Risky Permissions
Additionally, at RSA Conference CyberArk Labs will present a
session, “Highlighting Security Blind Spots in the DevOps Butler,”
on Tuesday, March 5 at 1:40 p.m. PST.
About CyberArkCyberArk (NASDAQ: CYBR) is the global
leader in privileged access security, a critical layer of IT
security to protect data, infrastructure and assets across the
enterprise, in the cloud and throughout the DevOps pipeline.
CyberArk delivers the industry’s most complete solution to reduce
risk created by privileged credentials and secrets. The
company is trusted by the world’s leading organizations, including
more than 50 percent of the Fortune 500, to protect against
external attackers and malicious insiders. A global company,
CyberArk is headquartered in Petach Tikva, Israel, with U.S.
headquarters located in Newton, Mass. The company also has offices
throughout the Americas, EMEA, Asia Pacific and Japan. To learn
more about CyberArk, visit www.cyberark.com, read the CyberArk
blogs or follow on Twitter via @CyberArk, LinkedIn or Facebook.
Copyright © 2019 CyberArk Software. All Rights Reserved. All
other brand names, product names, or trademarks belong to their
respective holders.
View source
version on businesswire.com: https://www.businesswire.com/news/home/20190304005115/en/
Media Relations Contacts:Brian Merrill, fama PRPhone:
+1-617-986-5005Email: cyberark@famapr.com
Liz Campbell, CyberArkPhone: +1-617-558-2191Email:
press@cyberark.com
Investor Relations Contact:Erica Smith, CyberArkPhone: +1
617-630-6426Email: ir@cyberark.com
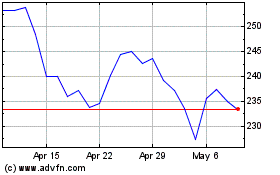
CyberArk Software (NASDAQ:CYBR)
Historical Stock Chart
From Mar 2024 to Apr 2024
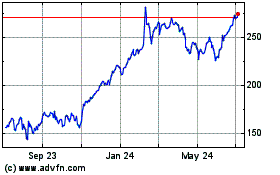
CyberArk Software (NASDAQ:CYBR)
Historical Stock Chart
From Apr 2023 to Apr 2024