Phil Quade, Chief Information Security Officer,
Fortinet“We, unfortunately, continue to see the
cybercriminal community mirror the strategies and methodologies of
nation-state actors, and the evolving devices and networks they are
targeting. Organizations need to rethink their strategy to better
future proof and manage cyber risks. An important first step
involves treating cybersecurity more like a science – doing the
fundamentals really well – which requires leveraging the
cyberspace fundamentals of speed and connectivity for
defense. Embracing a fabric approach to security, micro and
macro segmentation, and leveraging machine learning and automation
as the building blocks of AI, can provide tremendous opportunity to
force our adversaries back to square one.”
News Summary:Fortinet® (NASDAQ: FTNT), a global
leader in broad, integrated, and automated cybersecurity solutions,
today announced the findings of its latest quarterly Global
Threat Landscape Report. The research reveals that cybercriminals
continue to evolve the sophistication of their attack methods, from
tailored ransomware and custom coding for some attacks, to
living-off-the-land (LoTL) or sharing infrastructure to maximize
their opportunities. For a detailed view of the Threat Landscape
Index and subindices for exploits, malware, and botnets, as well as
some important takeaways for CISOs read the blog. Highlights of the
report follow:
Pre- and Post-Compromise Traffic: Research to
see if threat actors carry out phases of their attacks on different
days of the week demonstrates that cybercriminals are always
looking to maximize opportunity to their benefit. When comparing
Web filtering volume for two cyber kill chain phases during
weekdays and weekends, pre-compromise activity is roughly three
times more likely to occur during the work week, while
post-compromise traffic shows less differentiation in that regard.
This is primarily because exploitation activity often requires
someone to take an action such as clicking on a phishing email. In
contrast, command-and-control (C2) activity does not have this
requirement and can occur anytime. Cybercriminals understand this
and will work to maximize opportunity during the week when Internet
activity is the most prevalent. Differentiating between weekday and
weekend Web filtering practices is important to fully understand
the kill chain of various attacks.
Majority of Threats Share Infrastructure: The
degree to which different threats share infrastructure shows some
valuable trends. Some threats leverage community-use infrastructure
to a greater degree than unique or dedicated infrastructure. Nearly
60% of threats shared at least one domain indicating the majority
of botnets leverage established infrastructure. IcedID is an
example of this “why buy or build when you can borrow” behavior. In
addition, when threats share infrastructure they tend to do so
within the same stage in the kill chain. It is unusual for a threat
to leverage a domain for exploitation and then later leverage it
for C2 traffic. This suggests infrastructure plays a particular
role or function when used for malicious campaigns. Understanding
what threats share infrastructure and at what points of the attack
chain enables organizations to predict potential evolutionary
points for malware or botnets in the future.
Content Management Needs Constant
Management: Adversaries tend to move from
one opportunity to the next in clusters, targeting successfully
exploited vulnerabilities and technologies that are on the upswing,
to quickly maximize opportunity. An example of new technologies
getting a lot of attention from cybercriminals recently are Web
platforms that make it easier for consumers and businesses to build
Web presences. They continue to be targeted, even associated third
party plugins. This reinforces the fact that it is critical that
patches be applied immediately and to fully understand the
constantly evolving world of exploits to stay ahead of the
curve.
Ransomware Far From Gone: In general, previous
high rates of ransomware have been replaced with more targeted
attacks, but ransomware is far from gone. Instead, multiple attacks
demonstrate it is being customized for high-value targets and to
give the attacker privileged access to the network. LockerGoga is
an example of a targeted ransomware conducted in a multi-stage
attack. There is little about LockerGoga that sets it apart from
other ransomware in terms of functional sophistication, but while
most ransomware tools use some level of obfuscation to avoid
detection, there was little of it used when analyzed. This suggests
the targeted nature of the attack and a predetermination that the
malware would not be easily detected. In addition, like most other
ransomware, the main goal of Anatova is to encrypt as many files as
possible on the victim system, except that it systematically avoids
encrypting anything that can impact the stability of the system it
is infecting. It also avoids infecting computers that look like
they are being used for malware analysis or as honeypots. Both of
these ransomware variants demonstrate that security leaders need to
remain focused on patching and backups against commodity
ransomware, but targeted threats require more tailored defenses to
protect against their unique attack methods.
Tools and Tricks for Living Off the Land:
Because threat actors operate using the same business models as
their victims, to maximize their efforts, attack methods often
continue to develop even after gaining an initial entry. To
accomplish this, threat actors increasingly leverage dual-use tools
or tools that are already pre-installed on targeted systems to
carry out cyberattacks. This “living off the land” (LoTL) tactic
allows hackers to hide their activities in legitimate processes and
makes it harder for defenders to detect them. These tools also make
attack attribution much harder. Unfortunately, adversaries can use
a wide range of legitimate tools to accomplish their goals and hide
in plain sight. Smart defenders will need to limit access to
sanctioned administrative tools and log use in their
environments.
The Need for Dynamic and Proactive Threat
IntelligenceImproving an organization’s ability to not
only properly defend against current threat trends, but also
prepare for the evolution and automation of attacks over time
requires threat intelligence that is dynamic, proactive, and
available throughout the distributed network. This knowledge can
help identify trends showing the evolution of attack methods
targeting the digital attack surface and to pinpoint cyber hygiene
priorities based on where bad actors are focusing their efforts.
The value and ability to take action on threat intelligence is
severely diminished if it cannot be actionable in real time across
each security device. Only a security fabric that is broad,
integrated, and automated can provide protection for the entire
networked environment, from IoT to the edge, network core and to
multi-clouds at speed and scale.
Report and Index Overview The latest Fortinet
Threat Landscape Report is a quarterly view that represents the
collective intelligence of FortiGuard Labs, drawn from Fortinet’s
vast array of global sensors during Q1 2019. Research data covers
global and regional perspectives. Also included in the report is
the Fortinet Threat Landscape Index (TLI), comprised of individual
indices for three central and complementary aspects of that
landscape which are exploits, malware, and botnets, showing
prevalence and volume in a given quarter.
Additional Resources
- Read our blog for more information about this research or to
access the full threat report.
- View the Fortinet Threat Landscape Index and subindices for
botnets, malware, and exploits for Q1, 2019.
- For a more detailed view into the changing threats and events
driving the Fortinet Threat Landscape Index each week, check out
our Weekly Threat Briefs.
- Learn more about FortiGuard Labs and the FortiGuard Security
Services portfolio.
- Learn more about the FortiGuard Security Rating Service, which
provides security audits and best practices.
- Find out how Fortinet’s Security Fabric delivers
broad, integrated, and automated protection across an
organization’s entire digital attack surface from IoT to the edge,
network core and to multi-clouds.
- Read more about Fortinet’s Network Security Expert program ,
Network Security Academy program, and the FortiVets program.
- Follow Fortinet on Twitter, LinkedIn, Facebook,
YouTube, and Instagram.
About FortinetFortinet (NASDAQ: FTNT) secures
the largest enterprise, service provider, and government
organizations around the world. Fortinet empowers its customers
with intelligent, seamless protection across the expanding attack
surface and the power to take on ever-increasing performance
requirements of the borderless network - today and into the future.
Only the Fortinet Security Fabric architecture can deliver security
without compromise to address the most critical security
challenges, whether in networked, application, cloud, or mobile
environments. Fortinet ranks #1 in the most security appliances
shipped worldwide and more than 400,000 customers trust Fortinet to
protect their businesses. Learn more
at http://www.fortinet.com, the Fortinet Blog, or FortiGuard
Labs.
FTNT-O
Copyright © 2019 Fortinet, Inc. All rights reserved. The symbols
® and ™ denote respectively federally registered trademarks and
common law trademarks of Fortinet, Inc., its subsidiaries and
affiliates. Fortinet's trademarks include, but are not limited to,
the following: Fortinet, FortiGate, FortiGuard, FortiCare,
FortiManager, FortiAnalyzer, FortiOS, FortiADC, FortiAP,
FortiAppMonitor, FortiASIC, FortiAuthenticator, FortiBridge,
FortiCache, FortiCamera, FortiCASB, FortiClient, FortiCloud,
FortiConnect, FortiController, FortiConverter, FortiDB, FortiDDoS,
FortiExplorer, FortiExtender, FortiFone, FortiCarrier,
FortiHypervisor, FortiIsolator, FortiMail, FortiMonitor, FortiNAC,
FortiPlanner, FortiPortal, FortiPresence , FortiProxy,
FortiRecorder, FortiSandbox, FortiSIEM, FortiSwitch, FortiTester,
FortiToken, FortiVoice, FortiWAN, FortiWeb, FortiWiFi, FortiWLC,
FortiWLCOS and FortiWLM.
Other trademarks belong to their respective owners. Fortinet has
not independently verified statements or certifications herein
attributed to third parties and Fortinet does not independently
endorse such statements. Notwithstanding anything to the contrary
herein, nothing herein constitutes a warranty, guarantee, contract,
binding specification or other binding commitment by Fortinet or
any indication of intent related to a binding commitment, and
performance and other specification information herein may be
unique to certain environments. This news release may contain
forward-looking statements that involve uncertainties and
assumptions, such as statements regarding technology releases among
others. Changes of circumstances, product release delays, or other
risks as stated in our filings with the Securities and Exchange
Commission, located at www.sec.gov, may cause results to
differ materially from those expressed or implied in this press
release. If the uncertainties materialize or the assumptions prove
incorrect, results may differ materially from those expressed or
implied by such forward-looking statements and assumptions. All
statements other than statements of historical fact are statements
that could be deemed forward-looking statements. Fortinet assumes
no obligation to update any forward-looking statements, and
expressly disclaims any obligation to update these forward-looking
statements.
| Media
Contact: |
Investor
Contact: |
Analyst
Contact: |
| |
|
|
| John Welton |
Peter Salkowski |
Ron Davis |
| Fortinet, Inc. |
Fortinet, Inc. |
Fortinet, Inc. |
| 408-235-7700 |
408-331-4595 |
415-806-9892 |
| pr@fortinet.com |
psalkowski@fortinet.com |
rdavis@fortinet.com |
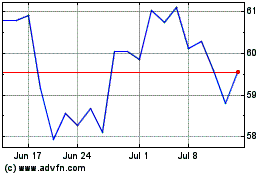
Fortinet (NASDAQ:FTNT)
Historical Stock Chart
From Mar 2024 to Apr 2024
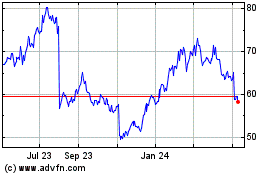
Fortinet (NASDAQ:FTNT)
Historical Stock Chart
From Apr 2023 to Apr 2024