Check Point Revolutionizes Security With New Software Blade Architecture
February 24 2009 - 2:00AM
Business Wire
Check Pointďż˝ Software Technologies Ltd. (Nasdaq:CHKP), the
worldwide leader in securing the Internet, today announced its new
Software Blade architecture, the industry�s first architecture to
meet businessesďż˝ need for total, flexible and manageable security.
The new architecture empowers businesses with the ability to select
from a library of over 20 software blades the exact security
protections necessary and dynamically tailor security gateways for
different environments and sites.
Security environments of large, medium and small companies are
becoming more complex as they attempt to address continually
evolving threats. Many organizations complain about the need to use
multiple products, hardware platforms, management consoles and
daily monitoring systems. Check Point Software Blade architecture
offers businesses a common platform to deploy independent, modular
and interoperable security applications or �software blades� � such
as firewall, virtual private network (VPN), intrusion prevention
system (IPS), anti-virus, policy management or provisioning blades.
The architecture allows customers to select the exact security
software blades they need and then to combine them into a single,
centrally managed gateway.
�We are proud to introduce a new paradigm in security; one that
meets today�s complex threat environment with refreshing
simplicity,ďż˝ said Gil Shwed, chairman and chief executive officer
at Check Point. �To address each new risk businesses can now
consolidate multiple security systems by simply activating software
blades on their Check Point security platform. Check Point Software
Blade architecture gives businesses the flexibility to create a
unified security infrastructure that can be extended to fit their
growing needs.ďż˝
With the new Software Blade architecture customers will be able
to move functionality from one system to another, consolidate or
split functionalities between systems and guarantee performance for
each software blade by setting usage thresholds. All these
capabilities will enable customers to scale their security needs
while reducing security cost of ownership.
For example, a business could start with a single core, single
blade firewall system. That business can turn on functionalities
such as VPN, network anti-virus, VoIP security and intrusion
prevention by adding four blades turning their system into a five
blade system. To meet their performance needs the system can be
upgraded into a two, four or eight core computing system, enabling
multi-gigabit performance with the extended functionality.
�For businesses a unified line of gateways with centralized
management securing both external and internal security zones is
very beneficial,ďż˝ said Charles Riordan, business leader, network
security and audit at Visa Inc. �Moving to Check Point Software
Blade architecture with its performance enhancing core associations
is something enterprises like Visa may well take advantage of
moving into the future.�Bottom line is Check Point�s new
architecture and foresight looks to be spot on with what the
industry needs.ďż˝
Key benefits of the Check Point Software Blade Architecture
include:
- Flexibility ďż˝ Provides the right
level of protection at the right level of investment
- Manageability ďż˝ Enables fast
deployment of security functions and increased productivity through
central management of software blades
- Total Security ďż˝ Provides the
right level of security, at all enforcement points, and at all
layers of the network
- Guaranteed performance ďż˝ Enables
performance setting per blade to ensure guaranteed performance
- Lower TCO - Protects investment
by enabling consolidation and leveraging existing
infrastructure
�IDC expects the next generation of security products to offer
more flexibility in both features and deployment options, a trend
that is accelerated by the current state of the economy and the
demand for more cost-effective solutions. Check Point�s new
Software Blade architecture offers customers important flexibility
and customization options to deliver security tailored to each
enterprise�s specific environment,� said Andrew Hanson, network and
endpoint security analyst at IDC. �Software Blades� modular
approach can also supply cost saving benefits as they can be
deployed dynamically without the need to upgrade hardware, firmware
or drivers.ďż˝
Software blades can be deployed on Check Point UTM-1ďż˝ or
Power-1ďż˝ appliances as well as open servers. Additional information
on the new Check Point Software Blade architecture can be found at:
www.checkpoint.com/products/softwareblades/architecture/index.html.
�Check Point Software Blades offer customers a revolutionary
architecture to create a security system that is uniquely flexible
and can expand to optimize their existing infrastructure,ďż˝
concluded Shwed.
Pricing and Availability
Check Point Software Blades are available immediately and can be
purchased through Check Point�s worldwide network of value-added
resellers. For information on pricing and licensing, visit
https://pricelist.checkpoint.com. To find a Check Point partner,
visit www.checkpoint.com.
About Check Point Software Technologies Ltd.
Check Point Software Technologies Ltd. (www.checkpoint.com) is
the leader in securing the Internet. Check Point offers total
security solutions featuring a unified gateway, single endpoint
agent and single management architecture, customized to fit
customersďż˝ dynamic business needs. This combination is unique and
is a result of our leadership and innovation in the enterprise
firewall, personal firewall/endpoint, data security and VPN
markets.
Check Point�s pure focus is on information security. Through its
NGX platform, Check Point delivers a unified security architecture
to protect business communications and resources, including
corporate networks and applications, remote employees, branch
offices and partner extranets. The company also offers
market-leading endpoint and data security solutions with Check
Point Endpoint Security products, protecting and encrypting
sensitive corporate information stored on PCs and other mobile
computing devices. Check Point's award-winning ZoneAlarm solutions
protect millions of consumer PCs from hackers, spyware and identity
theft. Check Point solutions are sold, integrated and serviced by a
network of Check Point partners around the world and its customers
include 100 percent of Fortune 100 companies and tens of thousands
of businesses and organizations of all sizes.
�2009 Check Point Software Technologies Ltd. All rights
reserved.
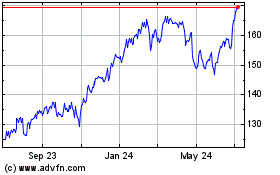
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From Aug 2024 to Sep 2024
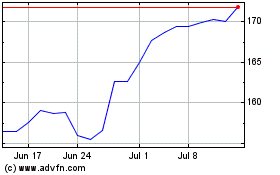
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From Sep 2023 to Sep 2024