Intel Editorial: Intel CET Answers Call to Protect Against Common Malware Threats
June 15 2020 - 9:00AM
Business Wire
Intel Control-Flow Enforcement Technology
Available in 'Tiger Lake' Adds CPU-Level Protection Against a
Common Class of Malware
The following is an opinion editorial by Tom Garrison of Intel
Corporation.
This press release features multimedia. View
the full release here:
https://www.businesswire.com/news/home/20200615005120/en/
Intel has announced Intel Control-Flow
Enforcement Technology. It delivers CPU-level security capabilities
to help protect against common malware attack methods that have
been difficult to mitigate with software alone. (Credit: Intel
Corporation)
The security of our customers’ data is a top priority at Intel.
As part of Intel’s Security First Pledge, our engineers continue to
deliver advancements to help safeguard our technology from evolving
cyber-threats. It begins with designing and engineering security
features into our products and continues in our work with the
industry to move security innovation forward.
Today, we are announcing a new security capability. Intel®
Control-Flow Enforcement Technology (Intel CET) will be first
available on Intel’s upcoming mobile processor code-named "Tiger
Lake." Intel CET delivers CPU-level security capabilities to help
protect against common malware attack methods that have been a
challenge to mitigate with software alone.
Intel CET is designed to protect against the misuse of
legitimate code through control-flow hijacking attacks – widely
used techniques in large classes of malware. Intel CET offers
software developers two key capabilities to help defend against
control-flow hijacking malware: indirect branch tracking and shadow
stack. Indirect branch tracking delivers indirect branch protection
to defend against jump/call-oriented programming (JOP/COP) attack
methods. Shadow stack delivers return address protection to help
defend against return-oriented programming (ROP) attack methods.
These types of attack methods are part of a class of malware
referred to as memory safety issues and include tactics such as the
corruption of stack buffer overflow and use-after-free.
According to TrendMicro’s Zero Day Initiative (ZDI), 63.2% of
the 1,097 vulnerabilities disclosed by ZDI from 2019 to today were
memory safety related. These malware types target operating systems
(OS), browsers, readers and many other applications. It takes deep
hardware integration at the foundation to deliver effective
security features with minimal performance impact.
Intel was the first to tackle these complex security challenges,
and we remain committed to working with the industry to drive
security innovation. We recognized that scaling OS and application
adoption to truly solve the problem would require industrywide
collaboration. To accelerate adoption, we published the Intel CET
specifications in 2016. Additionally, Intel and Microsoft have been
working closely to prepare Windows 10 and developer tools so
applications and the industry at large can offer better protection
against control-flow hijacking threats.
Microsoft’s upcoming support for Intel CET in Windows 10 is
called Hardware-enforced Stack Protection, and a preview of it is
available today in Windows 10 Insider Previews. This new
Hardware-enforced Stack Protection feature only works on chipsets
with Intel CET instructions. It relies on a new CPU architecture
that is compliant with Intel CET specifications. For applications
running on an OS that supports Intel CET, users can expect detailed
guidance from our partners on how applications “opt-in” for
protection.
The significance of Intel CET is that it is built into the
microarchitecture and available across the family of products with
that core. While Intel vPro® platforms with Intel® Hardware Shield
already meet and exceed the security requirements for Secured-core
PCs, Intel CET further extends advanced threat protection
capabilities. Intel CET is also expected to be available in future
desktop and server platforms.
As our work here shows, hardware is the bedrock of any security
solution. Security solutions rooted in hardware provide the
greatest opportunity to provide security assurance against current
and future threats. Intel hardware, and the added assurance and
security innovation it brings, help to harden the layers of the
stack that depend on it.
The security of our products is an ongoing priority, not a
one-time event. Together with our partners and customers, we
continue to build a more trusted foundation for all computing
systems.
Tom Garrison is vice president of the Client Computing Group and
general manager of Security Strategies and Initiatives (SSI) at
Intel Corporation.
About Intel
Intel (Nasdaq: INTC) is an industry leader, creating
world-changing technology that enables global progress and enriches
lives. Inspired by Moore’s Law, we continuously work to advance the
design and manufacturing of semiconductors to help address our
customers’ greatest challenges. By embedding intelligence in the
cloud, network, edge and every kind of computing device, we unleash
the potential of data to transform business and society for the
better. To learn more about Intel’s innovations, go to
newsroom.intel.com and intel.com.
Intel technologies may require enabled hardware, software or
service activation. No product or component can be absolutely
secure. Your costs and results may vary.
© Intel Corporation. Intel, the Intel logo and other Intel marks
are trademarks of Intel Corporation or its subsidiaries. Other
names and brands may be claimed as the property of others.
View source
version on businesswire.com: https://www.businesswire.com/news/home/20200615005120/en/
Jennifer Foss 425-765-3485 Jennifer.Foss@intel.com
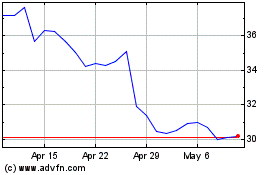
Intel (NASDAQ:INTC)
Historical Stock Chart
From Mar 2024 to Apr 2024
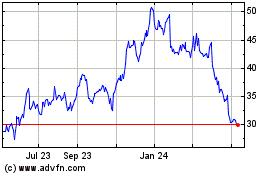
Intel (NASDAQ:INTC)
Historical Stock Chart
From Apr 2023 to Apr 2024