By Dustin Volz and Robert McMillan
Russian hackers linked to the 2016 election cyberattacks on the
Democratic Party are widening their targeting for the coming
midterms to include the U.S. Senate and well-connected conservative
groups, according to new research from Microsoft Corp.
Microsoft last week took down six internet domains registered by
a Russian hacking group that sought to mimic legitimate websites.
The domains appeared to mark the early stages of spear-phishing
attacks intended to compromise political operatives working for or
around the targeted organizations.
One of the domains mimicked the International Republican
Institute, Microsoft said. The IRI is a Republican-leaning think
tank that has counted Sens. Lindsey Graham, John McCain and Marco
Rubio -- all of whom advocate tough policies against Russia --
among its board members. Other targets include the Hudson
Institute, which is a Washington, D.C.-based conservative think
tank, as well as the U.S. Senate, Microsoft said.
Microsoft said it had no evidence any of the spoofed internet
domains were used in any successful cyberattacks before the company
seized control of them.
The domains were registered by a hacking group associated with
Moscow's military intelligence agency, the GRU. In the past, the
hackers, commonly referred to as Fancy Bear or Strontium, have used
phishing emails to direct targets to fake websites designed to
resemble legitimate ones where they steal login credentials,
according to security researchers.
After slowing efforts last year targeting the American political
system, the Russian hacking group has launched a number of
attempted digital intrusions in recent months, Microsoft said.
Missouri Democrat Sen. Claire McCaskill last month disclosed that
her office had been a target of a phishing scam.
U.S. intelligence officials have said the 2016 break-ins were
carried out by Russian intelligence. Last month, special counsel
Robert Mueller charged a dozen Russian intelligence officers in the
hacks. Russia has denied involvement in the hacking, and said the
indictment was designed to "spoil the atmosphere" of the July
meeting between Donald Trump and Russian President Vladimir
Putin.
"We are not surprised by this," said David Tell, a spokesman for
the Hudson Institute, in response to the new Microsoft findings.
"There can't be an even peripherally involved office in politics in
Washington that does not routinely get emails ending in .ru with
weird attachments in them."
Mr. Tell said that the institute's work on promoting American
global leadership and tracking kleptocratic regimes would make it
an especially appealing target for Moscow.
The attack was "consistent with the campaign of meddling that
the Kremlin has waged against organizations that support democracy
and human rights," said IRI President Daniel Twining in a
statement. A spokeswoman for the Senate's Sergeant at Arms, which
handles the chamber's computer protection, declined to comment on
the alleged phishing attempts.
"There is a breadth that is starting to match what we saw in
2016," said Brad Smith, president and chief legal officer of
Microsoft, in an interview. Notably, Mr. Smith said, the efforts
appeared to be targeting both political parties, in an apparent
shift in tactics.
Disclosure of the hacking attempts also comes as senior
officials in the Trump administration, including Vice President
Mike Pence, have issued warnings about Russia's intent to interfere
in future elections and vowed to halt such attacks. Mr. Trump, who
has been criticized for not sending clear signals to Moscow that
cyberattacks targeting American elections won't be tolerated,
signed an order last week rescinding classified Obama-era rules
that limited the offensive use of cyberweapons.
Microsoft has historically been able to gain control of phishing
domains such as these by claiming trademark violations when the
domains masquerade as the firm's websites.
Microsoft hasn't seen as many attempted intrusions as it did
during the 2016 presidential cycle, Mr. Smith said, though he
cautioned that could be due in part to Russia relying on more
sophisticated tools.
"At the same time given that we have developed this tactic, we
have to assume there are smart people on the other side who are
shifting tactics or at least finding new ways to elude this type of
response," Mr. Smith said.
Microsoft is taking new steps to give candidates, political
groups and think tanks more information on cyberthreats and how to
protect from them, Mr. Smith said.
Both the Hudson Institute and International Republican Institute
comprise part of the old-guard Republican firmament of Washington,
which has seen its policy priorities, such as free trade and a
globally engaged foreign policy, repeatedly challenged by Mr.
Trump.
The Hudson Institute hosted Dan Coats, the director of national
intelligence, last month at a cybersecurity event at which Mr.
Coats likened the cybersecurity threat posed to the U.S. by Russian
hackers to terrorist threats before Sept. 11, 2001. "The warning
lights are blinking red again," Mr. Coats said during a speech.
Write to Robert McMillan at Robert.Mcmillan@wsj.com
(END) Dow Jones Newswires
August 21, 2018 00:15 ET (04:15 GMT)
Copyright (c) 2018 Dow Jones & Company, Inc.
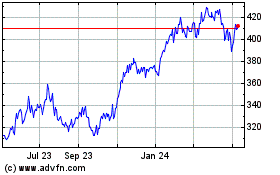
Microsoft (NASDAQ:MSFT)
Historical Stock Chart
From Mar 2024 to Apr 2024
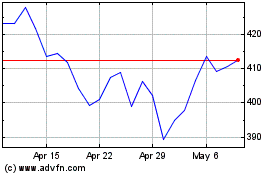
Microsoft (NASDAQ:MSFT)
Historical Stock Chart
From Apr 2023 to Apr 2024