Accenture Security Report Identifies Top Cyber Threats of 2017
July 25 2017 - 8:59AM
Business Wire
Destructive ransomware, alternative
crypto-currencies and increased use of deception tactics among
threats driving even more lucrative criminal marketplace
With recent large-scale cyber attacks signaling a growing front
in destructive threats and business impact, a new midyear report
from iDefense, part of Accenture Security (NYSE:ACN), reveals how
threat actors are continuing to evolve their ability to avoid
detection. Based on in-depth analysis, the report anticipates a
growth in the number of threat actors who are rapidly expanding
their capabilities due to factors such as the proliferation of
affordable, customizable and accessible tools and exploits.
This Smart News Release features multimedia.
View the full release here:
http://www.businesswire.com/news/home/20170725005441/en/
Accenture Security Report Identifies Top
Cyber Threats of 2017 (Photo: Business Wire)
The 2017 Cyber Threatscape Report examines key trends during the
first half of 2017 and explores how cyber incidents may evolve over
the next six months. This report relies on iDefense intelligence
collection, research, and analysis including research using primary
and secondary open-source materials. It covers the increased
prevalence of destructive attacks and adversary denial and
deception tactics; the aggressive use of information operations by
nation-states; growth in the numbers and diversity of threat
actors; as well as the greater availability of exploits, tools,
encryption, and anonymous payment systems available to malicious
actors.
“The first six months of 2017 have seen an evolution of
ransomware producing more viral variants unleashed by potential
state-sponsored actors and cybercriminals. Our findings confirm
that a new bar has been set for cybersecurity teams across all
industries to defend their assets in the coming months,” said Josh
Ray, managing director at Accenture Security. “While the occurrence
of new cyber attack methods is not going away, there are immediate
actions companies can take to better protect themselves against
malicious ransomware and reduce the impact of security
breaches.”
Other notable observations from the report include:
- Reverse Deception Tactics –
Increasing cybercriminal use of deception tactics including
anti-analysis code, steganography, and expendable
command-and-control servers used for concealment of stolen data.
Greater public reporting on cyber threat activity and attribution
may accelerate this denial and deception trend, increasing the cost
of cyber defense efforts and resource allocations.
- Sophisticated Phishing Campaigns
– Cybercriminals continue to craft familiar lures—subject lines
mentioning invoices, shipping, resumes, wire transfers, missed
payments— but ransomware is displacing banking trojans as one of
the most prevalent types of malware delivered via phishing
techniques.
- Strategic Use of Information
Operations – Escalation of espionage and disruption activity
from state-sponsored actors may likely continue in response to
fulfilling strategic collection requirements and geopolitical
triggers such as economic sanctions, military exercises and
religious conflicts.
- Alternative Crypto-Currencies –
Bitcoin continues to be the currency of choice among
cybercriminals, however, the need to better conceal transactions is
forcing cybercriminals to either develop and leverage bitcoin
laundering techniques or adopt alternative cryptocurrencies.
- DDoS-for-Hire Services –
Distributed denial of service (DDoS)-for-hire services have given
way to a thriving DDoS-for-hire botnet ecosystem leading to threat
actors gaining greater access to increasingly potent and affordable
DDoS-for-hire tools and services.
Effective components for a business continuity plan include:
- Adopt proactive prevention –
Recognize phishing scams through prevention training and awareness
programs. Make it easy for employees to report fraudulent e-mails
quickly, and keep testing internally to prove the training is
working.
- Elevate e-mail controls –
Maintain strong spam filters and authentication. Scan incoming and
outgoing e-mails to detect threats and filter executable files.
Consider a cloud-based e-mail analytics solution.
- Insulate your infrastructure –
Remove or limit local workstation admin rights or seek out the
right configuration combinations (e.g. virus scanners, firewalls).
Regularly patch operating systems and applications.
- Plan for continuity – To avoid
paying any ransom have a strong cyber resilience plan for recovery
that is regularly reviewed, updated, and tested.
About Accenture
Accenture is a leading global professional services company,
providing a broad range of services and solutions in strategy,
consulting, digital, technology and operations. Combining unmatched
experience and specialized skills across more than 40 industries
and all business functions – underpinned by the world’s largest
delivery network – Accenture works at the intersection of business
and technology to help clients improve their performance and create
sustainable value for their stakeholders. With more than 411,000
people serving clients in more than 120 countries, Accenture drives
innovation to improve the way the world works and lives. Visit us
at www.accenture.com.
Accenture Security helps organizations build
resilience from the inside out, so they can confidently
focus on innovation and growth. Leveraging its global network of
cybersecurity labs, deep industry understanding across client value
chains and services that span the security lifecycle, Accenture
protects organizations’ valuable assets, end-to-end. With services
that include strategy and risk management, cyber defense,
digital identity, application security and managed security,
Accenture enables businesses around the world to defend against
known sophisticated threats, and the unknown. Follow us
@AccentureSecure on Twitter or visit us at
www.accenture.com/security.
View source
version on businesswire.com: http://www.businesswire.com/news/home/20170725005441/en/
AccentureAlison Geib, + 1
703-947-4404alison.geib@accenture.com
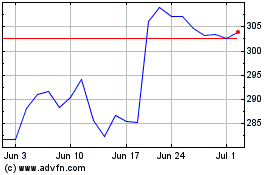
Accenture (NYSE:ACN)
Historical Stock Chart
From Mar 2024 to Apr 2024
Accenture (NYSE:ACN)
Historical Stock Chart
From Apr 2023 to Apr 2024
