New CyberArk Capabilities Detect and Alert on
High-Risk Privileged Activity During User Sessions to Help Security
Teams Better Prioritize Threat Response
RSA CONFERENCE 2017– Booth #N3209 – CyberArk (NASDAQ:
CYBR), the company that protects organizations from cyber attacks
that have made their way inside the network perimeter, today
announced advanced insider threat detection capabilities available
through the CyberArk Privileged Account Security Solution to
automatically detect and alert on high-risk privileged activity
during user sessions and enable rapid response to in-progress
attacks.
With this release, CyberArk is delivering a new integration that
provides deeper insights into privileged activity across an
organization. A new data feed from CyberArk Privileged Session
Manager into CyberArk Privileged Threat Analytics, both part of the
CyberArk Privileged Account Security Solution, enables security
teams to receive customizable, prioritized alerts with granular
detail on high-risk privileged activity, watch suspicious sessions
in-progress, and terminate potentially malicious sessions to
disrupt potential attacks – all from one platform. By helping to
prioritize the review of privileged session logs, CyberArk can also
improve efficiency and shorten IT audit cycles to reduce costs.
Analyze High-Risk Privileged Activity to Stop Insider
AttacksAn insider who has gained access to privileged
credentials can initiate seemingly legitimate privileged user
sessions. Without the automated real-time detection and alerting on
risky activities within privileged sessions, an inside attacker may
operate undetected.
According to the SANS Institute, only nine percent ranked their
insider threat prevention methods as ‘very effective.’1 Most
organizations are overwhelmed by alerts, with 93 percent unable to
triage all relevant threats.2
The CyberArk solution improves security teams’ ability to
respond to external threats and malicious insiders with the
flexibility to extend detection beyond initial account logon
events. CyberArk allows security operations teams to assign risk
levels that are most relevant to their organization, monitor and
analyze actual behavior during a privileged session, identify
activity or commands that may indicate compromise, and prioritize
threat response based on alert severity.
Improve Productivity and Cost Savings for Audit and
ComplianceBased on CyberArk’s experience working with
customers, an average large corporation could have thousands of
privileged user sessions running on its IT infrastructure each day.
With enormous amounts of security data and privileged session
recordings to sift through, it becomes nearly impossible for audit
and compliance teams to identify risky or suspicious activity.
Furthermore, to meet certain global audit and compliance
regulations, dozens of full time auditors who are focused solely on
this task are often required to manually review a certain
percentage of all privileged session activity.
CyberArk delivers a new level of automation for compliance and
audit teams. The CyberArk solution applies risk scores based on
customer-defined policies to live and recorded sessions, empowering
auditors to prioritize or deprioritize privileged activity for
review. This enables them to work more efficiently, deliver greater
value to the business, accelerate audit cycles to reduce total IT
audit costs, and create a consistent approach for examining the
risks associated with privileged activity.
“By delivering an integrated solution for threat detection based
on privileged sessions, we help identify malicious activity hidden
in a sea of legitimate data, and enable rapid threat response,”
said Roy Adar, senior vice president, product management, CyberArk.
“In addition, organizations could potentially save thousands of man
hours that would have been spent manually reviewing sessions. These
time and cost savings are especially important in context of
requirements like those associated with the Monetary Authority of
Singapore (MAS) Technology Risk Management (TRM) guidelines and
similar global regulations.”
Supporting this announcement, cyber security experts from
CyberArk Labs and customers’ security operations teams identified
some examples of commands that are frequently associated with
malicious – or accidentally damaging – behavior. Highly sensitive
commands that were frequently cited as being indicative of risk
include “mmc.exe, Active Directory Users and Computers” on Windows
systems, as well as commands containing the terms “authorized_keys”
and “sudoers” on *nix systems.
To learn more, read the CyberArk blog: “Spot Insider Threats: 10
Commands Commonly Used During the Cyber Attack Cycle.”
AvailabilityCyberArk Privileged Session Manager v9.8 and
CyberArk Privileged Threat Analytics v3.4 are available now.
Contact CyberArk sales to learn more about bundled pricing
options.
Additional Resources
- Video - CyberArk Brief: Detecting &
Responding to Insider Threats
- eBook - The Danger Within: Unmasking
Insider Threats
1- "Insider Threats and the Need for Fast and Directed
Response," April 20152- "McAfee Labs Threats Report," December
2016
About CyberArkCyberArk is the only security company
focused on eliminating the most advanced cyber threats; those that
use insider privileges to attack the heart of the enterprise.
Dedicated to stopping attacks before they stop business, CyberArk
proactively secures against cyber threats before attacks can
escalate and do irreparable damage. The company is trusted by the
world’s leading companies – including more than 45 percent of the
Fortune 100 – to protect their highest value information assets,
infrastructure and applications. A global company, CyberArk is
headquartered in Petach Tikvah, Israel, with U.S. headquarters
located in Newton, Mass. The company also has offices throughout
EMEA and Asia Pacific and Japan. To learn more about CyberArk,
visit www.cyberark.com, read the company
blog, http://www.cyberark.com/blog/, follow on
Twitter @CyberArk or Facebook
at https://www.facebook.com/CyberArk.
Forward-Looking StatementsThis release may contain
forward-looking statements, which express the current beliefs and
expectations of CyberArk’s (the “Company”) management. In some
cases, forward-looking statements may be identified by terminology
such as “believe,” “may,” “estimate,” “continue,” “anticipate,”
“intend,” “should,” “plan,” “expect,” “predict,” “potential” or the
negative of these terms or other similar expressions. Such
statements involve a number of known and unknown risks and
uncertainties that could cause the Company’s future results,
performance or achievements to differ significantly from the
results, performance or achievements expressed or implied by such
forward-looking statements. Important factors that could cause or
contribute to such differences include risks relating to: changes
in the rapidly evolving cyber threat landscape; failure to
effectively manage growth; near-term declines in the Company’s
operating and net profit margins and its revenue growth rate; real
or perceived shortcomings, defects or vulnerabilities in the
Company’s solutions or internal network system, or the failure of
the Company’s customers or channel partners to correctly implement
the Company’s solutions; fluctuations in quarterly results of
operations; the inability to acquire new customers or sell
additional products and services to existing customers; competition
from IT security vendors; the Company’s ability to successfully
integrate recent and or future acquisitions; and other factors
discussed under the heading “Risk Factors” in the Company’s most
recent annual report on Form 20-F filed with the Securities and
Exchange Commission. Forward-looking statements in this release are
made pursuant to the safe harbor provisions contained in the
Private Securities Litigation Reform Act of 1995. These
forward-looking statements are made only as of the date hereof, and
the Company undertakes no obligation to update or revise the
forward-looking statements, whether as a result of new information,
future events or otherwise.
Copyright © 2017 CyberArk Software. All Rights Reserved. All
other brand names, product names, or trademarks belong to their
respective holders.
View source
version on businesswire.com: http://www.businesswire.com/news/home/20170214005208/en/
Media Relations Contacts:fama PRBrian Merrill,
+1-617-986-5005cyberark@famapr.comorCyberArkLiz Campbell,
+1-617-558-2191press@cyberark.comorInvestor Relations
Contact:CyberArkErica Smith, +1-617-630-6426ir@cyberark.com
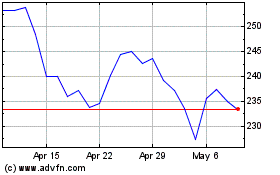
CyberArk Software (NASDAQ:CYBR)
Historical Stock Chart
From Mar 2024 to Apr 2024
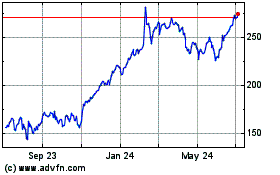
CyberArk Software (NASDAQ:CYBR)
Historical Stock Chart
From Apr 2023 to Apr 2024