Firm Manipulated iPhone Software for Spying, Report Says
August 25 2016 - 3:10PM
Dow Jones News
Security researchers say a little-known Israeli startup
exploited previously unknown bugs in Apple Inc.'s smartphone
software to help foreign governments spy on their citizens.
The researchers say the surveillance software was the work of
NSO Group Technologies Ltd., which sells primarily to government
agencies. The researchers, at Citizen Lab, a group that
investigates surveillance technology, and at mobile-security firm
Lookout Inc., say they discovered the software in a link sent
earlier this month to the phone of Ahmed Mansoor, a human-rights
activist in the United Arab Emirates.
Their report sheds new light on the capabilities of private
security companies to produce sophisticated software for
state-sponsored spying. It also suggests that the iOS operating
system behind Apple's iPhones isn't as impregnable as it appeared
earlier this year, when the Federal Bureau of Investigation
struggled for weeks and ultimately paid $1 million to unlock a
phone tied to the San Bernardino terror attack.
NSO Group's software takes advantage of three previously unknown
flaws in iOS to install itself on an iPhone, where it then
transforms the phone into a surveillance device, tracking its
movements, logging messages and downloading personal data.
In a statement Thursday, Apple said it had been "made aware of
this vulnerability and immediately fixed it." The company advised
iPhone users to download the new version of iOS, dubbed 9.3.5.
Mark Murray, Lookout's vice president of security research, said
the NSO software, called Pegasus, is "the most professional piece
of spyware that I've ever seen." He said the software operates
stealthily, ensuring that it doesn't quickly drain the battery and
speeding up its data transfer when it is on Wi-Fi networks so that
it doesn't get noticed.
An NSO spokesman said the company had no knowledge of Mr.
Mansoor's case. In a statement, the spokesman said, "NSO's mission
is to help make the world a safer place, by providing authorized
governments with technology that helps them combat terror and
crime. The company sells only to authorized governmental agencies,
and fully complies with strict export control laws and
regulations."
The spokesman said NSO doesn't operate its systems, and requires
customers to use them lawfully and only "for the prevention and
investigation of crimes."
NSO has billed itself as a leader in the field of cyberwarfare,
offering tools for governments to keep tabs on criminals and
terrorists who use encrypted communications. The company has been
thought to be capable of installing unauthorized software on
Android, BlackBerry and iPhone devices, but Thursday's report
provides the first in-depth look at its capabilities.
"We're a complete ghost," NSO co-founder Omri Lavie told Defense
News in a 2013 interview. "We're totally transparent to the target,
and we leave no traces."
The Wall Street Journal in 2014 reported that the company had
been acquired by private-equity firm Francisco Partners for $110
million. Francisco Partners had no immediate comment.
Researchers highlighted the unusual way that Pegasus is
installed on a phone, taking advantage of the three flaws in iOS to
silently "jailbreak" the phone and circumvent the requirement that
only Apple-approved software runs on the device. This type of
one-click iPhone attack previously has been described by
researchers but never been seen in a real-world attack, Lookout's
Mr. Murray said.
Mr. Mansoor said he received a text message Aug. 10 from a phone
number he didn't recognize that said, "New secrets about torture of
Emiratis in state prisons." He said his suspicions immediately were
aroused. "I could tell that there was something wrong and I
contacted the Citizen Lab team immediately."
At Citizen Lab, researchers found that the link in Mr. Mansoor's
text message led to a website that they previously had connected to
NSO Group. That website launched the Apple attack and installed the
Pegasus spyware.
Mr. Mansoor previously has been targeted by other forms of
malicious software in 2011 and 2012. The first was built by a
German company called FinFisher GMBH; the 2012 attack was by
Hacking Team S.r.l., an Italian company, according to Citizen Lab,
which part of the University of Toronto's Munk School of Global
Affairs.
Although these products typically are marketed as legitimate
tools sold only to law enforcement, some governments use them to
spy on activists and journalists, said Bill Marczak, a senior
researcher with Citizen Lab.
After the attack on Mr. Mansoor, Citizen Lab linked NSO to 2015
attacks on a Mexican journalist who received text messages that
were similar to Mr. Mansoor's.
Mr. Mansoor believes that he was the target of U.A.E. officials
looking to keep tabs on his online activity.
A U.A.E. official declined to comment.
Write to Robert McMillan at Robert.Mcmillan@wsj.com
(END) Dow Jones Newswires
August 25, 2016 14:55 ET (18:55 GMT)
Copyright (c) 2016 Dow Jones & Company, Inc.
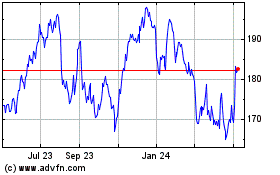
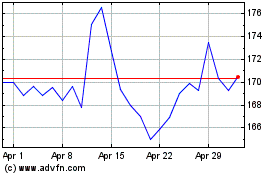
Apple (NASDAQ:AAPL)
Historical Stock Chart
From Mar 2024 to Apr 2024
Apple (NASDAQ:AAPL)
Historical Stock Chart
From Apr 2023 to Apr 2024